What is Active Directory? Complete Guide for IT Pros

Active Directory is Microsoft’s on-premises identity and access management (IAM) service. In this Active Directory tutorial, learn how Active Directory (AD) makes it easier for IT to manage an organization’s IT resources. Active Directory is especially useful for companies that have to manage lots of endpoints and servers.
🎬 Watch This Week in IT.
What is Active Directory and why is it used?
Active Directory is a database from Microsoft that stores information about objects on the network and makes this information easy for administrators and users to find and use. Objects might include user accounts, computer accounts, and resources like file and print servers. Active Directory uses a structured data store as the basis for a logical, hierarchical organization of directory information. Think of it as a telephone directory but for objects, devices, and resources on a network. Or in other words, an identity and access management (IAM) solution.
AD controls much of the activity that goes on in your IT environment. In particular, as an IAM service, it makes sure each person is who they claim to be (authentication), usually by checking the user ID and password they enter and allowing them to access only the data and resources they’re allowed to use (authorization).
What is Active Directory Domain Services?
Active Directory Domain Services (AD DS), is the Server Role in Windows Server that you install if you want to promote the server to a domain controller (DC).
What are domain controllers used for?
DCs host a copy of the AD database and they perform authentication and authorization functions to make resources and data available to network users and administrators. When you install the AD DS Server Role on a server it holds the keys to the kingdom for this instance of the directory service. For example, AD DS stores information about user accounts: such as names, passwords, phone numbers, computers, and other devices like printers and other network resources.
DCs authorize users, which are each assigned a unique security identifier (SID), to access protected information on the network. All other access attempts are blocked. The individual attributes of a user: name, address, location, manager, and so on, are stored in the directory database.
Permissions determine what users can do with the resources on your network. Access tokens are granted every time a user logs on to a domain-joined computer. Those access tokens contain the keys that the user needs to be able to access the resources for which they have been assigned rights to use.
Who is Active Directory for?
AD is for almost any company or organization out there. I have yet to come across an environment that didn’t utilize Active Directory Domain Services. AD simplifies life for administrators and end users while enhancing security for organizations.
Administrators and end users share the centralized user and rights management, as well as centralized control over computer and user configurations through the AD Group Policy feature. Users can authenticate once and then seamlessly access any resources in the domain for which they’re authorized (single sign-on).
Plus, files are stored in a central repository where they can be shared with other users to ease collaboration and backed up properly by IT teams to ensure business continuity.
How Active Directory works
So, what’s at the heart of how this service introduced in Windows 2000 works? Well, Active Directory Domain Services (AD DS) is a part of the Windows Server operating system. The servers that run AD DS are called domain controllers (DCs).
Back in the days of Windows NT Server, there was a specific role, the Primary Domain Controller (PDC), that was specified to hold a lot of the key roles across the domain amongst the other DCs. Today, DCs can hold one of 5 FSMO roles (Flexible Single Master Operations).
Organizations normally have multiple DCs for redundancy, performance, and business continuity. Each one has a copy of the directory for the entire domain. Changes made to the directory on one domain controller — such as password update or the deletion of a user account — are replicated using a replication service to the other DCs so they all stay up to date.
In addition, the schema of the database central to AD DS includes the various attributes each person, group, or computer can hold.
A Global Catalog (GC) server is a domain controller that stores a complete copy of all objects in the directory of its domain and a partial copy of all objects of all other domains in the forest; this enables users and applications to find objects in any domain of their forest.
Desktops, laptops, and other devices running Windows (rather than Windows Server) can be part of an AD environment, but they do not run AD DS.
AD DS relies on several established protocols and standards, including LDAP (Lightweight Directory Access Protocol), Kerberos, and DNS (Domain Name System).
IT admins can use various tools to access AD information, including the Active Directory Users and Computers (ADUC), the AD Administrative Center, as well as AD Sites and Services. I invite you to check my separate post about how to access Active Directory.
It’s important to understand that Active Directory is only for on-premises Microsoft environments. Microsoft environments in the cloud use Azure Active Directory, which serves the same purposes as its on-prem namesake.
AD and Azure AD are separate but can work together to some degree if your organization has both on-premises and cloud IT environments (a hybrid deployment). I’ll give you more on what Azure Active Directory (AAD) is at the end of this post.
Understanding the structure of Active Directory Domain Services
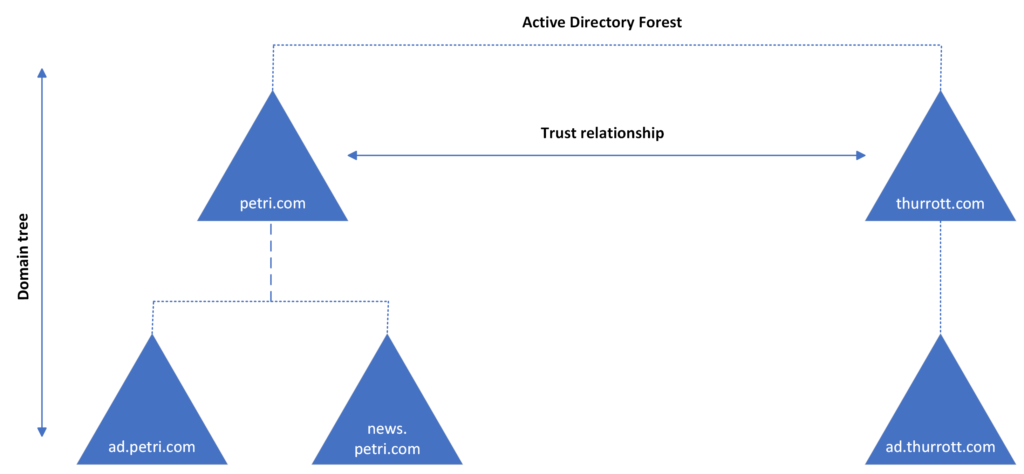
There are three core logical structures to AD DS. They are domains, trees, and forests. A domain is a group of related users, computers, and other AD objects, such as all the AD objects for your company’s various headquarters and branch offices. Multiple domains can be combined into a tree, and multiple trees can be grouped into a forest.
Keep in mind that a domain is a management boundary. The objects for a given domain are stored in a single database and can be managed together. A forest is a security boundary. Objects in different forests are not able to interact with each other unless the administrators of each forest create a trust between them.
For instance, if you have multiple disjointed business units, it’s likely to assist you with managing them if you create multiple forests.
|
Domains |
Domains represent an administrative boundary in your structure for users, groups, computers, and Organizational Units. AD domains can also have sub-domains, creating a tree-like structure. |
|
Trees |
Domains can be structured like a tree with branches. Much like domain names can be structured. For instance, petri.com, ad.petri.com, news.ad.petri.com, and so on. |
|
Forests |
AD forests represent a security boundary. A forest can contain a single domain or a group of domain trees. Each AD forest shares a Global Catalog and database schema. |
|
Organizational Units (OUs) |
OUs can be used to create administrative divisions in a domain. For instance, you could create an OU where only a certain group of users are allowed to reset passwords. Or apply a Group Policy Object (GPO) to computer accounts in each OU. |
|
Containers |
Like OUs, containers are built-in objects that group other AD objects. But it is not possible to link GPOs to containers. |
Below is a visual representation of an Active Directory forest with two domain trees and a disjointed DNS namespace.
What about other Active Directory services?
So, is Active Directory simply AD DS? Nope. There are a few other software features that make up the whole of AD. The most common one after AD DS is Active Directory Federation Services (AD FS).
Active Directory Federation Service (AD FS) enables Federated Identity and Access Management (IAM) by securely sharing digital identity and entitlements rights across security and enterprise boundaries.
AD FS extends the ability to use single sign-on functionality that is available within a single security or enterprise boundary to Internet-facing applications to enable customers, partners, and suppliers a streamlined user experience while accessing the web-based applications of an organization.
Starting in Windows Server 2012 R2, AD FS included a federation service role service that acts as an identity provider (authenticates users to provide security tokens to applications that trust AD FS) or as a federation provider (consumes tokens from other identity providers and then provides security tokens to applications that trust AD FS).
The other main services include:
- Active Directory Lightweight Directory Services (LDAP) – a light-weight instance of Active Directory that can be used for apps that need a directory service.
- Active Directory Certificate Services (AD CS) – manages and issues digital certificates to users and computers.
- Active Directory Rights Management Services (AD RMS) – lets organizations granularly control how documents are used by entities that have access.
- Active Directory Federation Services (AD FS) – used for enabling access and management between enterprises.
How Active Directory helps IT
There are several benefits for IT folk in using AD DS in your organization:
- You can choose how to organize your data across the various teams of users and roles in your organization.
- You can manage AD DS from any computer on the network, if necessary.
- AD DS provides built-in replication and redundancy: if one domain controller (DC) fails, another DC picks up the load.
- All access to network resources goes through AD DS, which keeps network access rights management centralized.
The largest benefit of implementing Active Directory for your users is a centralized token to log in to their computer. Instead of needing this user account to access the resources on this server, and another for server two, and so on, you can grant tokens to a single account that a user can use to seamlessly access resources and printers across the enterprise.
Active Directory vs LDAP or NIS
We already explained what Active Directory is above. But, what about LDAP and NIS? What are they, how are they different?
The Network Information Service or NIS (originally called Yellow Pages or YP) is Sun Microsystems client-server Directory Service protocol for distributed system configuration data such as user and host names between computers on a computer network. NIS is a discovery mechanism.
What is LDAP? Companies store usernames, passwords, email addresses, printer connections, and other static data within directories. LDAP is an open, vendor-neutral application protocol for accessing and maintaining that data. LDAP can also utilize authentication, so users can sign on just once and access many different files on the server (SSO). You can learn more about the differences between LDAP, OpenLDAP, and Active Directory here.
Windows Server Active Directory vs Azure Active Directory
Azure Active Directory (Azure AD, or AAD) is the next evolution of identity and access management solutions for the cloud. As I stated at the top of this post, Microsoft introduced Active Directory Domain Services in Windows 2000 to give organizations the ability to manage multiple on-premises infrastructure components and systems using a single identity per user.
Azure AD takes this approach to the next level by providing organizations with an Identity as a Service (IDaaS) solution for all their apps across cloud and on-premises.
Next generation Active Directory – what’s new in Windows Server 2025?
Active Directory remains a critical tool for large organizations, providing essential on-premises services, along with authorization and authentication mechanisms. However, vulnerabilities have been a longstanding issue, prompting Microsoft to enhance AD’s robustness in Windows Server 2025, particularly in terms of security.
LDAP and Kerberos improvements
In the Windows Server 2025 release of Active Directory, Microsoft is introducing a suite of security improvements aimed at addressing known vulnerabilities. Among the most notable enhancements are LDAP support for TLS 1.3, bolstering security for confidential attributes, and setting encryption as the default for LDAP communications. Furthermore, the update brings new encryption standards to Kerberos, including support for AES and SHA256/384, and it revises the default behavior for legacy SAM RPC password change methods to enhance security. Additionally, the update enhances Kerberos and PKINT for greater cryptographic agility.
NTLM authentication deprecation
In a move to phase out legacy authentication protocols, Microsoft has targeted NTLM authentication for deprecation, recognizing its security shortcomings and the preference for Kerberos as the primary authentication protocol within AD. Windows 11 will introduce a Kerberos Key Distribution Center (KDC), traditionally only found on domain controllers, to allow local account authentication on Windows PCs via Kerberos for the first time. This signifies a major advancement, making KDC functionality available across all Windows versions. Moreover, the introduction of IAKerb, a set of extensions to the Kerberos standard, facilitates authentication without direct domain controller connectivity, effectively acting as a proxy technology for remote authentication scenarios.
Database performance
The update also promises performance enhancements for Active Directory. These include an upgraded database architecture utilizing a 32k page size, enabling support for longer multi-value attributes and addressing performance bottlenecks. AD will now fully leverage multicore CPUs, enhancing its processing capabilities.
Administrators gain more control over replication priorities, allowing for more efficient domain controller replication management. Additionally, three new performance counters are introduced, offering deeper insights into AD’s operational metrics. These advancements collectively aim to improve the efficiency and reliability of Active Directory, ensuring it remains a pivotal component of modern IT infrastructures.
Feel free to read our separate post about Active Directory, Azure Active Directory, and other identity providers to see all the core differences between AD and AAD and how managing them differs. Plus, there are several articles on Petri that contain step-by-step tutorials on how to install AD in your environment if you want to learn more.
FAQs
How do I create and manage Active Directory groups?
You can create and manage groups through the Active Directory Administrative Center. Navigate to the Groups container, right-click, select ‘New Group,’ specify the group scope (Domain Local, Global, or Universal), and set the group type (Security or Distribution). You can then add members and assign permissions accordingly.
What are the best practices for Active Directory password policies?
Implement complex passwords with minimum 14 characters, enable password history, set maximum password age to 90 days, and configure account lockout policies. Use Fine-Grained Password Policies for different user groups and regularly audit password settings using built-in tools.
How do I set up Active Directory site links and replication?
Configure site links through the Sites and Services console. Create sites based on physical locations, establish site links with appropriate cost values, set replication schedules, and monitor replication health using repadmin commands or the Active Directory Replication Status Tool.
What backup strategies does this Active Directory tutorial recommend?
Implement System State backups daily, maintain multiple backup copies across different locations, use Windows Server Backup or third-party tools, and regularly test restore procedures in a lab environment to ensure business continuity.
How do I troubleshoot common Active Directory authentication issues?
Start by checking the Event Viewer logs, verify DNS settings, ensure time synchronization between domain controllers, use tools like dcdiag and netdiag for diagnostics, and validate Kerberos ticket granting services are functioning correctly.





