Blog

The “No-Breach” Breach: How Stealer Logs Lead to Active Directory Incidents
- May 11, 2026
-
A 2026 Forbes article reported that the previous year’s credential-theft wave exposed 2.86 billion compromised credentials, with infostealers tied to roughly 3.9 million infected machines and 347.5 million stolen logins; business cloud and authentication services accounted for more than 30% of targeted data, while sensitive corporate access points such as Active Directory/ADFS and RDP frequently…

Microsoft Security Without a Rulebook: The Problem with “Require Compliant Device”
- May 08, 2026
-
Microsoft is increasingly making security‑critical decisions on behalf of organizations and not through policy, but through defaults. The “Require compliant device or hybrid-joined device” Conditional Access template is one of the clearest examples of security without a rulebook. The no-brainer policy that gets complicated fast Microsoft’s Require compliant or hybrid-joined device Conditional Access (CA) template seems like…

Azure Arc-Enabled Kubernetes Adds Cert-Manager for TLS Certificate Automation
- May 07, 2026
-

Microsoft has announced the public preview of cert-manager support for Azure Arc-enabled Kubernetes. This new feature simplifies security by streamlining certificate issuance, renewal, and trust management across distributed Kubernetes clusters, which reduces manual effort and improves reliability. According to Microsoft, managing TLS certificates in Kubernetes (especially across hybrid, multicloud, and edge environments) has become increasingly…

Poor Employee Awareness and Skills Gap Drive Cybersecurity Breaches
- May 07, 2026
-

A major driver of cybersecurity breaches continues to be insufficient employee training and awareness, a problem that has persisted across the industry for years. New findings from Fortinet highlight that despite advancing technologies, organizations still struggle to address this ongoing human-factor vulnerability. According to Fortinet’s 2026 Global Cybersecurity Skills Gap Report, more than half of…

Microsoft Azure Local Now Supports Thousands of Servers in Sovereign Deployments
- May 06, 2026
-

Microsoft’s Azure Local can now support deployments of thousands of servers within a single sovereign environment. This allows organizations to run very large, complex workloads locally without redesigning their infrastructure. According to Microsoft, governments and regulated industries are increasingly prioritizing strict control over where their data is stored, how operations are managed, and how compliance…

Attackers Extract Microsoft Edge Passwords From Memory Using Legitimate Remote Access Tools
- May 06, 2026
-

An attacker who has administrative-level access can retrieve Microsoft Edge users’ saved passwords from memory, even when those credentials are not actively being used. This is possible because the browser temporarily keeps them in an unencrypted form in its process memory as part of how it is designed. According to a new report from Securonix,…

Why Windows Co-Management Is Becoming a Smarter Path for Enterprise IT
- May 06, 2026
-
It isn’t hard to guess why Microsoft Intune is a common first choice for Windows device management. For enterprises already using Microsoft 365 and Entra ID, it offered a logical way to extend modern management to Windows devices while keeping administration aligned with the broader Microsoft ecosystem. But as device estates grow and operational demands…

Millions of Internet‑Exposed RDP and VNC Servers Threaten Critical Systems
- May 05, 2026
-

RDP vulnerabilities have become a critical but often overlooked risk for organizations worldwide, which leaves many systems unknowingly exposed. Cyber attackers are increasingly exploiting these gaps by using unsecured servers as easy entry points into enterprise networks. According to a new report from Forescout Vedere Labs, millions of RDP and VNC servers are publicly accessible…

Active Directory DNS: Why It’s Required and How It Actually Works
- May 05, 2026
-
Active Directory DNS is used to locate domain controllers and critical services (LDAP, Kerberos, and the Global Catalog) via SRV and host records. If DNS is missing or misconfigured, common outcomes include failed logons, Group Policy errors, and domain controller replication issues. This article explains how and why Active Directory depends on DNS, with practical…

Why Over‑Privileged Apps Are One of the Most Dangerous Attack Paths in Microsoft Entra
- May 05, 2026
-
 Russell Smith
Russell Smith
“Applications can be incredibly powerful. If you own the application, you can act as that application. And if that application is highly privileged, you could effectively become a global admin without ever being in that group.” Nicolas Blank, Identity Architect, Microsoft MVP, and CTO of NBConsult In Microsoft Entra, being an application owner can be…
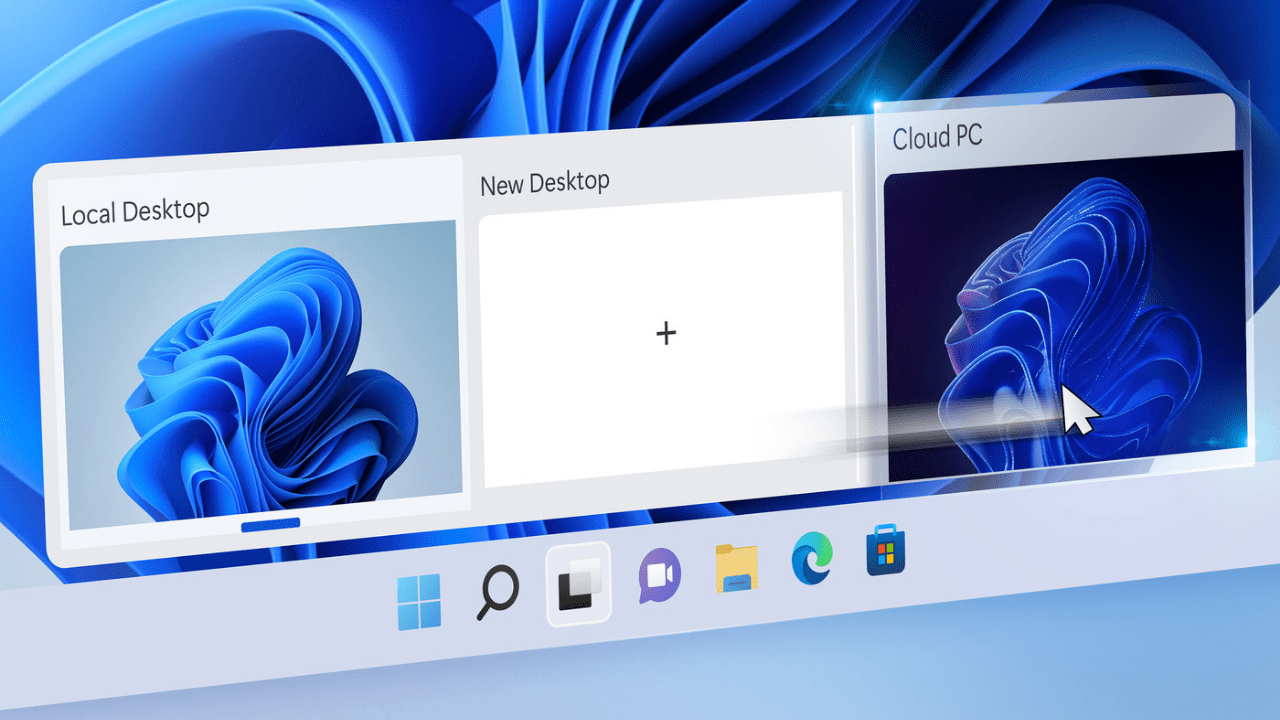
Microsoft Previews User‑Initiated Provisioning for Windows 365 Reserve
- May 04, 2026
-

Microsoft has introduced a public preview of user-initiated provisioning for Windows 365 Reserve. The feature enables selected users to spin up their own Reserve Cloud PC on demand, reducing reliance on IT administrators and minimizing downtime. Windows 365 Reserve is a cloud‑based service that provides employees with a temporary, fully configured virtual Windows PC when…

Microsoft Intune Adds Real‑Time App Inventory, Linux SSO Enhancements
- May 04, 2026
-

Microsoft is rolling out a series of enhancements to Microsoft Intune, targeting deeper visibility and tighter control across modern endpoints. This month’s updates span improved Windows app inventory, a more secure Linux SSO experience, and expanded enrollment and management capabilities for Apple devices. Microsoft has added new enhanced app inventory capabilities in the “All Apps”…



