Microsoft Blocks Unmanaged Azure AD Guest Accounts

Microsoft has released an update that blocks the use of unmanaged Azure AD accounts in organizations. The company has provided a set of tools to help IT admins find existing unmanaged accounts and reset their redemption status.
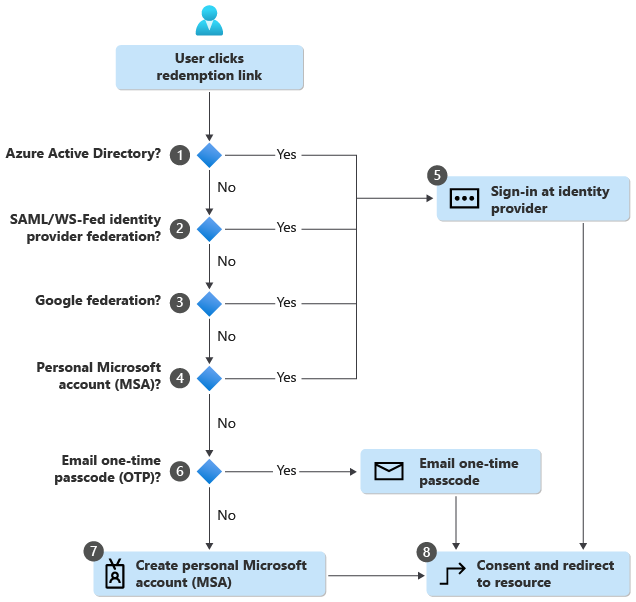
In 2016, Microsoft introduced a self-service sign-up feature that allowed external users to sign up as guest members in managed tenants based on their email domain. This capability made it easier for guest users to access resources without an Azure AD-based identity. At the same time, it created compliance issues for several customers.
“However, this sometimes means that users would create accounts in a tenant not managed by the IT department of their organization. This has several unintended consequences such as challenges with user lifecycle management, support costs due to password reset issues and information disclosure between users in the Azure Portal,” the company explained.
Starting this month, it’s no longer possible to create unmanaged Azure AD guest accounts. Microsoft has released some tools to help admins detect and clean up such accounts in their tenants. The unmanaged accounts will continue to work, but will be configured to use alternative sign-up methods such as Google federation or One-Time Passcode (OTP).
Microsoft releases Azure Multifactor Authentication (MFA) Server Migration Utility
Additionally, Microsoft has released a new Azure Multifactor Authentication (MFA) Server Migration Utility for enterprise customers. The service lets administrators migrate MFA settings for users from the on-premises Azure Server to Azure AD MFA. It enables them to complete the MFA process without re-enrolling users after switching to the Azure MFA service.
Microsoft says that staged migration lets organizations test the changes with select users without changing domain federation settings. Keep in mind that the staged rollout can target up to 500,000 users. You can learn more about the MFA Server Migration Utility on this support page.