Why Microsoft Intune Belongs in the Tier 0 Identity Control Plane
The answer is impact, and Intune delivers it at scale.

On March 18, 2026, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued an alert urging organizations to harden Microsoft Intune and other endpoint management systems after a cyberattack used legitimate management features, rather than malware, to cause widespread disruption.
That should change how we classify Intune. When a single control plane can push code, change configurations, or wipe devices at enterprise scale, it stops being “just endpoint management” and starts behaving like critical infrastructure.
So why should it admins treat Microsoft Intune like Tier 0?
The answer is impact, and Intune delivers it at scale.
Intune is often looked at as an endpoint management solution, which it is by default. But if we look at the scale and reach Intune has in an organization, it behaves like the identity control plane.
Enrollment, compliance, and device health signals feed Conditional Access decisions in Microsoft Entra ID, governing access to Microsoft 365 and other Software-as-a-Service (SaaS) apps. In simple terms, identity and device management are connected and form a control loop that amplifies the blast radius of a single privileged identity.
If an attacker gets Intune Administrator (or any role with broad device and policy control), they don’t need custom malware to create an outage: they can push a “legitimate” configuration change that breaks VPN or Wi‑Fi, deploy a script that disables security tooling, flip compliance so healthy devices become noncompliant, and then let Conditional Access lock users out, while they simultaneously wipe or retire targeted endpoints to slow down recovery.
The identity to Intune control loop and why it matters
Intune does not function alone. Entra ID plays a crucial role and determines:
- Who can administer Intune
- Which roles are assigned
- How admins authenticate
- Conditional Access
Intune then uses that to determine:
- Device enrollment state and availability
- Device compliance
- Which actions an administrator can take
- How device state influences Conditional Access (allow, block, or require remediation)
This tight coupling puts Intune squarely in the middle of the access decision process and is now part of the identity ecosystem.
This is why Intune needs stronger governance than many organizations apply today and requires the same mindset of managing the Tier 0 control plane.
CISA alert in response to endpoint management
On March 18, 2026, CISA put out an alert urging organizations using Microsoft Intune and other endpoint management platforms to harden administrative controls by applying several key practices:
- Use principles of least privilege when designing administrative roles, leverage Intune role-based access control to limit what actions admins can take and which users and devices those actions apply.
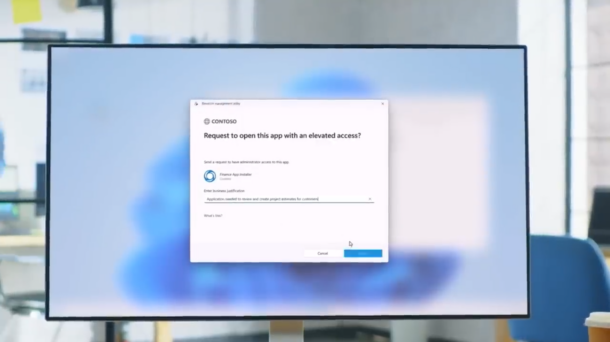
- Require Multi-Admin Approval for sensitive or high-impact actions, including device wipes, application and script changes, role modification, and configuration updates.
These recommendations are critical and must be considered as part of your baseline for securing Intune environments. However, they focus on hardening administrative access. They do not fully address a broader architecture reality: Microsoft Intune now functions as part of the identity control plane and must be designed, governed, and monitored the same way as Identity.
Architecting Intune for Tier 0
Unfortunately, there is not a single switch you can turn on to enable Tier 0 protection. Tier 0 is a set of design choices that when implemented together reduce the blast radius, add additional barriers to reversible actions, and increase the odds of early detection. Sound familiar; these are the same principles that apply to designing Tier 0 for the identity control plane.
1. Limit who can make high-impact changes
There is no need to reinvent the wheel with this design decision, to keep it simple start with role hygiene.
Broad permissions and too many admins create the perfect attack surface.
Reduce the use of broad permissions and the number of admins in roles that have influence over high-impact changes.
Practical actions you can apply today:
- Review your existing Intune roles and scope them into real admin responsibilities
- Remove tenant-wide permissions from daily admin use
- Minimize the number of accounts that can perform destructive device actions
2. Separate destructive actions from day-to-day administration
Certain admin tasks pose a greater risk to the organization, and they need to be tightly controlled.
Day-to-day work like policy tuning, app deployment, and compliance adjustments must not be coupled with destructive actions such as wipe, retire, or delete. Separate these into a dedicated, tightly controlled role or workflow that is only used when required.
This design decision aligns with how Multi-Admin Approval works in Intune. Critical actions are gated behind an additional approver.
3. Avoid “All users” and “All devices” for risky assignments
Global targeting sounds easy and the most efficient way to manage, but one bad change can turn into a catastrophic event.
If a high-impact policy, script, or app deployment is assigned to “All users” or “All devices” mistakes propagate instantly. A safer approach is staged rollout:
- Use segmented groups and filters
- Target a pilot ring
- Expand in phases
- Collect feedback, deploy to the rest of the population when change is determined to be safe.
It may seem like a lot of administrative overhead, but this is operational discipline.
4. Enforce phishing-resistant MFA
Basic multifactor authentication (MFA) is no longer sufficient for Tier 0 systems. Phishing-resistant authentication must be enforced for any role that can issue high-impact Intune actions.
5. Monitor Intune and Identity events together
As mentioned, Intune and Entra ID are tightly coupled and form a control loop for access this why your monitoring should be too. Key signals you should track:
- Policy edits
- Role changes
- App deployments
- Compliance updates
- Conditional Access Policy updates
- New privileged user creations
- Authentication-method changes
- Bulk wipe or reset actions
These signals could be early warning signs that are larger incident is about to occur. If they are monitored separately, you are more likely to correlate the chain of actions and miss an enterprise-wide attack.
Tier 0 quick checklist
- Ring-fence admin access: separate day-to-day Intune administration from destructive actions (wipe/retire/delete) and make those accounts rare and tightly controlled.
- Turn on friction for high-impact changes: require Multi-Admin Approval for wipes, scripts, app changes, role modifications, and configuration updates.
- Stop global targeting by default: use pilot rings, scoped groups, and filters instead of “All users” / “All devices” for anything risky.
- Enforce phishing-resistant MFA: protect Intune admins the same way you protect identity admins.
- Monitor the control loop: correlate Intune change events with Entra ID sign-ins, role changes, and Conditional Access updates.
Treating Microsoft Intune as Tier 0 does not mean turning on every available control or rebuilding your environment from scratch. It means recognizing that Intune now operates as part of the identity control plane and designing it accordingly. When a platform can enforce policy, remove access, and disrupt operations at enterprise scale using legitimate administrative actions, it deserves the same architectural discipline applied to identity systems.
The CISA alert underscores how quickly endpoint management platforms can become force multipliers for attackers when administrative access is abused. Hardening steps such as least privilege, Multi‑Admin Approval, and strong authentication are essential baselines. Architecting Intune as Tier 0 goes further by limiting blast radius, separating authority, and ensuring high‑impact actions are visible in context with identity activity.
The goal of Tier 0 is not only to eliminate risk but more importantly to control the blast radius when risk occurs. That is the difference between securing Intune as a tool and designing it as Tier 0 infrastructure.
Start here: reduce Intune blast radius
If Intune can change configuration, enforce access, and wipe devices at enterprise scale, it deserves Tier 0 operational discipline. Pick one step below and start this week:
- Run a Tier 0 review: list every Intune admin role assignment, remove broad roles, and scope what remains.
- Enable Multi-Admin Approval: start with wipes and role changes, then expand to scripts/apps/config.
- Create a safe rollout pattern: define pilot rings and a “no global targeting” rule for high-impact policies.
- Validate monitoring: confirm your SOC can detect role changes + bulk device actions + suspicious admin sign-ins as one storyline.