Microsoft Adds Authentication Strength Support to Conditional Access Policies

Microsoft has released a new setting for conditional access policies that enables organizations to define the authentication strength of accepted connections. This release brings the ability to specify a combination of multifactor authentication (MFA) methods that allow external users to access a particular resource.
Conditional access policies let IT admins create a set of rules and configurations that control how a user gets access to the requested resources. These policies leverage contextual information to determine the risk level and apply the most appropriate level of security to each login attempt.
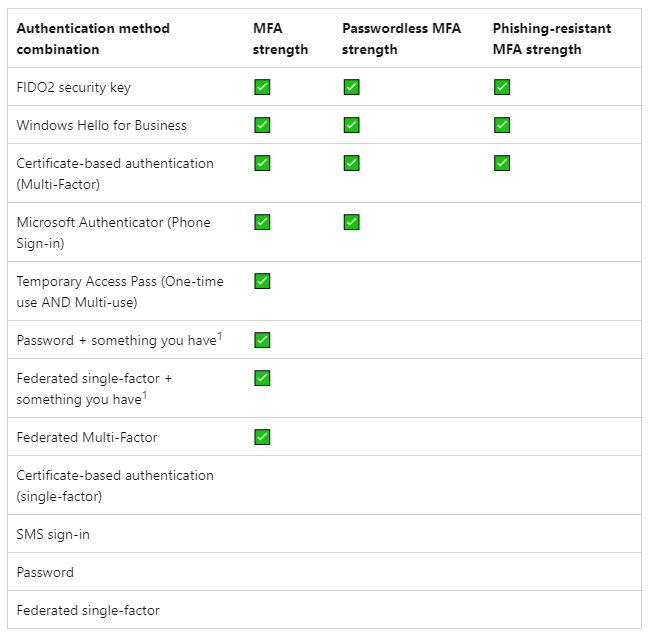
According to Microsoft, the new authentication strength feature helps administrators to restrict external access to sensitive Microsoft 365 apps in enterprise environments. Azure Active Directory (AD) currently offers three types of built-in authentication strengths. These include Multifactor authentication strength, phishing-resistant MFA strength, and passwordless MFA strength. Moreover, it is possible to create custom authentication strengths based on specific requirements.
“Authentication strength is based on the Authentication methods policy, where administrators can scope authentication methods for specific users and groups to be used across Azure Active Directory (Azure AD) federated applications. Authentication strength allows further control over the usage of these methods based upon specific scenarios such as sensitive resource access, user risk, location, and more,” the company explained.
How to choose an authentication strength
To choose an authentication strength, IT admins will first need to sign in to the Azure portal. Navigate to Azure Active Directory >> Security >> Authentication methods >> Authentication strengths (Preview). Select any built-in authentication strength type or create up to 15 custom authentication strengths depending on your needs.
Microsoft explained that the new authentication strength feature should help organizations to address specific scenarios. For instance, specific authentication methods are required to access a sensitive resource or perform a sensitive operation within an app. However, keep in mind that authentication strength doesn’t support some authentication methods, such as Email one-time pass (Guest) and Hardware-based OATH token.