Microsoft Advises Customers to Patch Active Directory Privilege Escalation Vulnerability
Last month, Microsoft released the November Patch Tuesday updates to address two Active Directory (AD) Domain Services privilege escalation security flaws affecting all supported versions of Windows Server. But it looks like some customers have not updated their servers yet. The company published a blog post yesterday advising customers to install the emergency fixes on unpatched domain controllers (DC) as soon as possible.
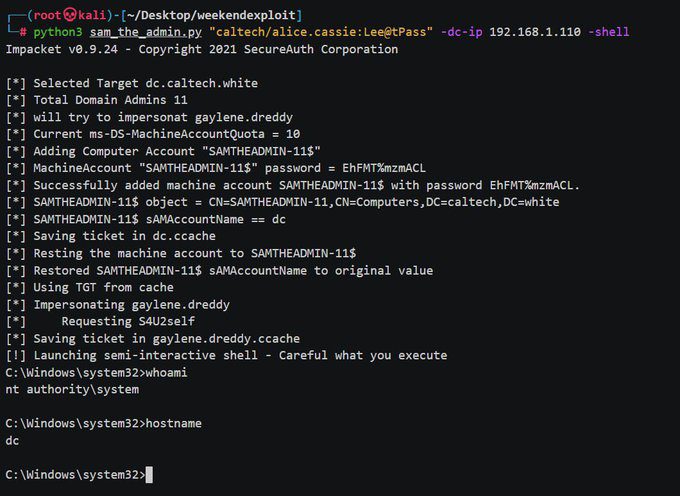
The Active Directory security flaws, tracked under the identifiers CVE-2021-42287 and CVE-2021-42278, were actually discovered last month by Andrew Bartlett, a security researcher at Catalyst IT Limited. Microsoft has acknowledged that both vulnerabilities enable attackers to easily get Domain Admin privileges in Active Directory by impersonating domain controllers.
“When combining these two vulnerabilities, an attacker can create a straightforward path to a Domain Admin user in an Active Directory environment that hasn’t applied these new updates. This escalation attack allows attackers to easily elevate their privilege to that of a Domain Admin once they compromise a regular user in the domain,” Microsoft explained in its Security Advisory. “As always, we strongly advise deploying the latest patches on the domain controllers as soon as possible.”
Apply November 9th Patch Tuesday updates as soon as possible to Active Directory domain controllers
Microsoft is recommending its customers to immediately apply the latest security updates (released on November 9, 2021) as soon as possible as the Windows Active Directory Domain Services privilege escalation vulnerability is actively being exploited by threat actors.
Meanwhile, the Redmond giant has detailed a step-by-step guide to help IT admins identify potentially compromised servers in their organizations. Windows admins are also advised to use the Microsoft Defender for Identity advanced hunting queries to detect abnormal changes in the device name.