Petri Webinars
Browse the Petri.com Knowledge Center below and get access to years of webinars, whitepapers, ebooks, thought leadership articles, conference sessions, and more!
The Good, The Bad, and The Ugly of Office 365 Tenant Migrations
Performing an Office 365 tenant to tenant migration is a little like moving house – especially when the panic sets in as you realize how much you have to move, and how large or unwieldy some of it is. Some workloads are relatively easy to migrate (the good), while others are more complex (the bad),…
Expert Roundtable: Trials and Tribulations of Office 365 Tenant Migrations
Whether the result of a Merger, Acquisition, or Divesture, or as part of org-wide IT consolidation, Office 365 tenant migrations require expert planning and execution. As the platform becomes ever more ubiquitous, the need to perform complex tenant migrations increases, but expertise is in short supply and the “Gotchas!” can easily trip you up. To…
Securing Active Directory – Proactively Detecting Attacks and Attack Pathways | Dec. 08 at 2 PM GMT
Active Directory is seasoned and well known. Unfortunately, the security set at install 15 years ago has not been checked or fixed. However, the attackers are using these attack pathways to move laterally and gain privileged access in AD. In order to fix these misconfigurations, today and tomorrow, a different tactic is required! The fact…
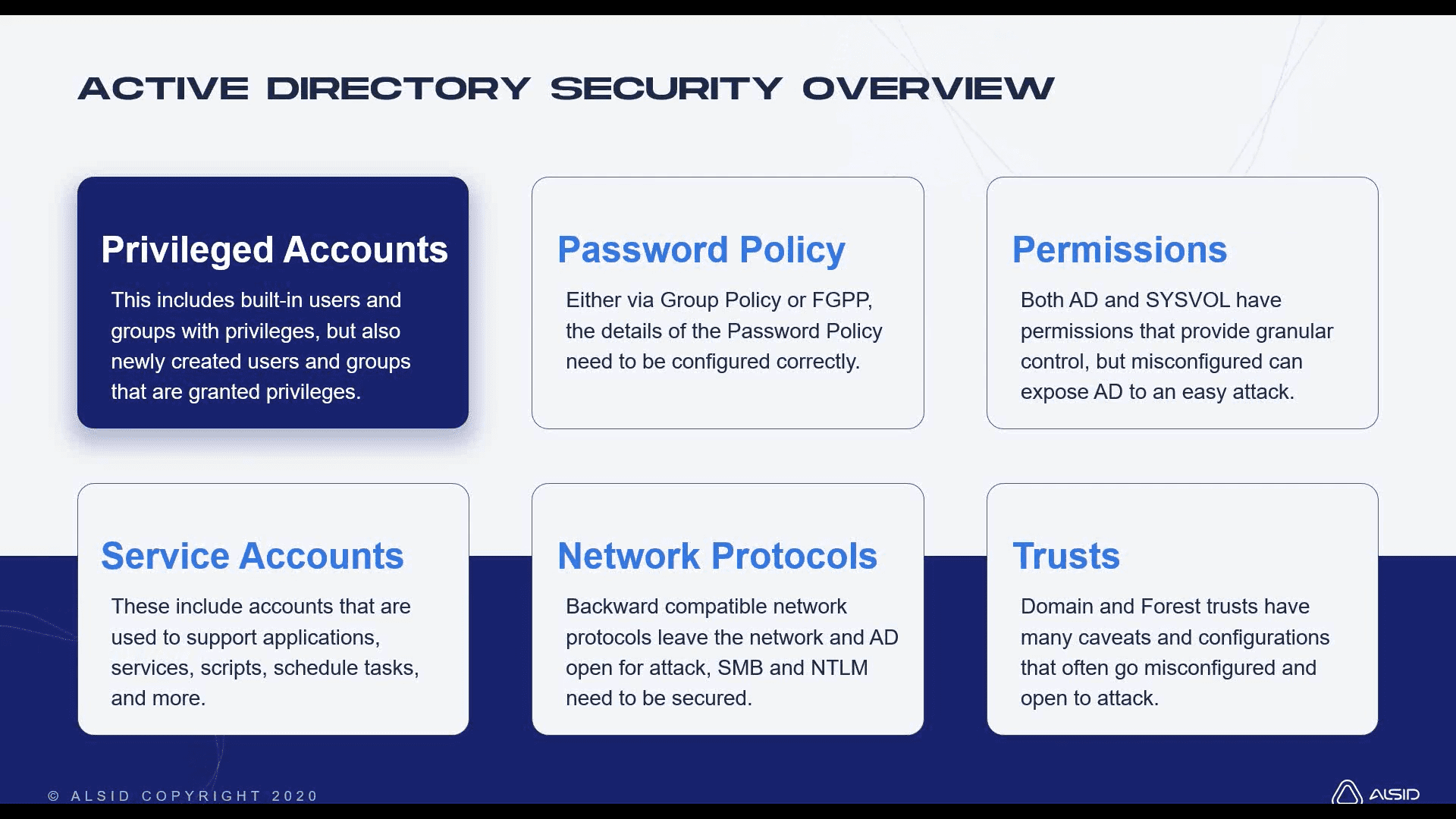
The 4 Pillars of Active Directory Security
Often organizations obtain a few Active Directory security-related tools, but there are always gaps. It is these gaps that the attackers are investigating and exploiting. If the same tools allow the same gaps each time, it only makes sense to fill the gaps, which will stop the attacks. In this session, 16X MVP Derek Melber…

What IT Pros Need to Know About Microsoft’s Windows 11
Later this year, Microsoft will be releasing Windows 11, its “next-generation” installment of Windows that brings with it a new user interface, a revised servicing and update model, as well as new baseline requirements for hardware minimum specs. The minimum hardware specification for Windows 11 requires the latest generation processors, recently released hardware and associated…

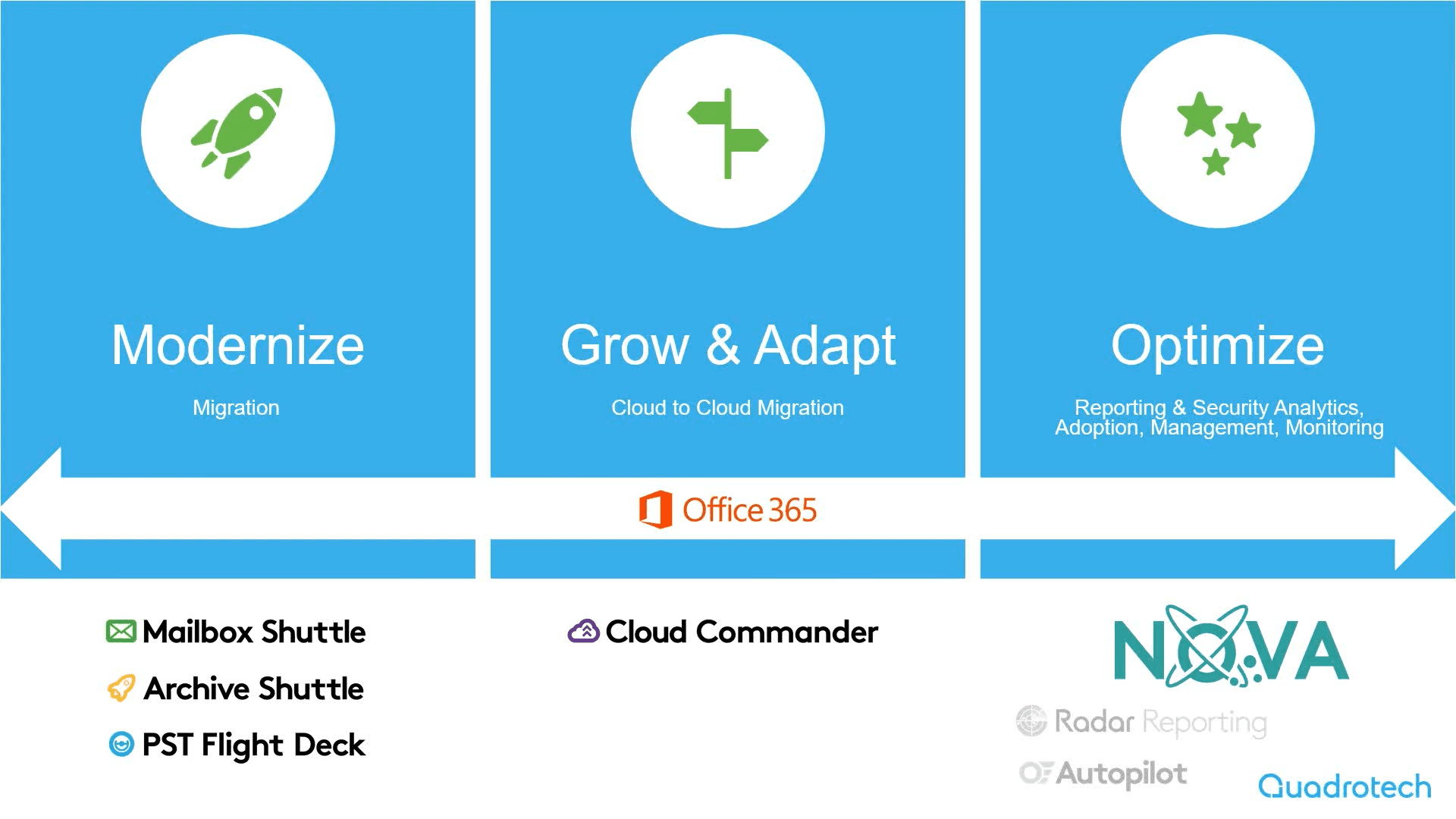
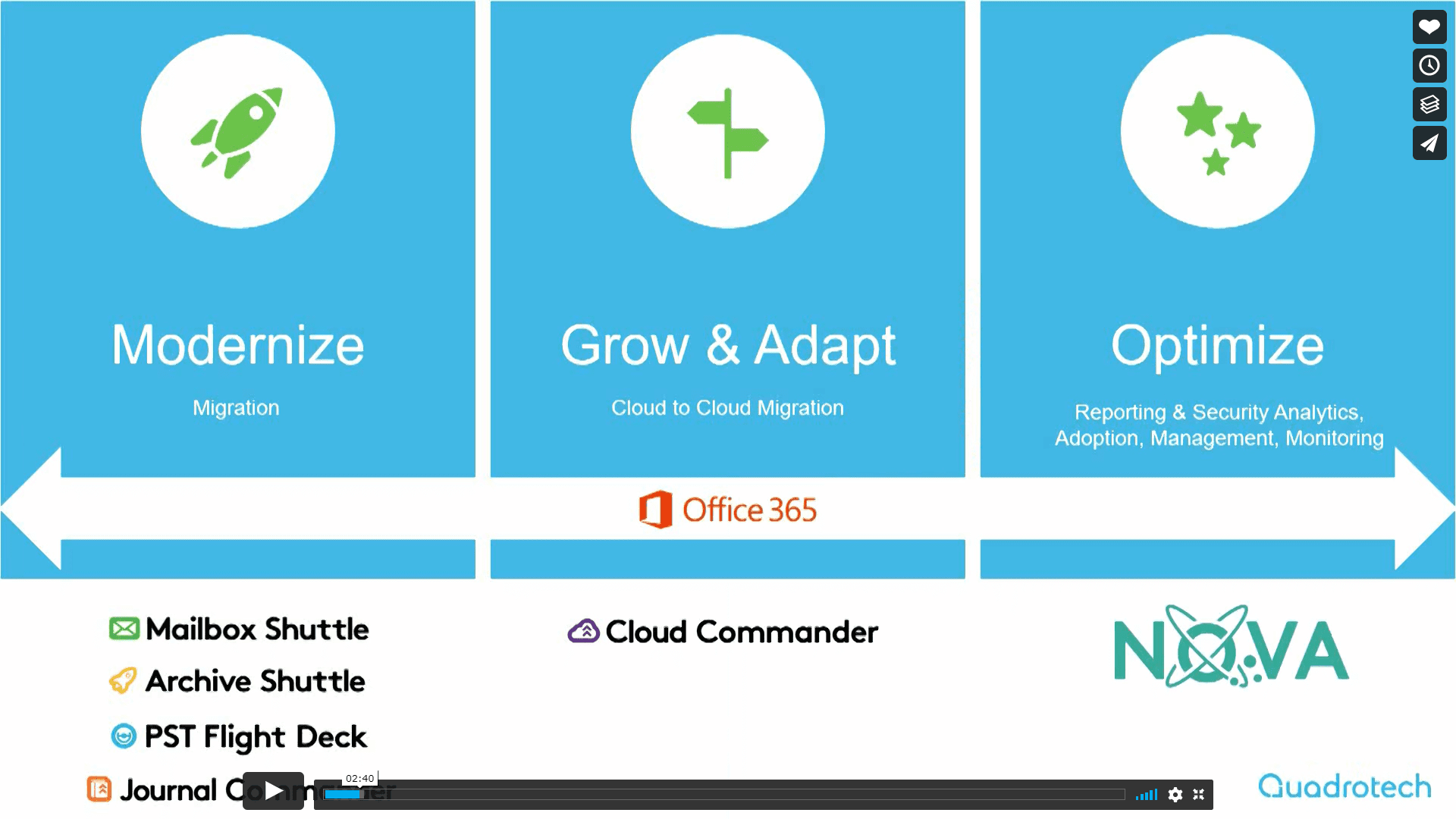
What You Need to Know to Migrate Your Office 365 Tenant Successfully
As we slowly return to a post-pandemic environment, M&A activity has been on the rise as companies look to expand their solutions and refine their operations. But with M&A activity, how do you keep your users collaborating and working without disruption and get the migration done within leadership expectations? And it’s not only M&A activity,…
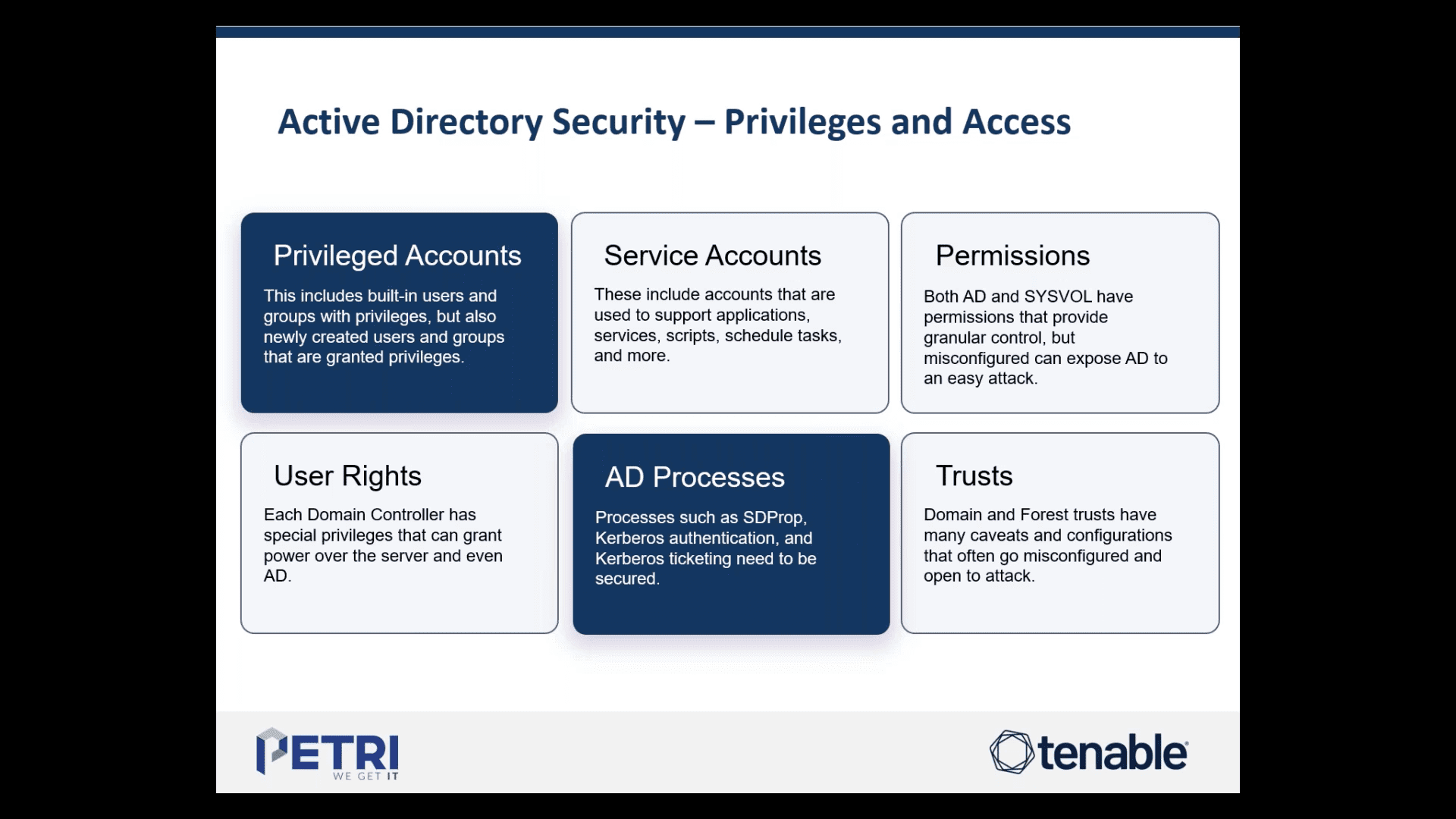
Active Directory Security: What Needs Immediate Priority!
The need to secure Active Directory is no longer an option, but a mandate. Attacks on Active Directory are at an all-time high. Companies that are not taking heed are being punished, both monetarily and with loss of production. Security starts at securing what you have in place, as well as knowing about new attack…
Office 365 Coexistence for Mergers & Acquisitions: Don’t Panic! Make it Simple
The early days – or even early hours – of an M&A announcement can cause anxiety and stress for Office 365 administrators. Common activities need to be repeated in the early stages, but these steps often come with unnecessary complexity. In this session, Microsoft MVPs Steve Goodman and Mike Weaver, will cover the four most…

Active Directory Masterclass: AD Configuration Strategies for Stronger Security
Active Directory (AD) is leveraged by over 90% of enterprises worldwide as the authentication and authorization hub of their IT infrastructure—but its inherent complexity leaves it prone to misconfigurations that can allow attackers to slip into your network and wreak havoc. To reduce risk, you need to ensure your AD is clean, configured properly, monitored…
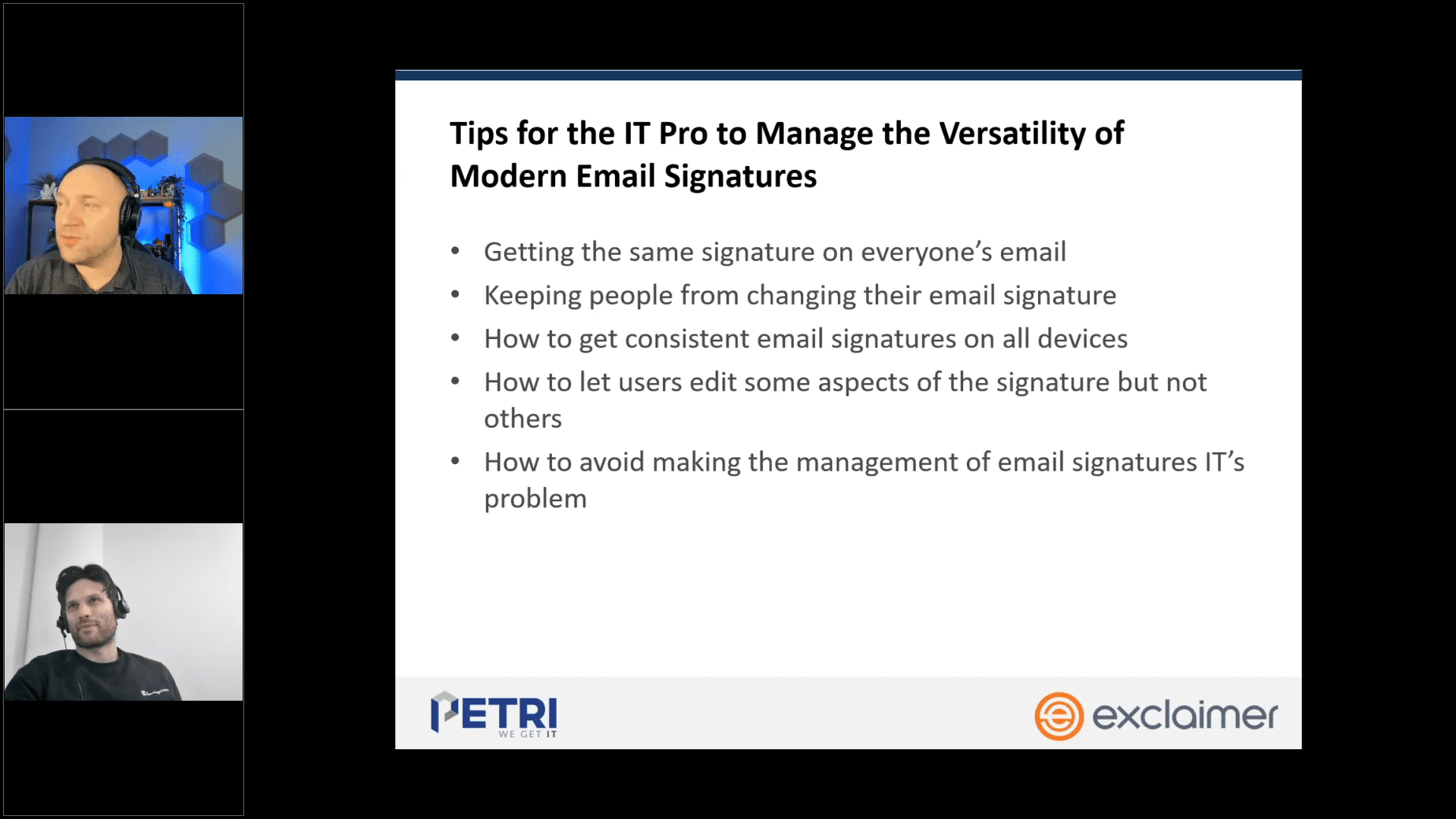
Tips to Standardize and Manage Modern Email Signatures
Microsoft 365 and Microsoft Exchange, or email clients such as Outlook, typically include basic features for adding an email signature to messages. Whether you are the lone IT person battling all odds or the head of IT that overlooks where resources should be allocated, you will encounter significant limitations if you choose to manage email…


