Patch Tuesday March 2018
This month, Microsoft patches a remote code execution vulnerability for CredSSP, helps Intel distribute microcode updates to protect against Spectre Variant 2, and Office 2016 gets updated to version 1803.
This month’s cumulative update for Windows 1709 64-bit patches twenty-four vulnerabilities in total. Fourteen of which are information disclosure, six privilege elevation, two security feature bypass, one denial of service, and one remote code execution vulnerability. Of particular interest is the remote code execution vulnerability CVE-2018-0886, which affects all supported versions of Windows.
Remote code execution vulnerabilities are especially important to patch because they can be exploited from a remote computer that has access to your network. The vulnerability is in the Credential Security Support Provider (CredSSP) protocol and could allow an attacker to relay credentials to run code on a remote system. CredSSP is used by WinRM and the Remote Desktop Protocol (RDP). In a worst-case scenario, the vulnerability could provide access a domain controller (DC) if an administrator initiates a session to a DC using Remote Desktop.
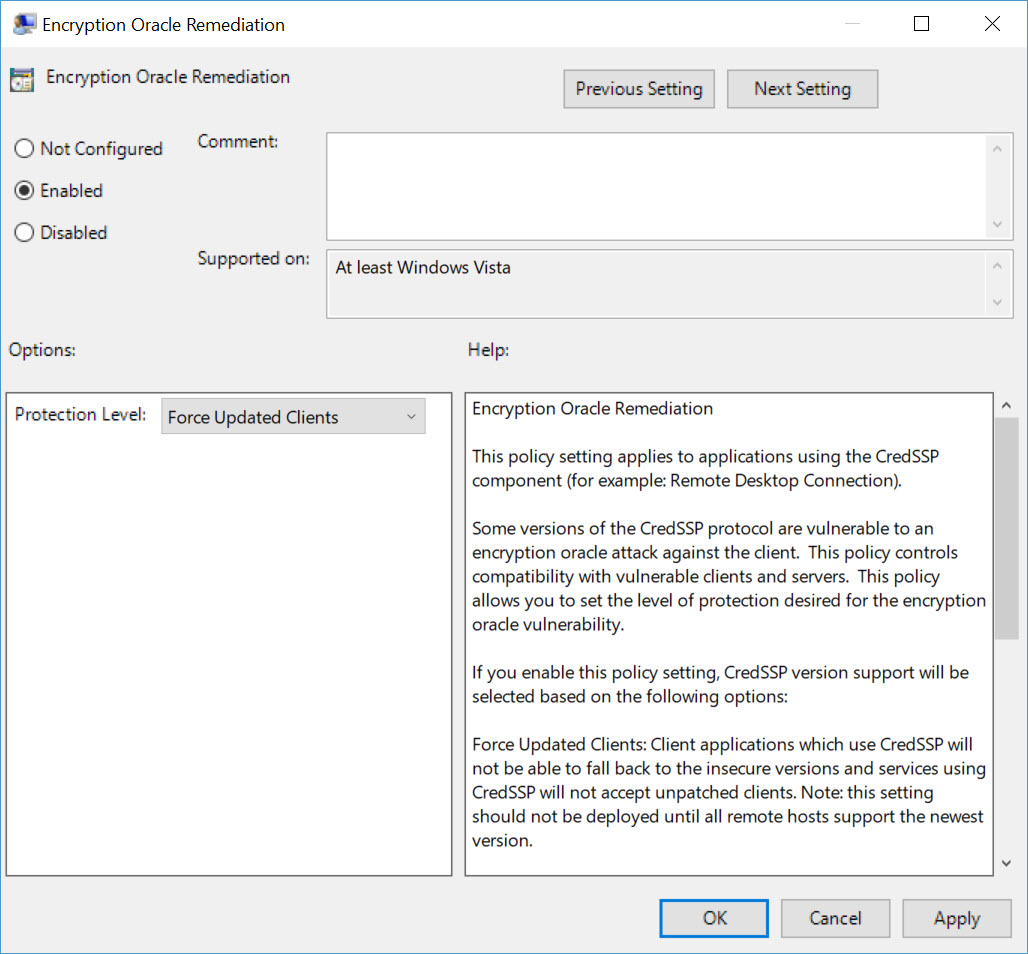
The patch updates CredSSP and Remote Desktop clients for all affected platforms. But for complete protection, it is not enough to install the patch. System administrators also need to apply some new Group Policy settings that are included in the patch. For more information about the new settings and configuring your environment, see Microsoft’s website here.
CVE-2018-0886 isn’t the only remote code vulnerability this month. CVE-2018-0883 patches a problem with the Windows shell and it affects all supported versions of Windows except Windows 1709 64-bit edition. If an attacker was able to exploit the vulnerability, they could get access in the context of the currently logged in user. If the user has administrative access, then the attacker could take control of the device.
There are no critical updates for Windows this month but there are several for Adobe Flash, Edge, and Internet Explorer. The Flash update addresses two critical remote code execution vulnerabilities, Edge – twelve vulnerabilities, and two for Internet Explorer. The Windows denial-of-service (DoS) vulnerability affects Windows 8.1, Windows Server 2008 R2, and all later versions of Windows. A second DoS vulnerability affects ASP.NET Core 2.0, the .NET Framework Core 1.0, 1.1, and 2.0, and PowerShell Core 6.0.0.
There are two import information disclosure vulnerabilities patched for Exchange Server 2016 and an import privilege escalation bug patched for Exchange Server 2010. SharePoint Server 2016 gets nine important privilege escalation fixes and one important information disclosure update. While SharePoint Server 2013 gets two important privilege escalation fixes and one important remote code execution patch. There’s nothing for SQL this month.
Microsoft Distributing Intel Microcode Updates
Microsoft is helping Intel distribute microcode updates that expand protection for the widely-publicized Meltdown and Spectre flaws that hit the headlines in early January. The update addresses extended protection for Spectre Variant 2. Microsoft already released Intel microcode for Windows 10 1709 and Windows Server 1709 (Server Core) that were running on Skylake at the beginning of March. System administrators must download the patches manually from the Microsoft Update Catalog.
On March 13th, Microsoft expanded the patches to include Kaby Lake and Coffee Lake chips. You can download the updates from Microsoft’s website here.
Office 2016
If you have an Office 2016 Click-to-Run installation and are on the semi-annual update channel, you will get version 1803 (build 9126.2072) this month. Apart from noticeable improvements in performance, there’s a host of new features and improvements. Sorting has been brought back to Outlook by popular demand and the Focused Inbox finally makes the cut. Word gets enhanced writing assistance with Editor pane, which provides advanced spelling, grammar, and writing style recommendations.
Problems, Problems, Problems
VMWare is calling out KB4088875 and KB4088878 as problematic.
When applied to a virtualized Windows Server 2008/R2 and/or Windows 7 instances, these patches replace the existing virtual network card (vNIC) with a new one, hides the pre-existing vNIC and does not persist or transfer the existing IP Address configuration to the new vNIC.
And it looks like Microsoft has pulled KB4088875. Read more about the issues here. KB4011730 for Word 2016 breaks opening .doc files if you don’t have the March 6th update (KB4018295) already installed. You can get more information about this issue here.



