Microsoft’s November 2025 Patch Tuesday Updates Fix 63 Windows Flaws
Microsoft’s November 2025 Patch Tuesday delivers major security fixes and new Windows 11 experience updates.

Key Takeaways:
- Microsoft’s November 2025 Patch Tuesday addresses 63 vulnerabilities.
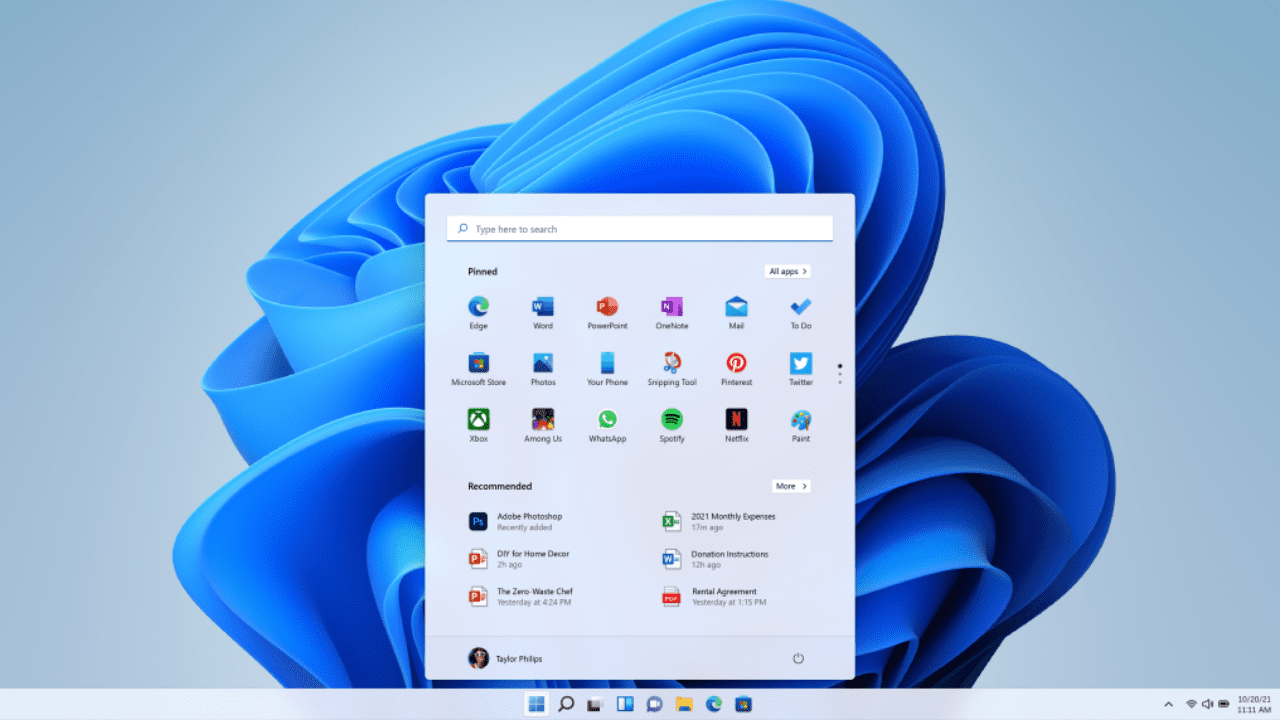
- The update introduces a redesigned Start Menu, taskbar and battery improvements, and new Copilot+ features for versions 25H2 and 24H2.
- A new Administrator Protection preview enhances system security.
Microsoft has started rolling out the November 2025 Patch Tuesday updates for Windows 11. This month, Microsoft has fixed 63 vulnerabilities in Windows, Office, Microsoft Edge, Azure Monitor Agent, Dynamics 365, Hyper-V, SQL Server, and other components.
On the quality and experience updates front, Microsoft has rolled out a redesigned Start Menu and a couple of other new capabilities to Windows 11 versions 25H2 and 24H2. The latest update also brings Click to Do improvements and other changes for users with Copilot+ devices.
63 vulnerabilities fixed in the November 2025 Patch Tuesday updates
Among the 63 Windows vulnerabilities Microsoft fixed this month, four are rated “Critical” and 59 are rated “Important” in severity. One of those vulnerabilities is already being exploited in the wild, and you can find more details about all of them below:
CVE-2025-62215: This is a Windows Kernel privilege escalation vulnerability that could allow hackers to gain admin-level rights on Windows devices. This flaw requires the attackers to win a race condition to gain system privileges.
CVE-2025-60724: This is a critical heap-based buffer overflow vulnerability in the Microsoft Graphics Component (GDI+) that allows remote code execution without authentication. This flaw carries a CVSS score of 9.8 and doesn’t require any user interaction or privileges.
CVE-2025-60704: This is a high-severity vulnerability in Windows Kerberos with a CVSS score of 7.5. It affects all organizations using Active Directory, with the Kerberos delegation capability enabled.
CVE-2025-62220: This is a heap-based buffer overflow vulnerability in the Windows Subsystem for Linux GUI (WSLg) with a CVSS score of 8.8. This flaw could allow an attacker to execute arbitrary code remotely through crafted inputs.
CVE-2025-60719: This vulnerability is an untrusted pointer dereference in the Windows Ancillary Function Driver for WinSock (afd.sys). It could enable a local attacker with low privileges to escalate to SYSTEM.
CVE-2025-62213: This is a use-after-free flaw in afd.sys (WinSock driver) that could allow an authenticated local attacker to gain elevated privileges. This flaw carries a CVSS score of 7.0 (High).
CVE-2025-62217: This race condition vulnerability in afd.sys occurs due to improper synchronization of shared resources.
You can find the full list of CVEs released by Microsoft with the November 2025 Patch Tuesday updates below:
| Tag | CVE | Base Score | CVSS Vector | Exploitability | FAQs? | Workarounds? | Mitigations? |
| Nuance PowerScribe | CVE-2025-30398 | 8.1 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Configuration Manager | CVE-2025-47179 | 6.7 | CVSS:3.1/AV:L/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-59240 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2025-59499 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure Monitor Agent | CVE-2025-59504 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Smart Card | CVE-2025-59505 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows DirectX | CVE-2025-59506 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Speech | CVE-2025-59507 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Speech | CVE-2025-59508 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Speech | CVE-2025-59509 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-59510 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows WLAN Service | CVE-2025-59511 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Customer Experience Improvement Program (CEIP) | CVE-2025-59512 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Bluetooth RFCOM Protocol Driver | CVE-2025-59513 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Streaming Service | CVE-2025-59514 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Broadcast DVR User Service | CVE-2025-59515 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Desktop | CVE-2025-60703 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Kerberos | CVE-2025-60704 | 7.5 | CVSS:3.1/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Client-Side Caching (CSC) Service | CVE-2025-60705 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Role: Windows Hyper-V | CVE-2025-60706 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Multimedia Class Scheduler Service (MMCSS) | CVE-2025-60707 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Storvsp.sys Driver | CVE-2025-60708 | 6.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:C/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Common Log File System Driver | CVE-2025-60709 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Host Process for Windows Tasks | CVE-2025-60710 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-60713 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows OLE | CVE-2025-60714 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-60715 | 8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows DirectX | CVE-2025-60716 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Broadcast DVR User Service | CVE-2025-60717 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Administrator Protection | CVE-2025-60718 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Ancillary Function Driver for WinSock | CVE-2025-60719 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows TDX.sys | CVE-2025-60720 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Administrator Protection | CVE-2025-60721 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:T/RC:C | Exploitation Less Likely | Yes | No | No |
| OneDrive for Android | CVE-2025-60722 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows DirectX | CVE-2025-60723 | 6.3 | CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:C/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Graphics Component | CVE-2025-60724 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-60726 | 7.1 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-60727 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-60728 | 4.3 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office | CVE-2025-62199 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-62200 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-62201 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-62202 | 7.1 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-62203 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2025-62204 | 8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Word | CVE-2025-62205 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Dynamics 365 (on-premises) | CVE-2025-62206 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows License Manager | CVE-2025-62208 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows License Manager | CVE-2025-62209 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Dynamics 365 Field Service (online) | CVE-2025-62210 | 8.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Dynamics 365 Field Service (online) | CVE-2025-62211 | 8.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Ancillary Function Driver for WinSock | CVE-2025-62213 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Visual Studio | CVE-2025-62214 | 6.7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel | CVE-2025-62215 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:F/RL:O/RC:C | Exploitation Detected | Yes | No | No |
| Microsoft Office | CVE-2025-62216 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Ancillary Function Driver for WinSock | CVE-2025-62217 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Wireless Provisioning System | CVE-2025-62218 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Wireless Provisioning System | CVE-2025-62219 | 7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Subsystem for Linux GUI | CVE-2025-62220 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Visual Studio Code CoPilot Chat Extension | CVE-2025-62222 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Visual Studio Code CoPilot Chat Extension | CVE-2025-62449 | 6.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-62452 | 8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| GitHub Copilot and Visual Studio Code | CVE-2025-62453 | 5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:N/I:H/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
Quality and experience updates
On Windows 11 versions 25H2 and 24H2, the KB5068861 patch brings improvements to Click to Do, File Explorer, Voice Access, and Windows Search for Copilot+ PCs. The Windows 11 Taskbar is also getting several enhancements this month. The battery icon now features different colors that indicate whether the battery is in battery saver mode, in charging, in good health, or is critically low.
Additionally, Microsoft has also updated the Windows 11 Start Menu this month. The new Start menu features a scrollable All section with category and grid views, a responsive layout for any screen size, and Phone Link integration via a collapsible side panel accessed through a mobile button next to the search box.
Microsoft has rolled out the Administrator Protection feature in preview for Windows 11 devices. It uses User Account Control (UAC) and security policies to prevent unauthorized changes by requiring admin approval for system-level actions. It can be enabled in Windows Security or via Microsoft Intune or Group Policy.
Microsoft has released KB5068781, the first Windows 10 Extended Security Update after end-of-support, which fixes an incorrect “end of support” message and includes November Patch Tuesday security fixes for 63 vulnerabilities, including one actively exploited flaw. This update is available only to devices enrolled in the Windows 10 Extended Security Updates (ESU) program.
Windows Update testing and best practices
Organizations looking to deploy this month’s patches should conduct thorough testing before deploying them widely on production systems. That said, applying the patches widely shouldn’t be delayed longer than necessary, as hackers start to work out how to weaponize newly reported vulnerabilities.
A best practice is to make sure you have backed up systems before applying updates. Every month, users experience issues with Windows updates that lead to systems not booting, application and hardware compatibility issues, or even data loss in extreme cases.
There are backup tools built into Windows and Windows Server that you can use to restore systems in the event a patch causes a problem. The backup features in Windows can be used to restore an entire system or files and folders on a granular basis.