Microsoft Defender Can Now Block Malicious Drivers on Windows PCs

Microsoft has released a new security feature that should help to protect Windows PCs against malicious drivers. David Weston, Microsoft’s Vice President of Enterprise and OS Security, announced on Twitter today that the vulnerable driver blocklist feature is now available on Windows 10, Windows 11, as well as Server 2016 and higher.
The new vulnerable driver blocklist feature is designed to prevent third-party malicious drivers from running on Windows devices, and Microsoft says that it blocks all potentially vulnerable drivers with known security vulnerabilities. Moreover, the feature prevents threat actors from exploiting vulnerabilities in signed kernel drivers in order to inject malware into the Windows kernel.
Microsoft highlighted that it collaborates with partners and security experts to track malicious drivers. The company keeps adding these drivers to its “ecosystem block policy” to protect against security threats across all Hypervisor-protected code integrity (HVCI) and Windows 10 in S mode devices.
“Microsoft works closely with our IHVs and security community to ensure the highest level of driver security for our customers and when vulnerabilities in drivers do arise, that they’re quickly patched and rolled out to the ecosystem. Microsoft then adds the vulnerable versions of the drivers to our ecosystem block policy” the company explained on a support page.
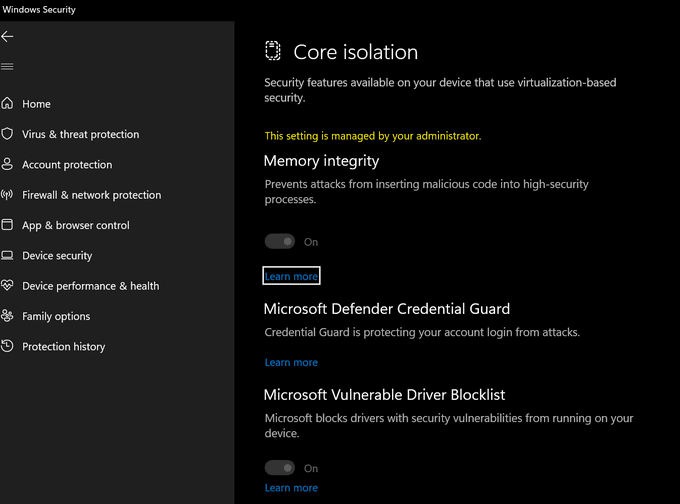
How to enable the vulnerable driver blocklist feature in Windows Security
To enable the vulnerable driver blocklist feature, you will need to open Windows Security on Windows 10 or Windows 11. Then, you’ll need to select Device Security and then click the Core isolation details option. Finally, turn on the Memory Integrity toggle button and restart your Windows device. As shown in the screenshot, the Microsoft Vulnerable Driver Blocklist option should show up under the Device Security section.
It is important to note that the vulnerable driver blocklist appears to be rolling out gradually to all Windows PCs, and it’s not available for everyone just yet. Have you spotted the new security capability on your PCs? Let us know in the comments down below.


