What You Need to Know About Windows 10 S Mode
Microsoft hasn’t made much noise about Windows 10 S Mode, the version of Windows that is restricted to Store apps. And with the death of the Windows 10 S SKU, some have speculated that S Mode is on its way out. But Microsoft is continuing to improve the S Mode experience in Windows 10 version 1809 and beyond.
S Mode provides firstline workers and the education sector with a secure OS and performance that lasts. Versions of Windows that support Win32 installers are prone to ‘Windows Rot’, where applications leave files and registry entries behind that impact performance over time. But the Microsoft Store uses containers to isolate apps from each other and the operating system, providing a clean mechanism for installing and removing apps.
Microsoft says that when pitching Windows 10 S Mode to management, you should present protection outcomes rather than product specifications. For example, because Group Policy isn’t supported, you can’t block USB devices. But because Win32 apps can’t run, Windows 10 S Mode is protected against malware distributed on portable USB drives. And data leakage prevention can be managed by Windows Information Protection (WIP). For more information on WIP, see Introduction to Windows Information Protection on Petri.
The Evolution of Windows 10 S Mode
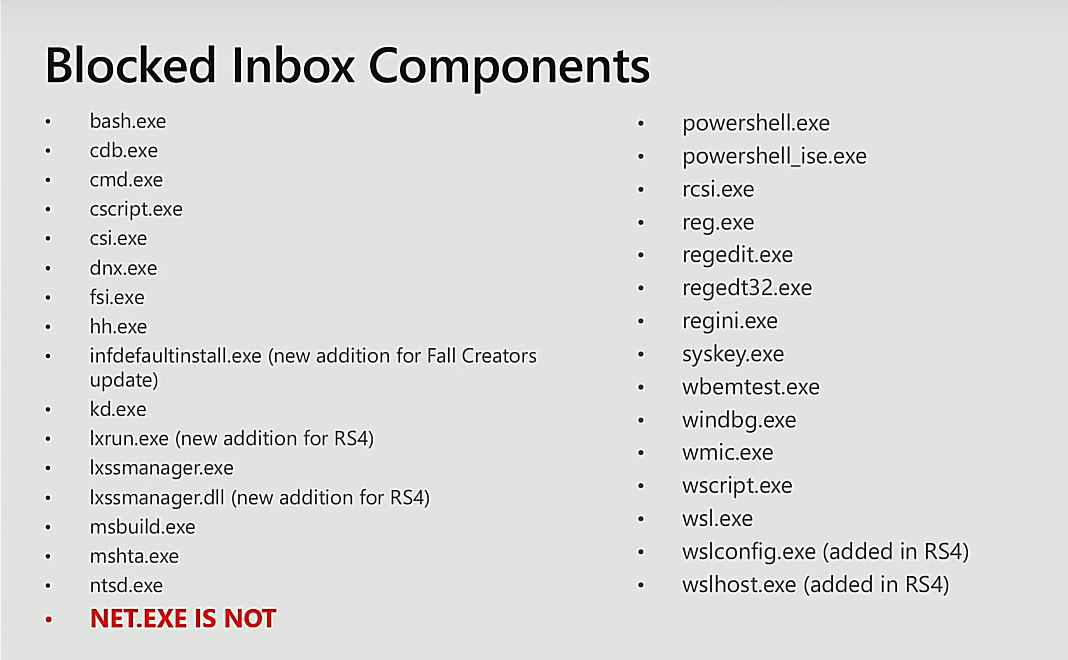
S Mode originated in Windows 10 version 1703 as a separate SKU (Windows 10 S) and was designed to restrict users to installing apps from the Microsoft Store. Legacy Win32 app installers were blocked using what is now called Windows Defender Device Guard, which uses both Windows Defender Application Control and Hypervisor-Protected Code Integrity (HVCI). For more information on Windows Defender Application Control, see What is Windows Defender Application Control? on Petri.
Windows 10 S Mode users can be standard users or administrators. But unlike AppLocker, an application whitelisting solution that was first included in Windows 7, Windows Defender Device Guard can’t be easily overridden if the user also has admin rights. Device Guard is a technology borrowed from Windows Mobile that proved to be effective at securing devices. But it has already been shown how Windows 10 S Mode can be hacked if Microsoft Office, which is a legacy Win32 app, is installed from the Store. Windows Mobile doesn’t support Win32 apps.
Windows 10 version 1709 added the ‘S’ SKU as an installation option and no longer required separate media. But in Windows 10 version 1803, Microsoft did away with the ‘S’ SKU and rebranded to S Mode and added it to Enterprise. Windows 10 version 1809 S Mode is ‘modern management’ ready, i.e. where organizations utilize Windows AutoPilot, Azure Active Directory, and Microsoft Intune instead of a traditional management stack like Group Policy and System Center Configuration Manager (SCCM).
S Mode is OEM Only
Don’t bother looking for S Mode in Windows 10 if your PC didn’t come with S Mode preinstalled. Microsoft only supplies S Mode to OEMs because of the necessity to check that the hardware drivers are either Universal Drivers or meet various other requirements like:
- Digitally signed with a Windows, WHQL, ELAM, or Store certificate.
- Don’t include .exe, .zip, .msi or .cab files in the driver package that extract unsigned binaries.
- Does not have user interface components, apps, or settings. Drivers must use Universal applications from the Microsoft Store instead.
OEMs must also update drivers and firmware through Windows Update. S Mode supports Windows Update and Windows Update for Business. SCCM and Windows Server Update Services (WSUS) cannot be used. For a full list of the requirements, see Microsoft’s website here.
No Support for Windows Server Active Directory
Windows 10 S Mode devices can be joined directly to Azure Active Directory (AAD), including in hybrid AAD/Windows Server AD scenarios. Group Policy is not supported, and organizations should use Windows Autopilot and Mobile Device Management instead.
Application Delivery and Compatibility
Applications can be delivered via the Microsoft Store, the Microsoft Store for Business, and Intune. Office 365 Pro Plus is also delivered through the Store in preview form, with Project Pro and Visio Pro delivered as separate applications. Win32 line-of-business apps can be packaged for Store delivery using the Desktop Bridge if you have access to your app’s original source code.
New in Windows 1809, MSIX promises to let system administrators package apps for the Store in situations where there is only access to the installer. See MSIX Installer to Bring More Win32 Apps to Microsoft Store on Petri for more information on MSIX. Apps deployed via the Store are also updated via the Store, with a little bit of help from Windows Update.
Hardware and Network Support
Printers will largely need inbox drivers to work but Windows 10 S Mode can also download drivers from Windows Print Servers and Windows Update. Win32 co-installers and Desktop Printer Extensions (DPEs) are not supported. Any additional software must be installed from the Store. The same applies for scanners. The Epson Print and Scan app is already available in the Store. HID devices, like keyboards and mice, must be supported by inbox drivers and Store apps.
Wi-Fi connectivity support is the same as in Windows 10. The following network connectivity options are supported in Windows 10 S Mode:
- Local area networks
- Internet Protocol (IP)
- Server Message Block (SMB)
- Active Directory Federation Services (ADFS)
- Hybrid cloud
- Wi-Fi Direct PIN and Ad Hoc PIN
Windows 10 S Mode uses VPNv2 Configuration Service Provider (CSP) for VPN profiles. S Mode supports AutoVPN, App Triggers, and Always ON via the built-in Windows 10 providers, like L2TP and PPTP, and the UWP VPN plug-in platform, which is supported by vendors such as Cisco AnyConnect, F5 Access, and Check Point Capsule.
Windows 10 S Mode version 1809
Microsoft has been busy adding new features for S Mode in the Windows 10 October 2018 update, or version 1809 as it is more correctly known. As I mentioned above, the MSIX installer technology debuts in version 1809 and should make it easier for organizations to get their legacy line-of-business apps packaged for distribution in the Microsoft Store for Business.
Organizations can block users’ ability to break out of S Mode via the Store in version 1809 using an MDM policy setting. Likewise, organizations can unlock S Mode, i.e. move users to the full Pro or Enterprise editions of Windows 10 during or post Out-Of-Box-Experience (OOBE) setup, using a policy setting. OOBE in version 1809 has been designed to support a password-less experience and now requires Internet connectivity. Devices enrolled with Windows Autopilot will require users to sign in with an Azure AD account. If not enrolled in Autopilot, users can sign in with a local account, Azure AD account, or Microsoft Account (MSA).
Users with admin rights can switch to Developer Mode, allowing them to sideload apps without needing to submit them to the Store for approval. This feature is designed to make it easier for developers to test apps on real S Mode devices. And finally, there are new APIs that allow programmatic detection of whether Windows 10 is switched in or out of S Mode.
Windows 10 S Mode Devices are Special Appliances
Microsoft says that devices in Windows 10 S Mode should be treated as special appliances. It’s clear that today, S Mode isn’t going to be suitable in many situations. And Microsoft suggests that legacy Win32 apps that can’t be packaged for the Store could be accessed on a different device using Remote Desktop. That might work for some but it’s not always going to be an option.
Windows 10 S Mode isn’t a perfect solution to your security and support woes, but it could go a long way for frontline workers that need secure and reliable devices with a limited app portfolio. And Microsoft has hinted that it hasn’t ruled out the possibility of direct support for Win32 apps in the future.




