In this Ask the Admin, I’ll explain what Windows Information Protection (WIP) is and how it works to protect sensitive business data.
As part of a defense-in-depth security strategy, Data Loss Prevention (DLP) products control how information that employees have legitimate access to is used. Microsoft says 87 percent of senior managers have admitted to sending corporate data to personal cloud storage and email, and that 58 percent of employees have accidentally sent information to the wrong person. Company documents might be sent to the wrong people when they’re copied in emails unnecessarily, and information might also leak online when posted either intentionally or by mistake.
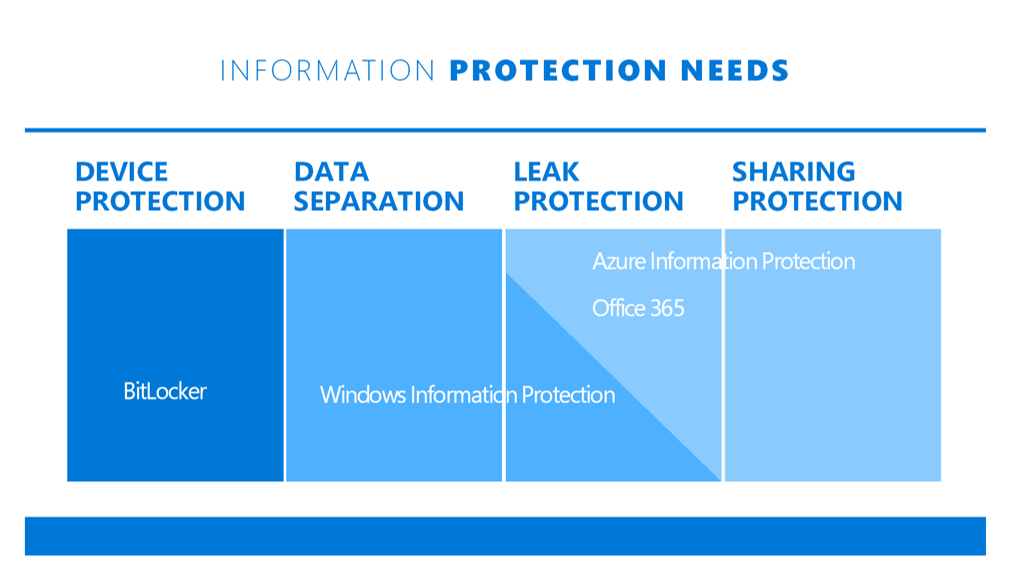
Designed as an alternative to third-party DLP solutions, such as Samsung Knox and Symantec Data Loss Prevention, Windows 10 Anniversary Update includes support for WIP, previously known as Enterprise Data Protection (EDP). Unlike third-party DLP products, WIP is built into Windows so that Microsoft can offer a seamless user experience. Many other products require the use of special applications or to switch modes when working with corporate data, adding a significant layer of inconvenience for both users and IT.
WIP is managed using Mobile Device Management (MDM) policy, as it is also supported in Windows 10 Mobile. Any app can encrypt corporate data when WIP is configured on a device, but only enlightened apps (i.e., those that are WIP-enabled through a set of APIs provided by Microsoft) permit users to save data as personal if WIP policy allows it. So far, there’s only a small set of apps that have been enlightened for WIP, including Internet Explorer 11, Microsoft Edge, Office 2016 desktop and mobile, but the short list shouldn’t prevent you from deploying WIP.
WIP uses the Encrypted File System (EFS) to protect data, and encryption is retained across devices. It’s worth noting that as a Windows technology, WIP is compatible only with devices running Windows 10 or Windows 10 Mobile, which might be a significant disadvantage for organizations using other mobile platforms.
In conjunction with Azure Rights Management (Azure RMS), which is soon to become Azure Information Protection, the protection provided by WIP can be extended into the Office 365 cloud, and Azure RMS allows data to be securely shared with external business partners. Additionally, while the ability to wipe remote devices is not new, because of the separation of business and personal data that WIP provides, IT can wipe business data from employee-owned devices with confidence that they won’t touch personal data.
For more information on how to deploy Windows Information Protection, stay tuned to the Petri IT Knowledgebase.




