Streamlining SaaS Governance: How Nudge Security Simplifies Compliance and Security Management for Cloud Apps

Nudge Security provides a simple and easy to implement solution to a challenging problem for organizations managing compliance, security, and governance of third-party cloud apps and services. Its simplicity encourages governed use of SaaS apps and the ability to monitor new apps and user signups. Nudge Security is a powerful alternative to complex products like Microsoft Defender for Cloud Apps, making it a compelling alternative.
Balancing employee freedom and IT governance for third-party SaaS
In the past, IT departments held extensive control over every aspect of business computing, often leading to delays and reduced agility due to strict oversight, including use of administrator rights. For instance, I knew of a bank where a request to use a piece of already licensed software could take 6 weeks. I contracted into an IT service provider where a laptop had to be supplied by the business and it took 8 weeks to be prepared. Clearly, the controls of IT were affecting the ability of employees to work.
However, the rise of the cloud disrupted this paradigm, granting employees the power to quickly adopt new solutions with just a web browser, internet access, and a credit card! This shift swung the pendulum from extreme control to extreme freedom, allowing employees to leverage various cloud services without considering important factors like data security, usage auditing, and compliance with legal requirements.
This transformation has created a challenging dilemma for organizations as they navigate the delicate balance between empowering employees with newfound freedom and maintaining some degree of oversight and control.
How can we give employees the freedom to use Cloud services? How do we keep them in a state where we can observe what they are doing and bring them under the umbrella of necessary data and account lifecycle controls? IT is not there to say “no” but rather “how?”
Meet Nudge Security
Nudge Security aims to be a friendly, warm hug to employees to nudge them into compliance instead of IT being Nudge Dredd, constantly shouting out “I am the law!”. I was blown away by the simplicity of the concept when it was demonstrated to me during a call.
You sign up for the service and it uses Microsoft/Google APIs to monitor incoming emails of employees. If an email looks like a cloud service registration, Nudge Security adds the relevant information to the inventory of SaaS and cloud apps. It could be a type of service that is new to the business. If so, IT can look into it. Is it secure? Is it compliant? Is it reliable? Can we integrate the new service into our authentication/authorization and identity governance?
If the service appears to be a duplicate of something that is already in the service catalog, then a friendly email or Slack message can be sent to the employee, offering them other options and a chance to have an open conversation.
The beauty of the concept is the elegance of the design. Don’t say “no”. Encourage agility and transparency so employees don’t try to go around more severe controls like blocking access. Don’t automatically respond negatively – look at the service and see if it can be an asset and take it into control to make it easier for everyone to use.
My testing process
I was given a quick briefing on Nudge Security so I knew what I was going to see when I signed up. But I deliberately did the review without any assistance to see what a potential customer experience might be like. I tried out many regular tasks and tried to understand and document what the human experience might be like.
Using Nudge Security
It is easy for IT departments to sign up if you want to try out Nudge Security; browse to www.nudgesecurity.com, and click the Try It Now button. You can sign in using your work email, provided it is associated with either a Google Workspace or Microsoft (Entra) Organization (with support for multifactor authentication). You will need to grant Nudge Security access to your Google or Microsoft tenant. A wizard will walk you through the setup.
Signing up
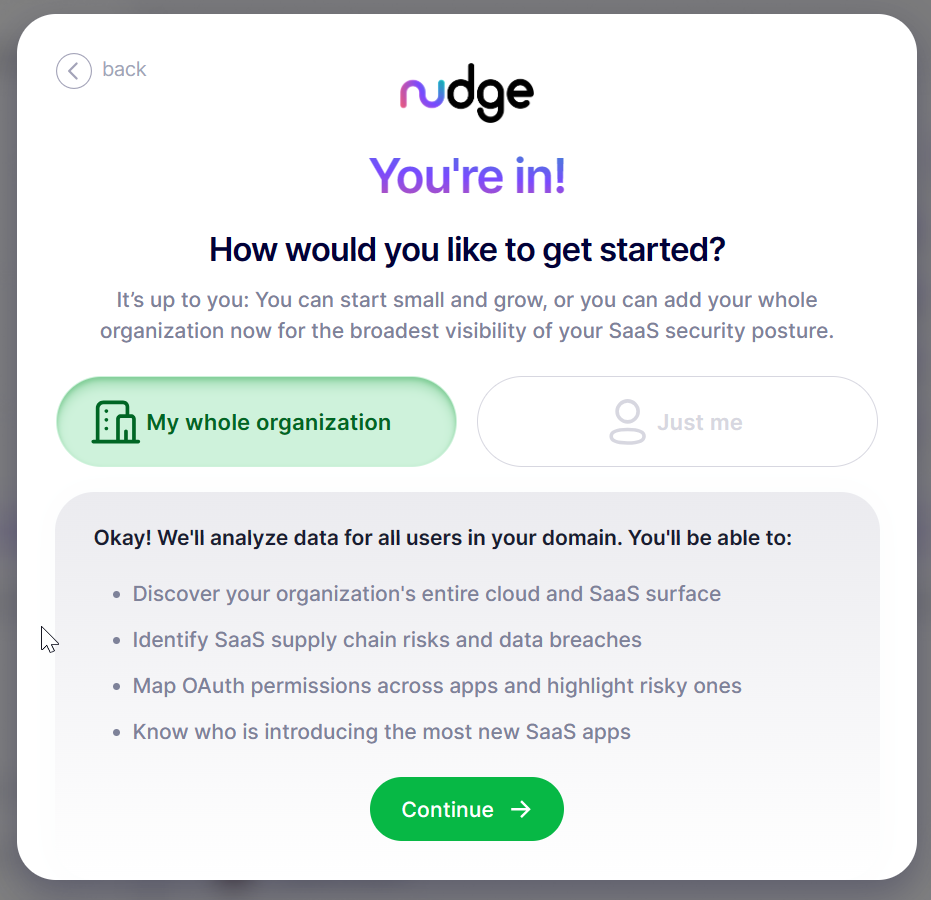
A welcome wizard greets you. You can choose to restrict the service to just your account, which will limit analysis to just data for yourself or establish control for the entire organization.
The magic begins once you complete the sign-up wizard. Nudge Security will analyze existing email, OAuth and SSO activity to find out what SaaS solutions are already in place. This simple concept should not feel so incredible – why does another product I know of in this market analyze firewall logs to know what is out there? Why not just look at the registration emails to figure out what SaaS products are being used?
There’s no point in sitting here watching this screen. Even in my tiny Office 356 tenant, this process took a couple of hours. You will get an email when the scan is done so it’s time to multitask.
Welcome
After the analysis is completed, you can sign in to view the dashboard.
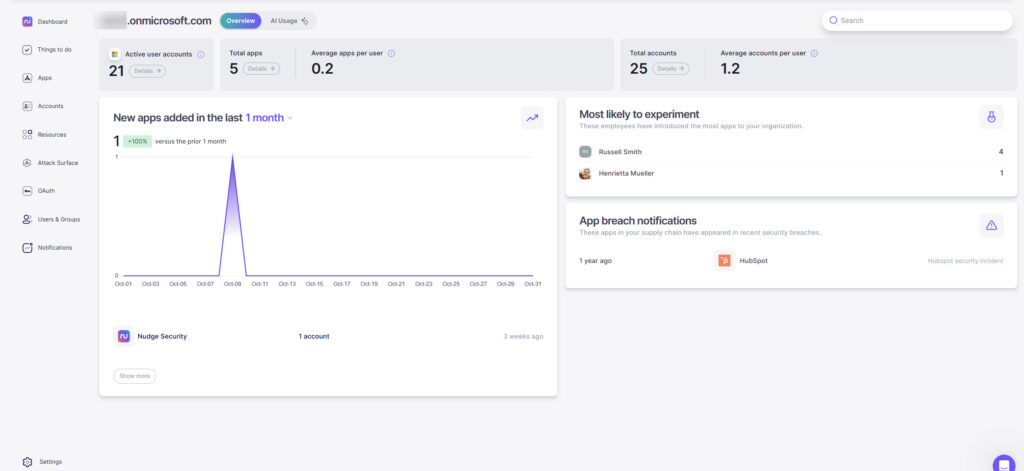
The natural first action is to see what was discovered! Anything that has an account registration is picked up as an app. If your employees have used their work email to sign up for services like online streaming, shopping, news sites, etc. those will also show up in the inventory, in additional to the apps they use for business purposes. The breadth of discovery and app categorization is good, and anything the engine doesn’t yet recognize is grouped as “Unclassified”. This tends to be where apps and services geared more towards personal use will show up.
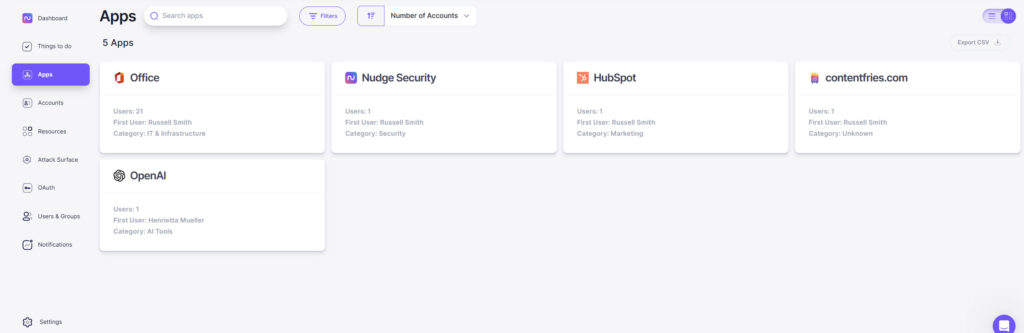
Most of the sites are pretty well-known companies and it was surprising that there wasn’t some built in classification or automation for dealing with “noise”. When I asked Nudge about this, they said that the Unclassified category is intended to deal with noise because the other categories are focused on common workplace applications.
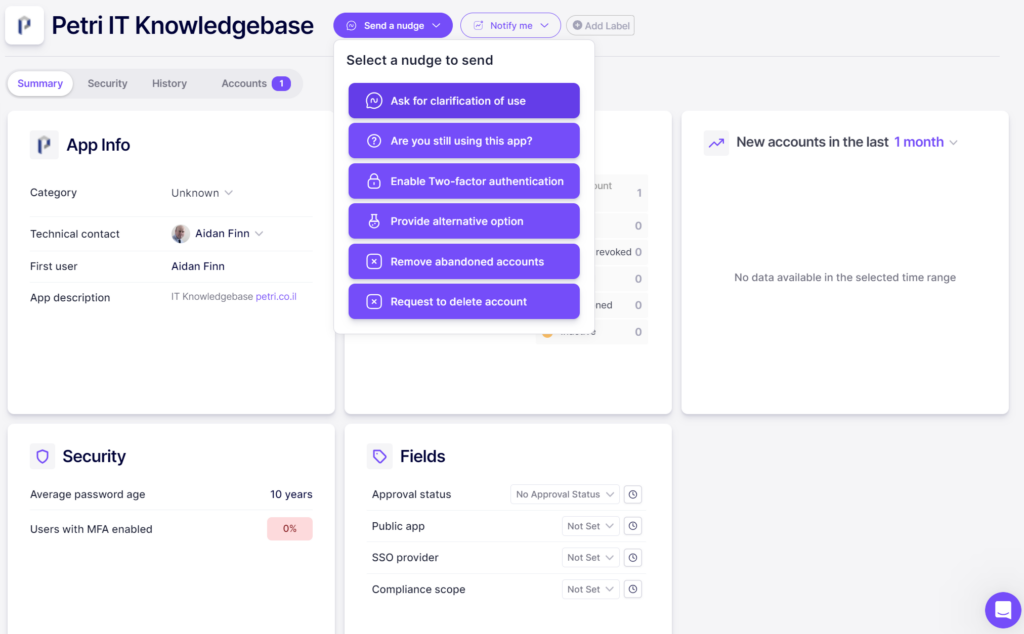
One can drill into an app to learn a little bit more about it:
- Who is the technical contact?
- Who was the first user?
- Total number of user accounts discovered.
- Security information including average password age and MFA status.
- Administrator-managed tags for approval status, public app status, single sign-on provider selection, and a USA-oriented compliance scope selection.
When you have discovered an app, you can send a nudge to the technical contact. This can include:
- Asking questions about the app
- Enabling multifactor authentication
- Suggesting an alternative
- Account handling operations
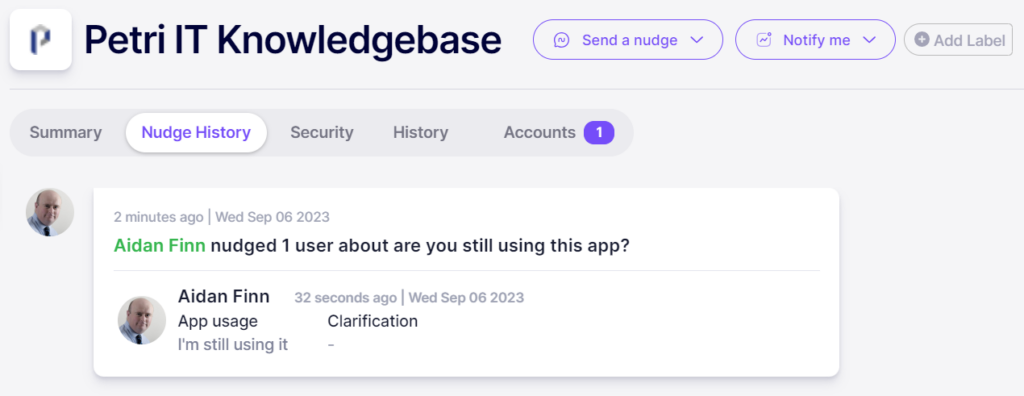
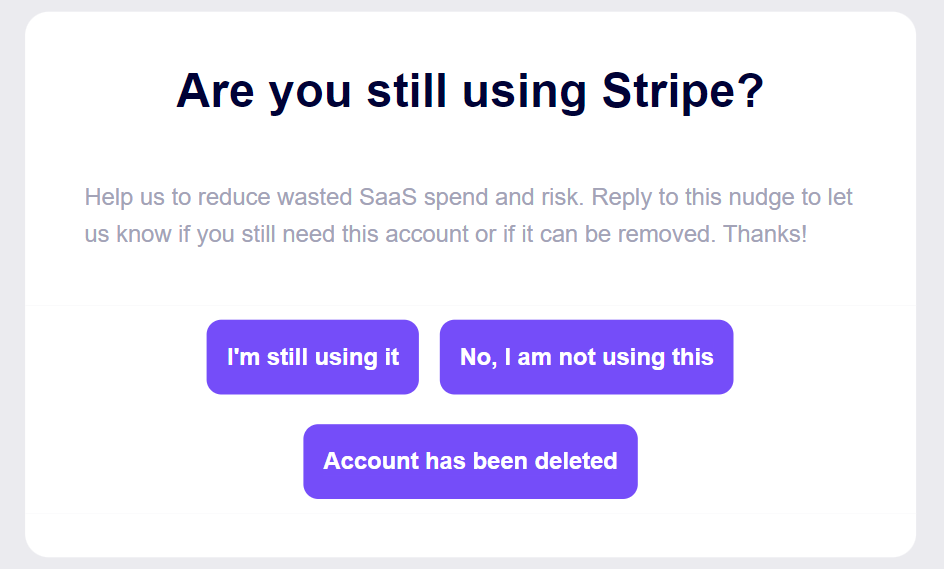
I received an email from Nudge almost immediately after asking “are you still using this app”. A nicely formatted email arrived with click options of:
- I’m still using it
- No, I am not using this
- Account has been deleted
The Nudge history was updated for the app to indicate that I was still using the app.
Additional information on the app is also available. Security shows us the status of the app, including a breach history. History shows a timeline of the app in the tenant. And Accounts summarizes the user accounts from the tenant that are using the app – a nice feature to see here is the ability to export information to a CSV file that includes the username, email address, first seen timestamp, last active timestamp (based on email activity), and the authentication method that was detected. You can also receive a notification when a new account for the app is created – useful when you detect a rogue app.
Customize Nudge Security settings
You can customize Nudge Security for your organization.
Profile is where you can set up your user account and configure email subscriptions to receive weekly summaries and breach notifications – now you don’t need to rely on users to let you know.
Manage Users allows you to invite other users to Nudge Security and grant them roles. This will be important to bring security and governance teams on board without granting full rights. If you have started a trial with just a single mailbox, you can very easily enable organization-wide access or revoke all access through Office Integration.
Analysis History gives you a quick health check to see if Nudge Security is still analyzing your tenant.
You can enable integration with Slack – fine for the minority who use Slack but I find it puzzling that Teams is not being used with a product that so easily integrates with the dominant office product on the planet. This is clearly an important missing feature.
Managing employee offboarding
Employee offboarding is a way to manage the removal of employees. What happens to that employee’s cloud accounts and assets (company assets!) when they leave the company? You can select a user and perform offboarding activities such as:
- Transfer ownership of content: This provides you with a checklist of resources that you must arrange to repossess. In my case, GitHub repos and social media accounts were detected.
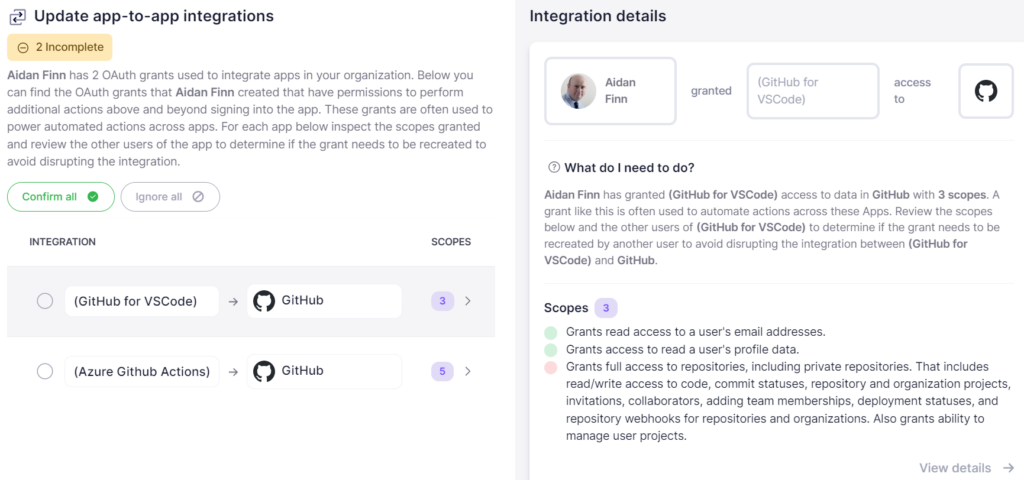
- Manage App-to-App Integrations: See how apps are granted rights.
- Revoke Unmanaged Accounts: Reset passwords to prevent a departed employee from using the app again.
- Update technical contacts: Change the business owner of an app.
One can imagine that an employee might have many accounts to revoke when they leave the organization. There is a handy Revoke All button to reset all passwords for “unmanaged” accounts that are not governed within an SSO or IDP. However, I attempted to revoke several apps automatically. Each attempt failed and I was prompted to manually change the passwords with a deep link to each SaaS application’s password reset page. I cannot blame Nudge Security for SaaS providers’ various protections against robotic password resets – but the manual process will be quite time consuming.
AWS
A fear for organizations is that an employee can easily start up a platform account, such as AWS, and deploy services/data outside of the organization’s governance, compliance, and security controls. All AWS, GCP and Azure accounts can be discovered and Nudge Security includes a playbook to bring AWS accounts under central governance. That’s a good thing – but I’m disappointed to see that the playbook is limited to AWS.
Note from Nudge Security: Feedback from customers has been that the native capabilities in GCP and Azure for bringing accounts under governance are much easier than for AWS, so we have prioritized solving this pain point for AWS.
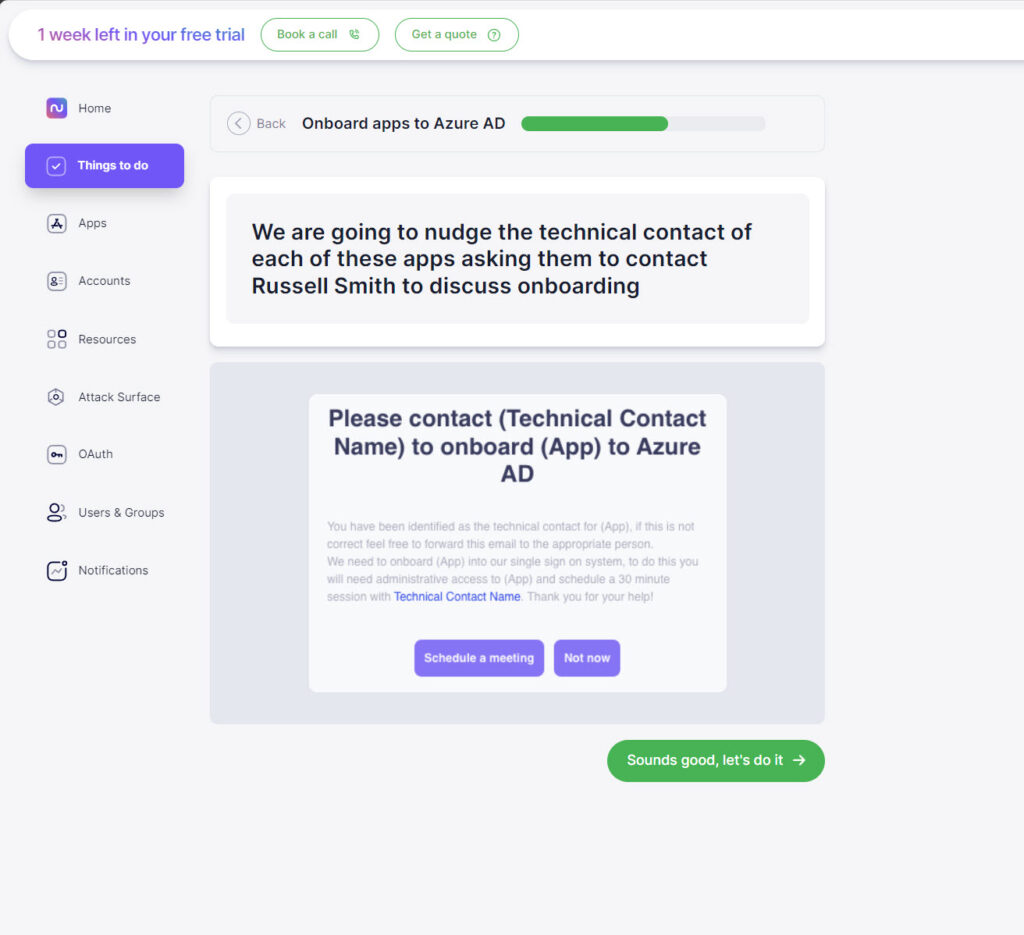
Enabling Entra ID (Azure AD) authentication
You can view which of your apps have been onboarded into Microsoft Entra ID (previously called Azure AD) for single sign-on and identity governance/control. The complexity of enabling this is that the owner of the cloud service must enable the app’s side of the integration. Nudge Security allows you to see which apps aren’t integrated with Entra ID and to nudge a selected employee to start the process of integration.
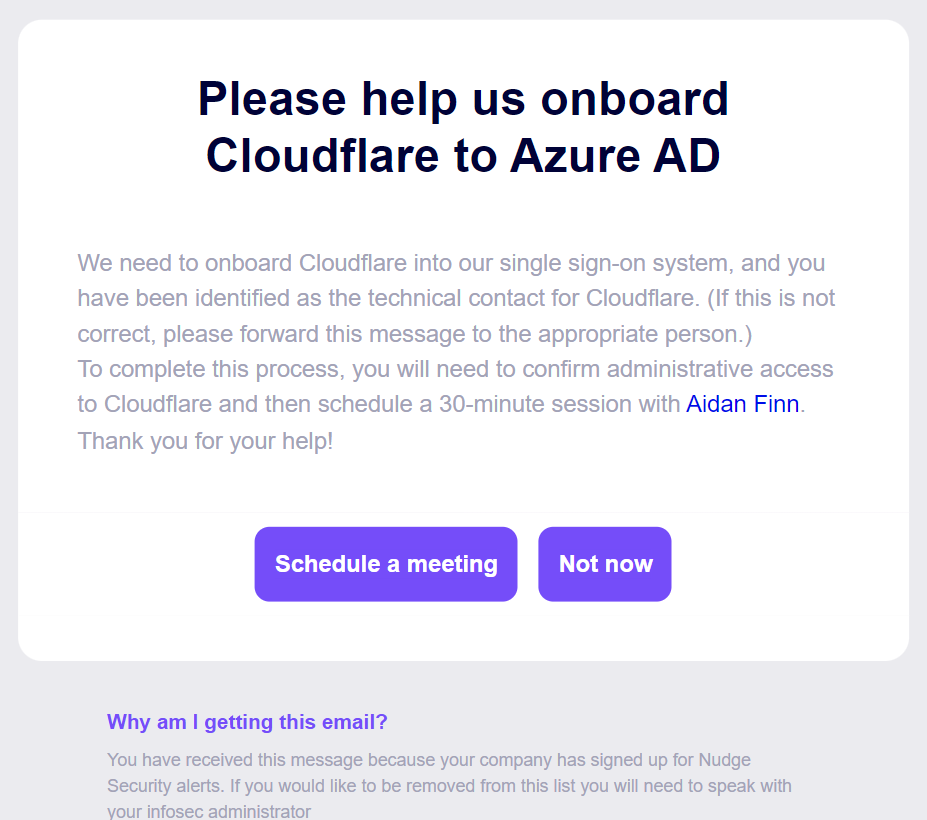
The nudge is quite sensible; enabling Entra ID integration for any cloud app is not a trivial task, so it will involve IT. The nudge is an invitation to bring the selected employee into a process to schedule a meeting with a member of IT.
The employee receives an email with a Schedule Meeting link which can open Google or Outlook. In my tests, it only tried to open Outlook online and made no attempt to open Outlook on my PC. The online Outlook failed to open correctly. I like the concept, but the execution wasn’t what I was hoping for.
Abandoned accounts
Cloud apps come and go – how many do you think you have signed up for and still use? Judging by my screen shots, I have quite a few! Those dead accounts should be shut down to minimize the attack surface of the organization. You can create a nudge to employees to ask them if they are still using a service or not. Nudge sends one email to users detailing all the apps that need attention.
When the information is collected, a nudge can be sent to the owner of the application that includes a CSV of accounts to disable. The owner can then remove those accounts from the app.
Attack Surface
This is a rather interesting view of the data that is gathered. You can view different attack vectors against your organization based on apps and dependencies. Social media accounts, Entra ID domains or other domains registered by any employee, asset storage (files, HR, finance, and so on), cloud infrastructure (Azure is poorly presented here) are all present.
The one that I really was impressed to see was supply chain breaches. It’s hard to keep track of which services have been attacked. Even worse is keeping track of supply chain attacks – many SaaS services are used to build other SaaS services.
An employee might have no idea that Loom is being used by the SaaS service that they subscribed to and that it has been compromised in the past year.
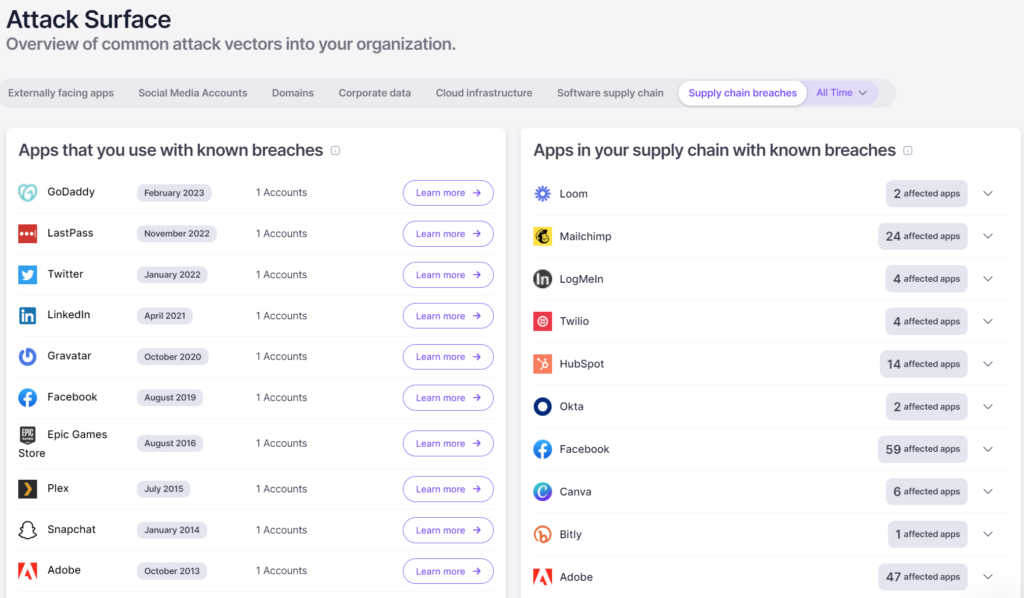
It is the duty of a SaaS vendor to tell a customer that there has been a compromise – but does that employee who may receive the breach notification email understand or care? The security organization does care but will likely not receive a notification; Nudge takes care of that for you.
Notifications
Nudge includes 8 notifications by default, including when there is a compromised user account or an app has a breach. A simple wizard lets you customize the notifications to suit your needs.
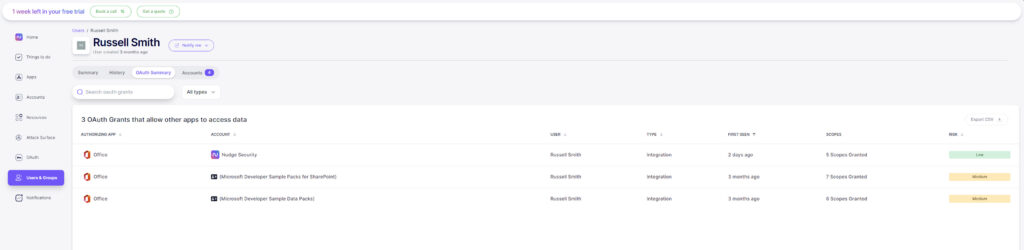
Assessing OAuth grants, risks, and revoking OAuth grants
Nudge Security lets you see the OAuth grants in your environment. OAuth grants are a method for getting access tokens to make requests to resources. Nudge shows grants associated with Google Workspace, Microsoft 365, GitHub, and Slack.
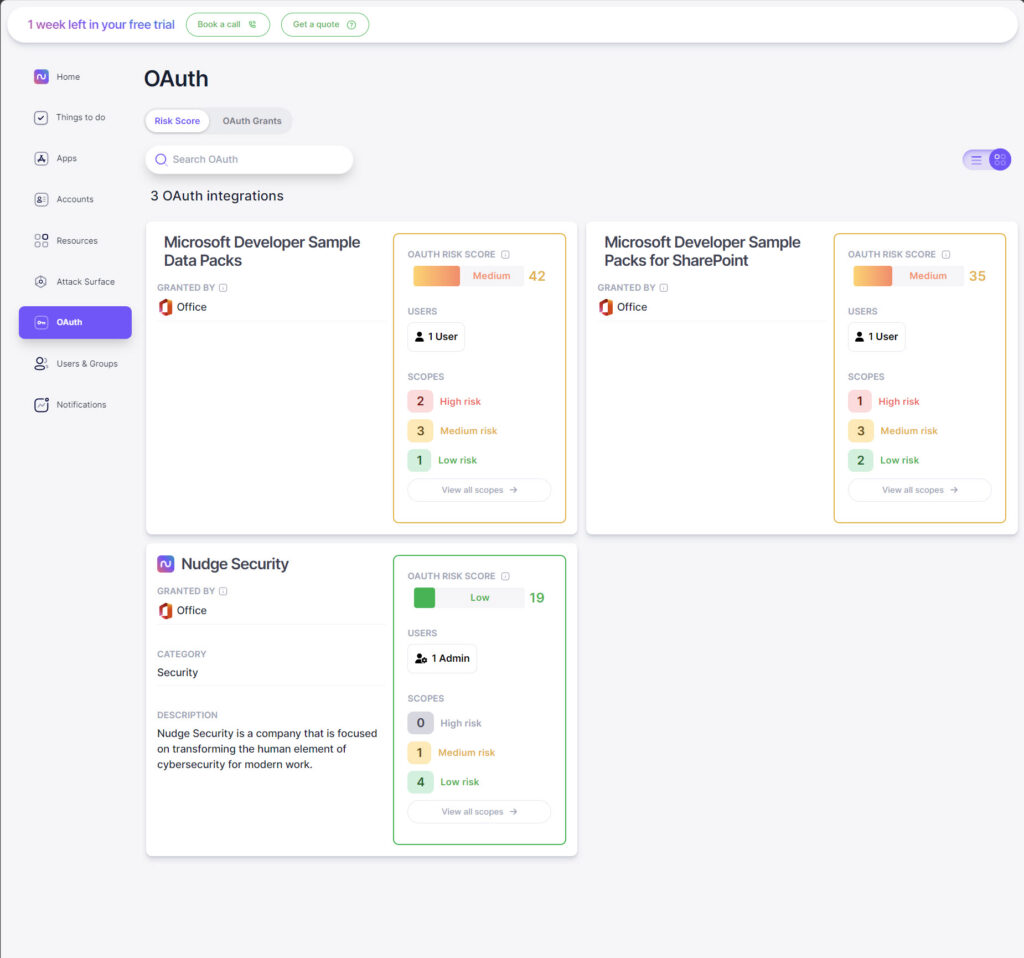
Clicking on View all scopes gives more information about exactly what permissions have been granted.
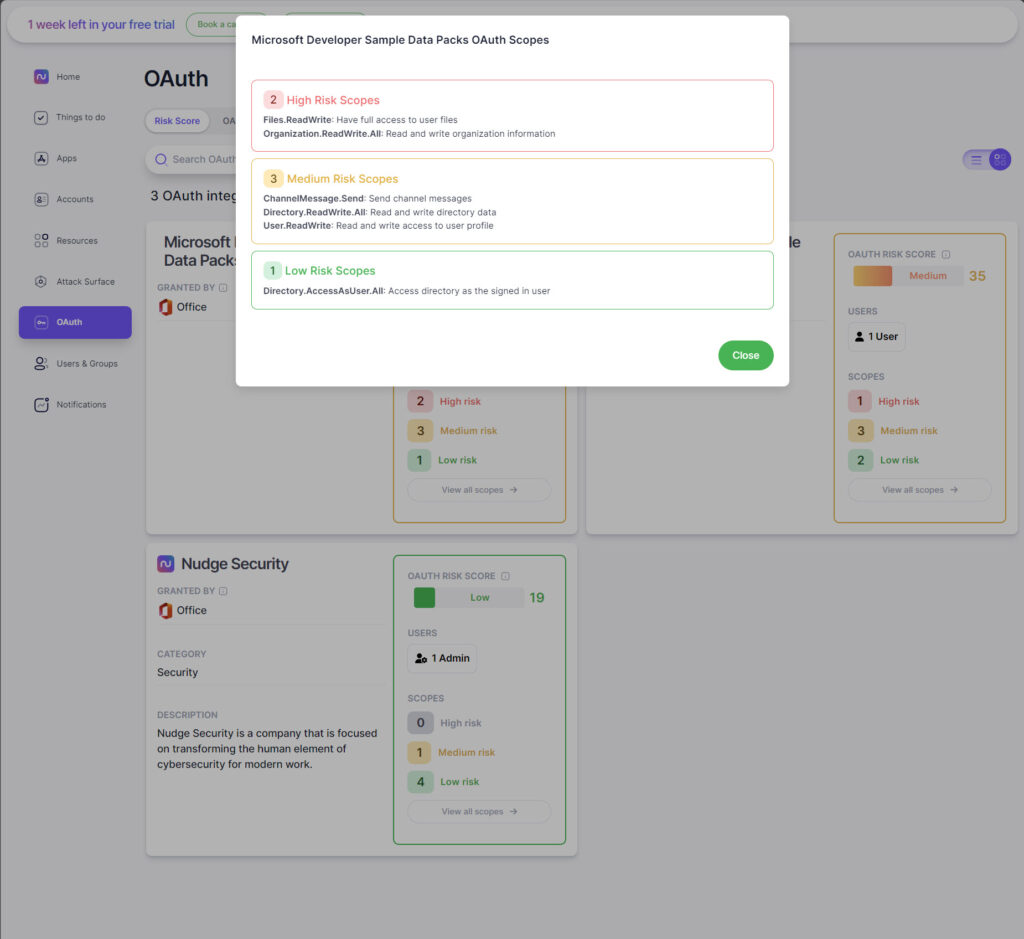
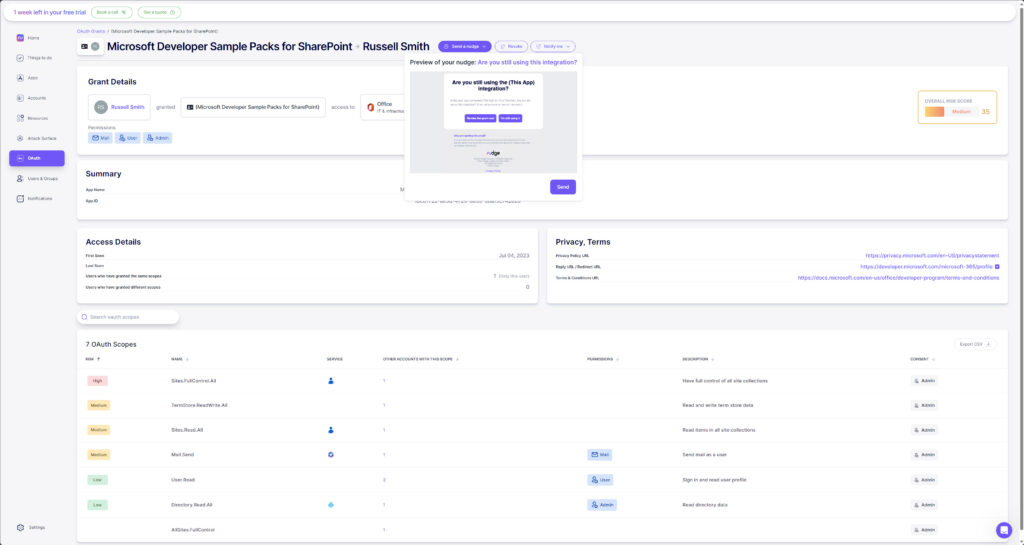
Even more detail is provided by switching to the OAuth Grants tab. By default, grants are sorted by risk, but you can sort them by any of the given columns, like Authorizing App and User. Clicking on a grant provides a lot more detail.
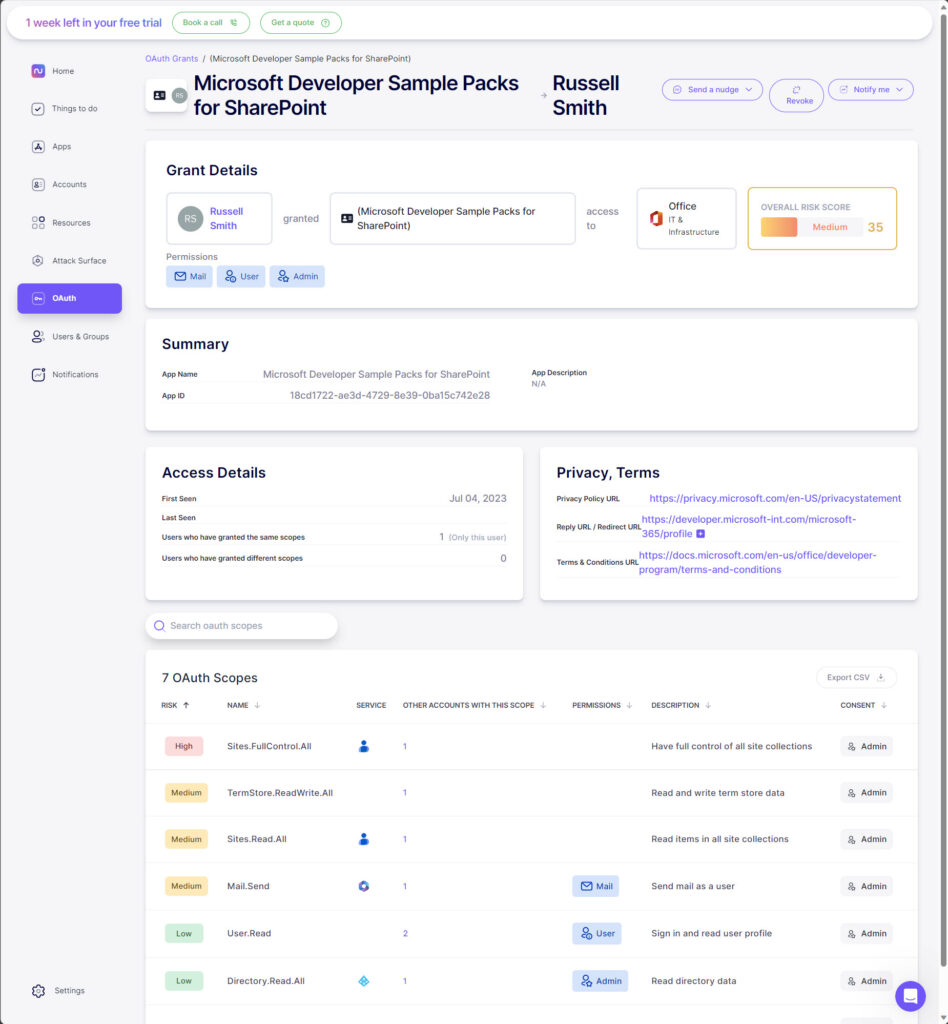
On the details page, you get a summary of the permissions granted, in this case Mail, User, and Admin. Plus a full list of the OAuth scopes.
Importantly, there are three actions you can perform:
- You can send the user a nudge asking them whether they are still using the OAuth grant. The user gets two options: to inform you they are still using the grant or to revoke the grant now. You also get a useful preview of what the user receives.
- There’s also the option to revoke the grant. You will be asked to confirm the action before it is revoked.
- And to be notified if there are any new OAuth grants for the app or user.
Assessing SSO coverage and launching SSO enrollment workflows
One of the great features of Nudge Security is ‘Things to do’, which provides a series of playbooks to remediate security issues it identifies in your organization. For example, in Petri’s Microsoft 365 Developer environment, you can see there are 5 apps, none of which have been onboarded to Entra ID for single sign-on (SSO).
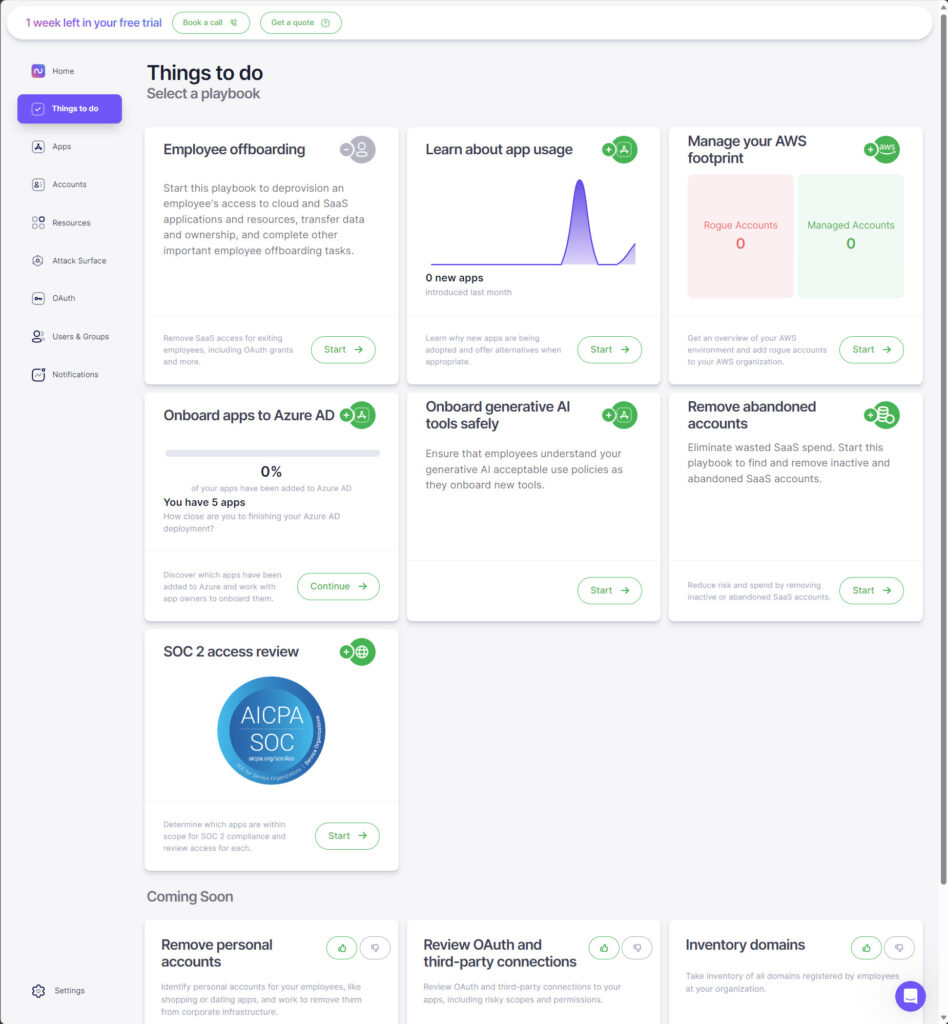
Starting the playbook reveals Petri’s Editorial Director, Russell Smith, as the technical contact for the tenant. There’s also the option to change the contact in this step. The wizard takes you through onboarding the apps to Entra ID and nudging teammates about the apps.
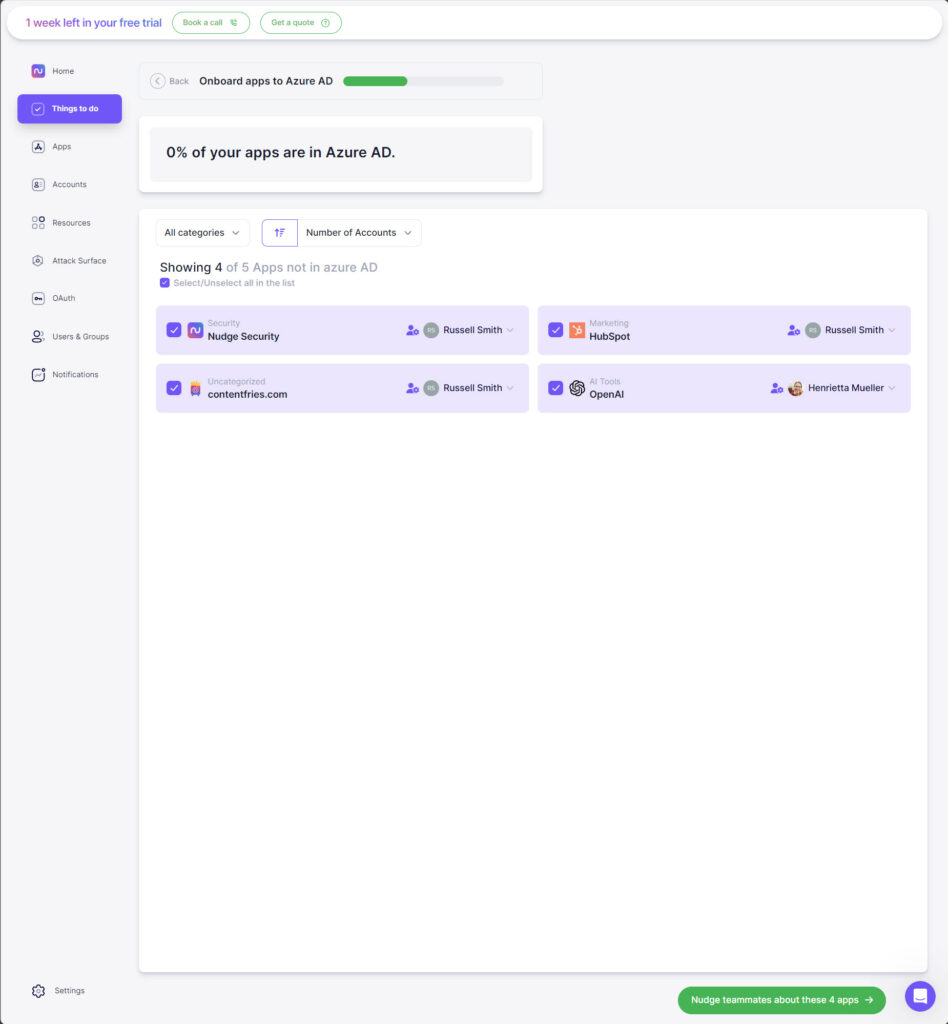
Again, here you get a preview of the message that will be sent, which gives the recipient the option to schedule a meeting with the technical contact or not proceed with enrollment at this time.
Finally, you get the option to be notified when new apps are added and automatically nudge users.
Reviewing security profiles of SaaS providers in your environment
Nudge provides a security overview of SaaS providers. In the Microsoft 365 Developer tenant, clicking on HubSpot and then switching to the Security tab reveals information that allows you to assess the security profile of the SaaS provider.
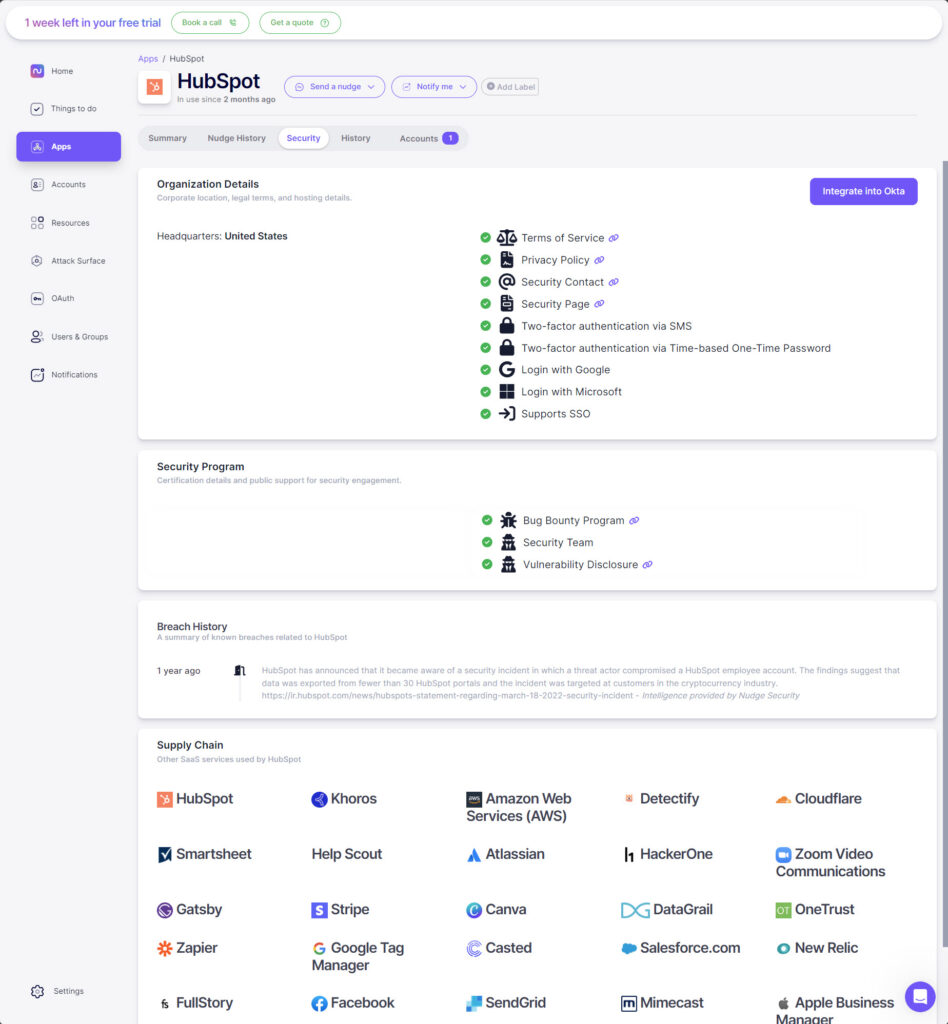
In this case, you can see that HubSpot supports Google and Microsoft logins, and various options for two-factor authentication. Also, there are details of any certifications or programs the vendor has for security, like a bug bounty and vulnerability disclosures.
In addition to a breach history, you get to see the provider’s supply chain. Supply chain attacks are increasingly common, so it’s important to be aware of who the provider is working with. Although, it would have been nice if I could have clicked on the entries for SaaS services used by HubSpot to see their security profiles.
Conducting user access reviews
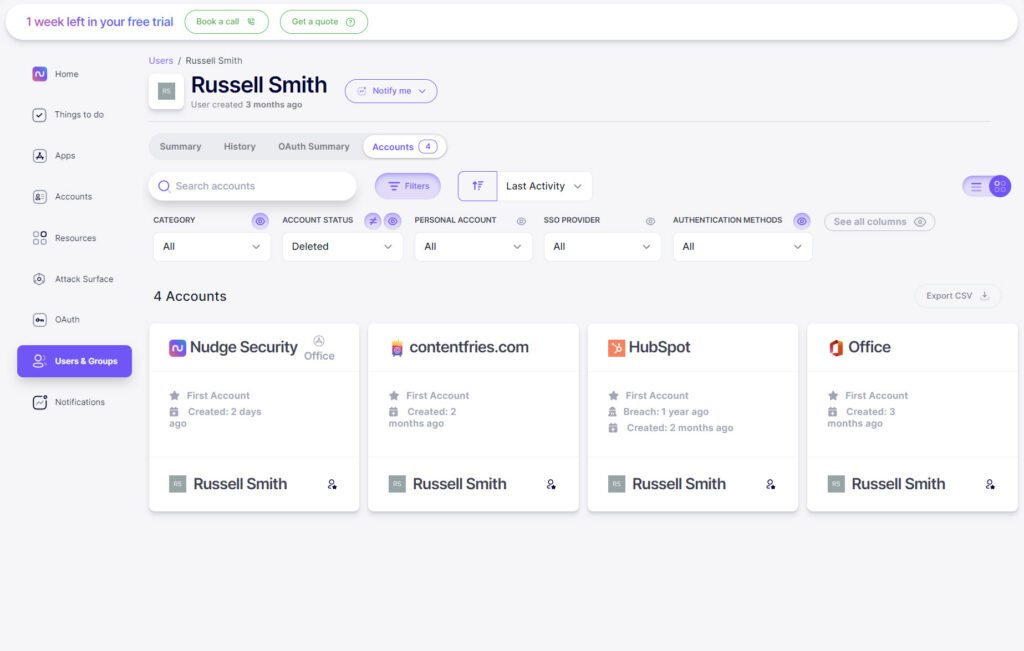
Nudge provides the ability to easily review user access in your environment. Users & Groups displays all the users in your connected tenants and a summary of their accounts and the apps they have introduced. Clicking a user provides more detailed information about their security profile.
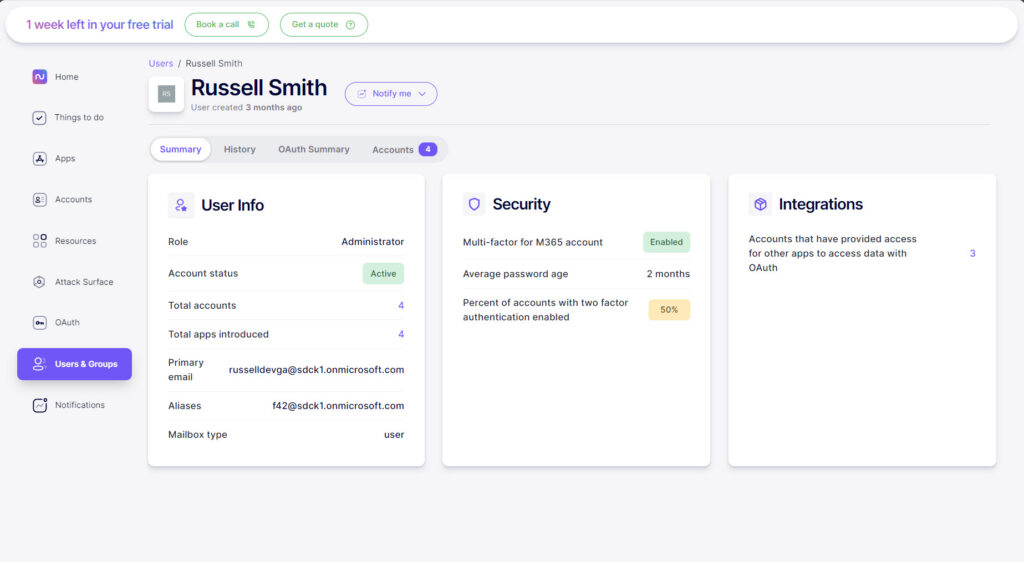
The History tab displays an account creation timeline and the OAuth Summary tab a list of grants associated with the user.
The Accounts tab lists all the user’s accounts and you can further filter the list by several criteria, including category, SSO provider, and authentication methods.
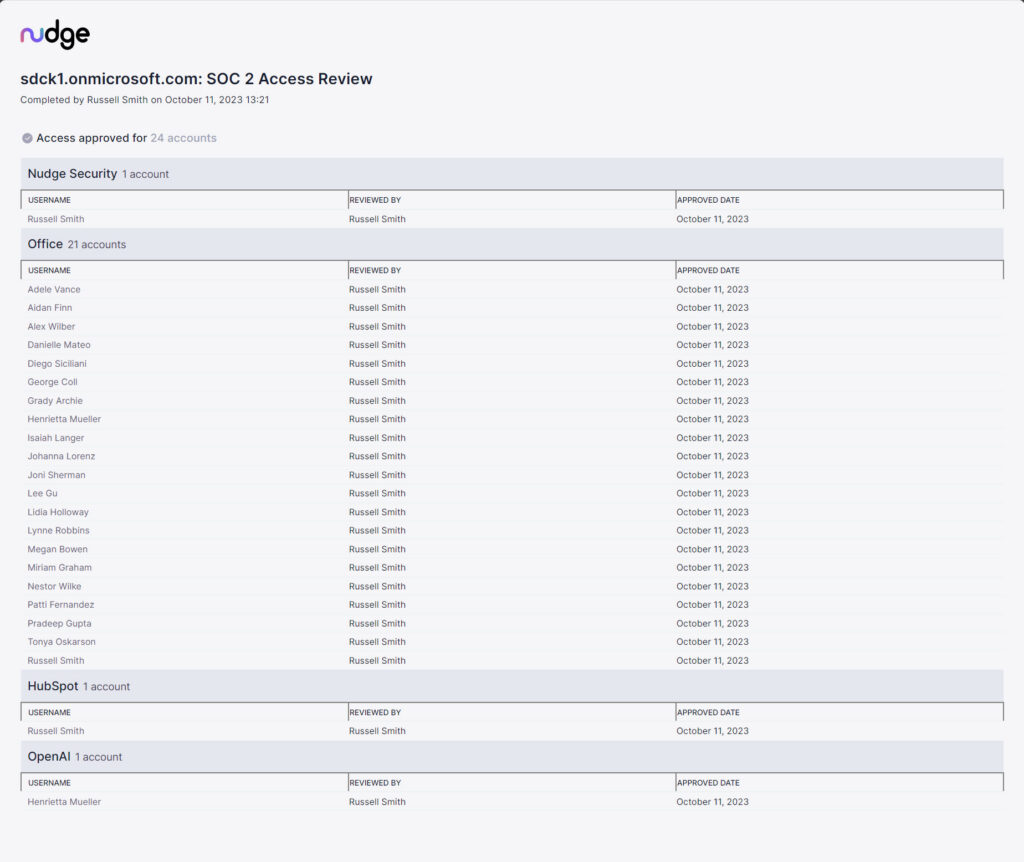
For organizations that need to comply with SOC 2 requirements, there is a playbook just for you. It can identify which apps are likely to be in scope and then review access to them.
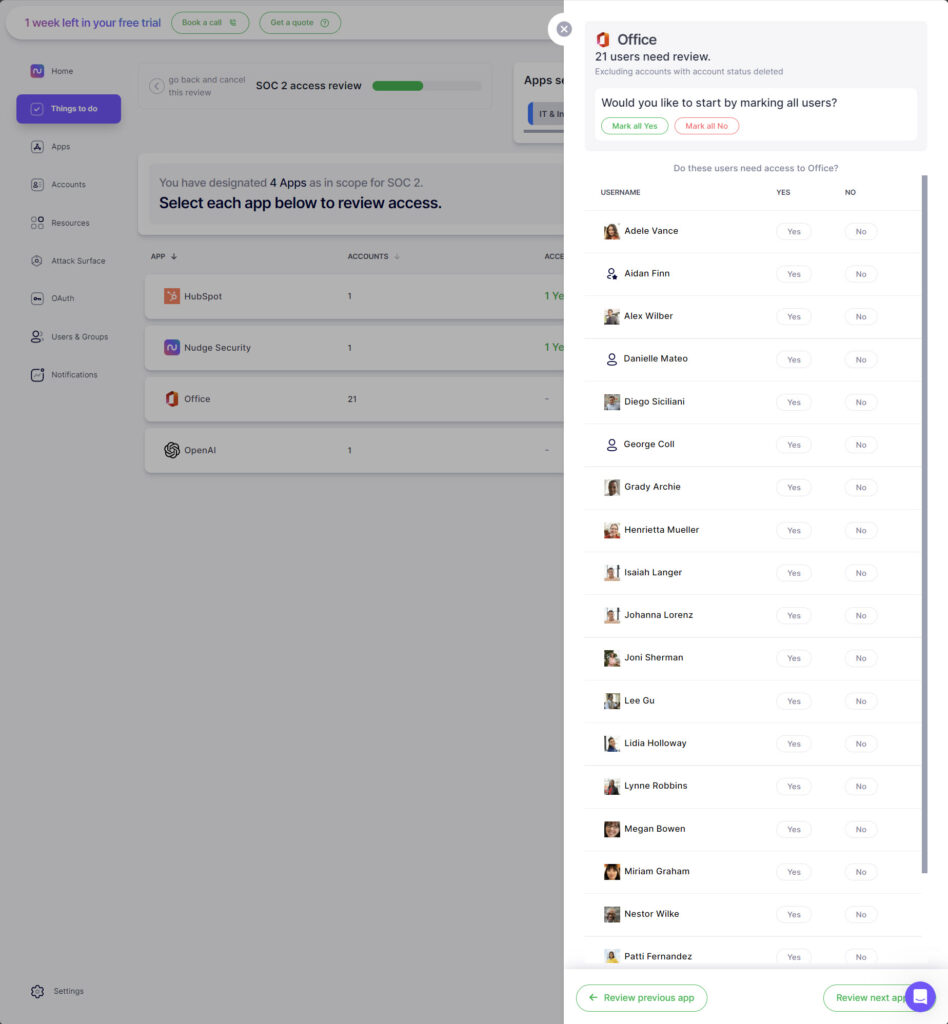
You can review each user’s access to an application and revoke it where necessary. Nudge lets you access a list of historical reviews that you have performed and generate reports for auditors.
An interesting solution to a difficult problem
My first impressions of Nudge Security were really good. I admire the simplicity of the concept – don’t be a negative gatekeeper to adoption. Instead, encourage governed usage of SaaS apps where employees feel that it is OK to sign up using their work email address. Nudge Security can monitor that email account and detect new apps or user accounts. The organization now has a way to manage apps, accounts, and assets in the cloud, which is a difficult challenge.
Enabling the integration was super easy and the net is sure to catch most of the fish. Compare this approach with the one taken by Microsoft Defender for Cloud Apps. David’s elegant simplicity is a slingshot to the forehead of Goliath’s stumbling complexity.
You can fall into the trap of thinking “Nudge Security will do everything for me”. Unfortunately, there are things that just cannot be done by this kind of solution. IT will always have to be nudged into doing things like enabling Entra ID integration or disabling user accounts.
I like the gentle wording used in the nudges; this is important because a solution such as this requires employees to not want to use personal email accounts to sign up for SaaS apps. Employees must feel like they are a part of the solution. A perfect example is the nudge to set up app authentication with Entra ID – the employee is invited to schedule a meeting with IT because the integration will be complicated, and assistance required.
My worry is that there may be too many nudges, especially early in adoption. Employees receive too much email already, and piling on will lead to disinterest or automated rules to delete noisy emails. Administrators will need to be judicious about how and how often to use nudges in order to avoid email/Slack overload.
I’m also disappointed to see that some Microsoft cloud products have been left out. Slack, which has roughly 10% of the userbase of Teams, has an integration feature but Teams does not. AWS has a footprint management feature, but Azure does not because the playbook addresses a unique problem in AWS tenants that does not persist in Microsoft Azure.
Overall, I think that Nudge Security is a very interesting solution to a difficult problem. I like their approach and while I think that not everything is perfect, this is a cloud product from a relatively small company and agile improvement is likely – in fact, one can up/down vote roadmap features in the Things To Do screen.
Nudge Security is a product that is worthy of consideration and testing by organizations that should be managing compliance, security, or governance.






