Check Certificate Authority Health in Windows Server 2012 R2 Using PKIVIEW
As data and IT services become more distributed, whether it be accessing data from a mobile device or data in the cloud, securing access to IT resources becomes increasingly complex. Public Key Infrastructures (PKI) are increasingly required to enable new features in Windows Server, so in this Ask the Admin, I’ll show you how to use the PKIVIEW tool to check certification authority health.
Enterprise PKI
The Enterprise PKI tool, sometimes referred to simply as PKIVIEW, is invaluable for checking the status of your organization’s certification authorities (CA). It was first released as part of the Windows Server 2003 Resource Kit, but starting with Windows Server 2008 it is installed by default when you add the Active Directory Certificate Services (AD CS) role.
If you want to use PKIVIEW from a management workstation or server where AD CS is not installed, Active Directory Certificate Services Tools can be added as part of the Remote Server Administration Tools (RSAT). See “Remote Server Administration Tools (RSAT) for Windows 8: Download and Install” for more information about using RSAT with Windows 8.
Running PKIVIEW
PKIVIEW is not listed on the Tools menu in Server Manager. To run the tool, log on to your Windows Server 2012 R2 device where the certification authority is installed, switch to the Start screen, type pkiview.msc and press Enter.
In the left pane, the root and subordinate CAs registered with Active Directory are available to select. In my domain, I only have one root CA. Start by clicking on Enterprise PKI in the left pane, and you will see on the right the health status of all the registered CAs.
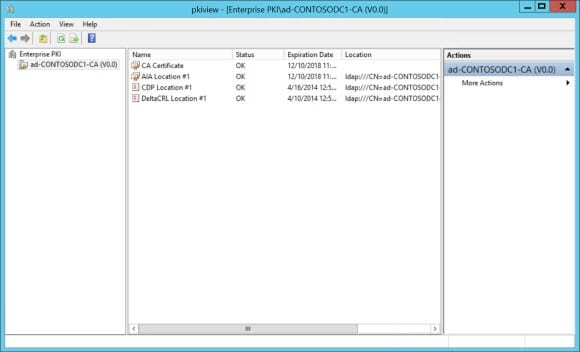
If you click a CA in the left pane, you’ll see information about the CA’s certificate, Authority Information Access (AIA) CRL Extension location, CRL Distribution Point (CDP) location, and DeltaCRL location, which should all be healthy for a properly functioning PKI. A yellow indicator signifies a non-critical problem, and a red indicator or red cross over a CA icon shows that there is a critical problem or that the CA is offline respectively.
Advanced Options
PKIVIEW allows you to manage Active Directory certificate and CRL stores. Right-click on Enterprise PKI in the left pane and select Manage AD Containers from the menu. The NTAuthCertificates tab lists CAs that can issue certs for RADIUS and smart card authentication, and allows you to add, remove, and view certificates.
The remaining tabs, including Key Recovery Agent (KRA) certificates for key archival, allow you to view and remove entries for each category. If you want to add new entries, you should use certutil at the command line.


