Security Researchers Discover New Windows Search Protocol Vulnerability

Security researchers have discovered a new zero-day vulnerability that allows hackers to launch a Windows search window via malicious Word documents. The security flaw exists in the Windows search protocol handler (search-ms) that allows applications and links to open searches for malicious attacks.
According to Bleeping Computer, an attacker could abuse the protocol handler to create a malicious Windows Update directory. The threat actors distributed the search-ms URI via phishing emails to trick users into installing the malware. However, many modern browsers (including Microsoft Edge) show security warnings to prevent users from running harmful executable files.
Additionally, security researchers have found a new vulnerability in Microsoft Office OLEObject. Attackers can exploit this flaw to bypass the Explorer preview pane and open a search window without any user intervention. It is also possible to create Rich Text Format (RTF) documents that can automatically launch a new search window each time a preview appears in the Preview Pane.
Workaround to fix Windows Search protocol vulnerability
Microsoft has yet to confirm this new protocol vulnerability in Windows 10 and Windows 11. As a workaround, the security researcher has recommended users to delete the search-ms protocol handler from Windows Registry by following the steps mentioned below:
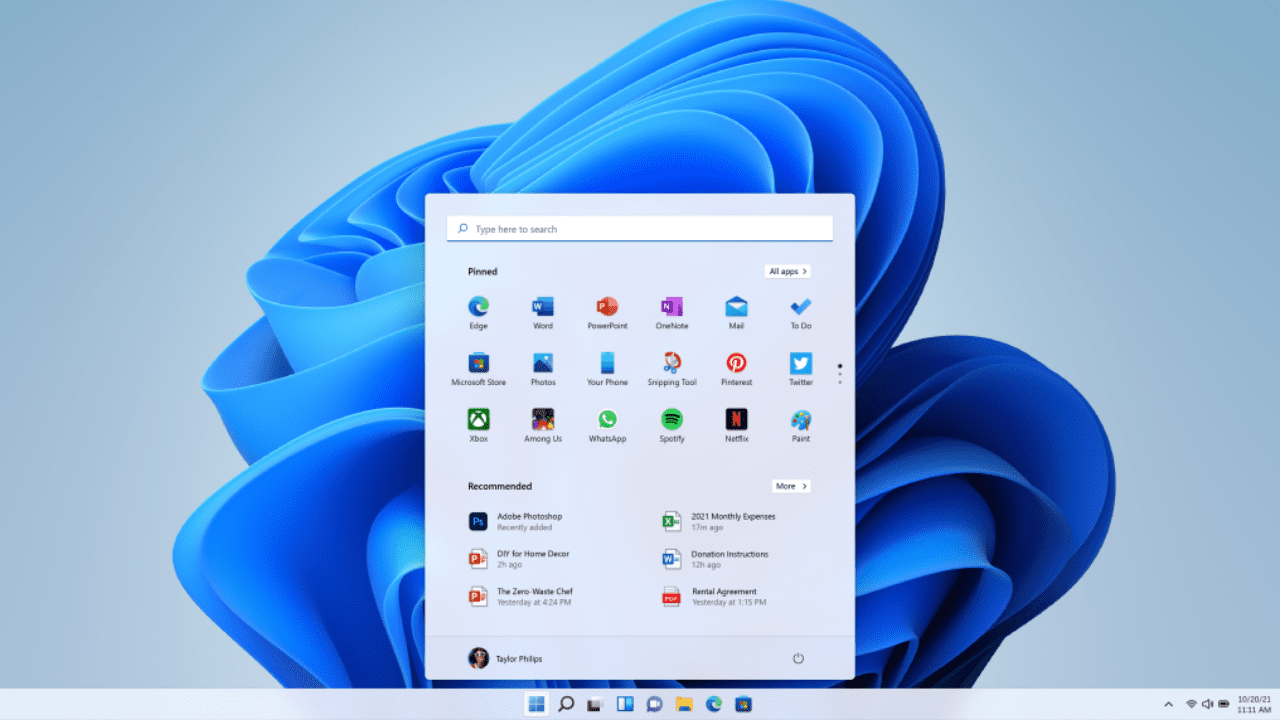
- First of all, type cmd in the search bar, right-click the Command Prompt option, and then choose Run as administrator from the list.
- Execute the command “reg export HKEY_CLASSES_ROOT\ms-msdt filename” in the command prompt window to create a back of the registry.
- Run the following command to remove the key from Windows Registry: reg delete HKEY_CLASSES_ROOT\search-ms /f
- Finally, close the Registry Editor and reboot your PC.
In case you missed it, Microsoft has also confirmed another zero-day flaw that lets hackers execute malicious PowerShell commands via the Microsoft Diagnostic Tool (MSDT) on Windows machines. Meanwhile, CISA has published an alert that urges IT Pros to apply temporary workaround solutions mentioned in Microsoft’s security advisory.