PingCastle – A Free Tool to Assess Active Directory Security

Are you looking to improve the security of your Active Directory environment? Learn how to set up the PingCastle Community Pack and strengthen your network defenses.
What is PingCastle?
PingCastle is a free, open-sourced tool designed to assess the security level of your Active Directory environment quickly. It’s based on a methodology focusing on risk assessment and a maturity framework. The goal of PingCastle is to offer an efficient report to assist with remediation, not a perfect, silver bullet.
🎬 Watch This Week in IT.
How does PingCastle help me learn about Active Directory vulnerabilities?
PingCastle uses several methods to assist you in learning about your security issues in AD and tips on how to resolve them. Here are some examples.
- Perform Security Controls Periodically – PingCastle ensures that a consistent set of actions are performed regularly. This includes checking for basic issues like provisioning, deletion, privileged accounts management, AD interconnections (trusts), and other vulnerabilities.
- Know Your Environment! – One of PingCastle’s first steps is to identify your Active Directory domains, assign them an owner (accountable for security), and check if all trusts to external parties have been removed or are at least secure.
- Document Processes – The tool helps document the processes that are already in place. This means the process to find hackers is in place and vulnerabilities are limited by a hardening project.
- Continuous Improvement – In this final step, the ‘well-oiled machine’ moniker comes into play as you’re provided with a method to keep new attacks at bay, and a constant periodic scanning schedule is put in place.
What main Active Directory vulnerabilities does PingCastle scan for?
Any good tool should scan for the most basic and critical vulnerabilities, in any product. But for Active Directory, it is all the more important. We’ve all read the stories of what hackers can do once they ‘get into’ your AD. Here are some common things the tool scans for.
- Privileged Accounts – The tool checks for issues related to accounts with special permissions. Identifying these accounts is crucial for knowing about privileged accounts you may not know.
- Stale Objects – The tool identifies accounts that haven’t been logged in in a long time, very old passwords, etc. These could be a big security risk.
- Trusts – PingCastle evaluates the existing trusts in your AD domains and lets you know if any of them are insecure by configuration or haven’t been validated in a while.
- Security Anomalies – The free tool looks for any suspicious or unusual activity that could indicate a breach. Unexpected changes in permissions, maybe repetitive bulk changes, are flagged as a high priority.
- Local Admin Privileges – The tool scans workstations for issues related to local administrators. If there are a larger number of accounts in the local Administrators group, you’ll want to know about it.
How can PingCastle solve my Active Directory security concerns?
The main focus and value of the tool is to provide you with a comprehensive assessment of your Active Directory security posture. By following the included steps when launching and using the tool, PingCastle can help you improve your AD security by identifying and addressing industry-recognized vulnerabilities effectively, and ensuring that your IT budget dollars are being utilized to remediate any holes discovered.
Check out our comprehensive comparison of Purple Knight vs PingCastle on Petri.com
Getting started – an overview of the tool
Let me show you how to start by downloading and using PingCastle in your environment. First, you can browse to download the software via PingCastle’s Download site.
Click the Download link, and extract the contents of the .zip file.
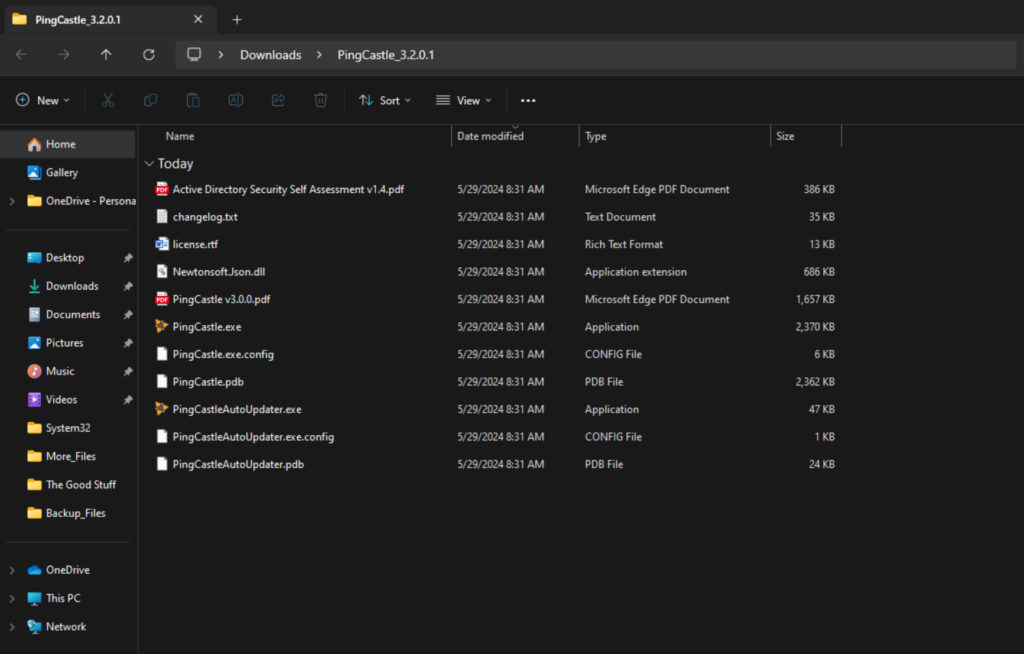
Next, double-click on PingCastle.exe, and a new command prompt opens with the main menu.
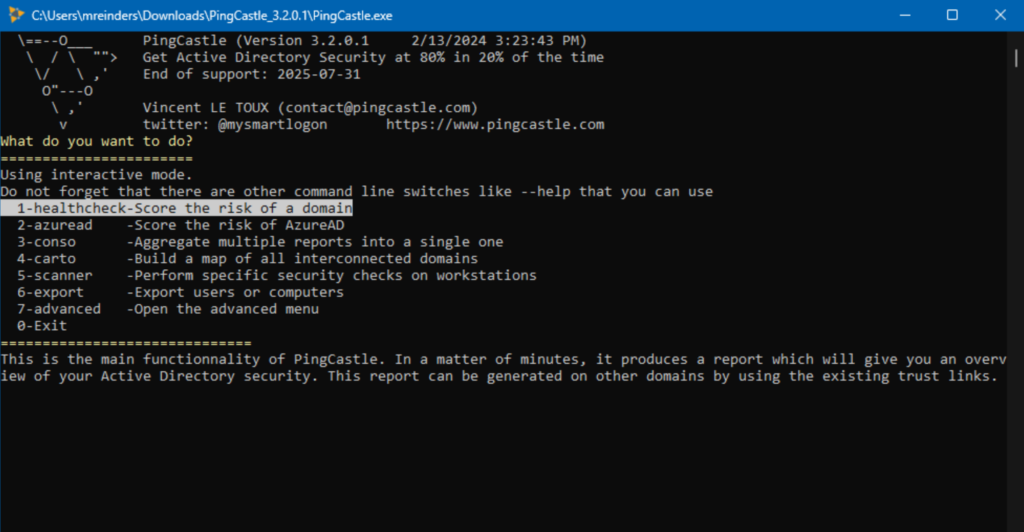
I will choose the first option – ‘1-healthcheck – Score the risk of a domain’. I typed in my domain, reinders.local, and the report was generated in less than a minute!
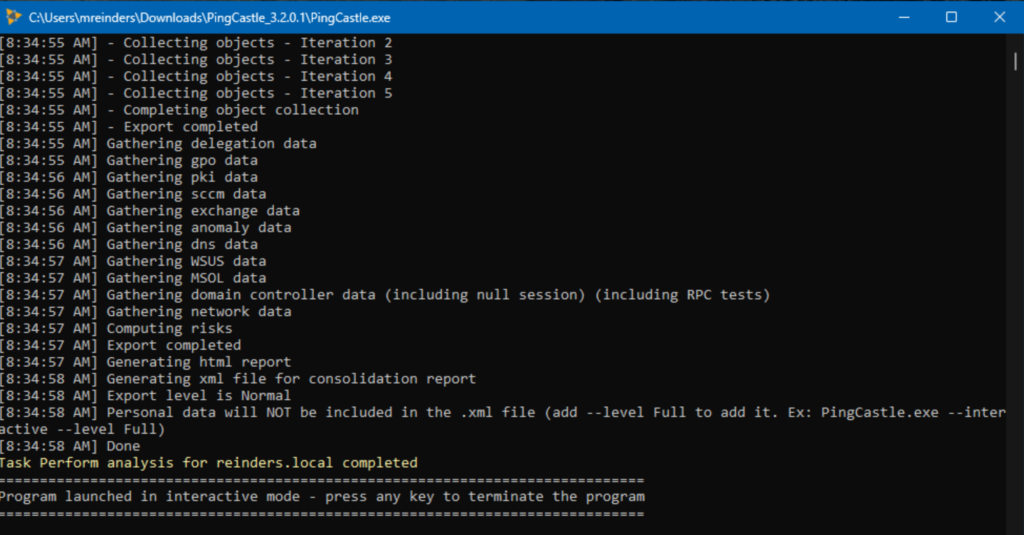
When it finished, I pressed a key and the command window closed. I went back to the downloaded folder and found the report. It is generated in HTML and XML formats. I opened the HTML version in Edge.

Here is a beautiful and effective Dashboard view that allows you to drill down into the report details and find remediation recommendations. I especially enjoy the time between visiting their website and getting a report to action on – less than 5 minutes.
Is there a cost associated with using PingCastle?
Because PingCastle is open-sourced and the fact that the code is released under the Non-Profit Open Software License (“Non-Profit OSL”), there is no cost to using the software. You can even have your cybersecurity and compliance teams download and audit the code before running the tool!
Conclusion
PingCastle is a powerful and comprehensive free tool designed for auditing and assessing the security of Active Directory environments. By offering detailed insights into potential vulnerabilities, misconfigurations, and compliance issues, PingCastle allows you and your organization to proactively identify and mitigate risks. Its user-friendly interface and thorough reporting capabilities make it accessible for both IT professionals and security experts, facilitating informed decision-making and robust security strategies.
In a time when cybersecurity is all but of the utmost importance, PingCastle serves as an invaluable resource for maintaining the integrity and security of Active Directory, ultimately helping organizations protect their critical digital assets from evolving threats. Petri also has a comprehensive list of free Active Directory tools if you want to check out what else is available.





