
A team of security researchers has discovered that attackers are now exploiting the critical Spring4Shell vulnerability to spread Mirai malware on target systems. The Mirai botnet malware attacks were first detected earlier this month, and the threat actors are currently targetting vulnerable web servers in the Singapore region.
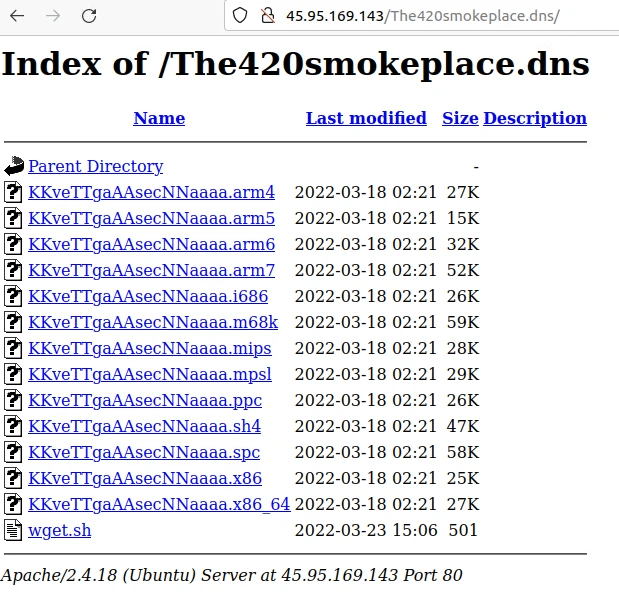
According to Trend Micro’s researchers, the threat actors have created a weaponized exploit that lets them successfully install Mirai on vulnerable systems. The security researchers explained that the malware file server stored multiple variants of Mirai designed for different CPU architectures. However, the blog post didn’t specifically mention the infected CPU or device type.
“We observed active exploitation of Spring4Shell wherein malicious actors were able to weaponize and execute the Mirai botnet malware on vulnerable servers, specifically in the Singapore region,” Trend Micro researchers explained. “We also found the malware file server with other variants for different CPU architectures.”
The Spring4Shell flaw enables attackers to gain remote access to the targetted device and download the Mirai sample to the “/tmp” folder. Once done, the threat actor can then execute the malware following a permission change via the “chmod” command.
Spring Framework versions affected by the Mirai botnet malware attacks
Here’s a list of the configurations that render systems vulnerable:
- Java Development Kit (JDK) version 9 or higher
- Apache Tomcat
- Spring Framework versions before 5.2.20, 5.3.18
- spring-webmvc or spring-webflux dependency
- Packaged as a traditional web application archive (WAR)
- Writable file system like ROOT or web apps
The Mirai botnet malware recently made headlines following a surge in attacks against Internet of Things (IoT) devices in 2020 and 2021. This malware is commonly used to launch distributed denial-of-service (DDoS) attacks, brute-force attacks, credential theft, ransomware deployment, etc.
VMware recommends IT Admins to upgrade to Spring Framework 5.3.18 and 5.2.20 as soon as possible to patch the Spring4Shell exploit. Meanwhile, Microsoft has also provided some detection and hunting capabilities to help its customers protect vulnerable devices in their organizations.



