
VMware has released emergency patches to address the “Spring4Shell” remote code execution exploit in the Spring Framework. The company is recommending all users to install these updates (version 5.3.18 and 5.2.20) as soon as possible.
The security researchers recently discovered a new zero-day exploit in the Spring Framework called “Spring4Shell” that could lead to unauthenticated remote code execution (RCE) on applications. The CVE-2022-22965 vulnerability was first reported to VMware by security researchers at AntGroup FG and impacts Spring Core on JDK (Java Development Kit) 9 and above.
“The vulnerability impacts Spring MVC and Spring WebFlux applications running on JDK 9+. The specific exploit requires the application to run on Tomcat as a WAR deployment. If the application is deployed as a Spring Boot executable jar, i.e. the default, it is not vulnerable to the exploit. However, the nature of the vulnerability is more general, and there may be other ways to exploit it,” Spring explained in its security advisory.
VMware has published a list of specific requirements that can be used to determine whether a Spring app is vulnerable:
- Apache Tomcat as the Servlet container
- Packaged as a traditional WAR (in contrast to a Spring Boot executable jar)
- spring-webmvc or spring-webflux dependency
- Spring Framework versions 5.3.0 to 5.3.17, 5.2.0 to 5.2.19, and older versions
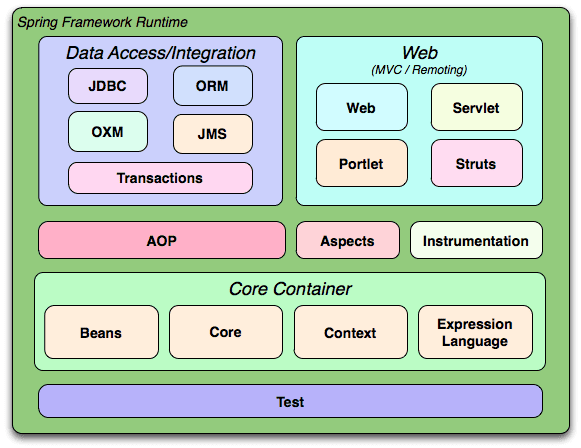
Spring is a lightweight open-source framework that allows developers to build robust, scalable, and secure Java-based enterprise applications. It can help to improve coding efficiency and reduce the time it takes to develop an application. The developers can deploy these applications as stand-alone packages (with all the dependencies) on servers like Apache Tomcat.
VMware recommends upgrades to Spring Framework 5.3.18 and 5.2.20
The cybersecurity company LunaSec explained that Spring4Shell shouldn’t be ignored, but it’s “NOT as bad” as the Log4Shell flaw. The researchers believe that the attack scenarios are a bit more complex, and attackers must have a high level of Java understanding to exploit them.
That said, security analysts Colin Cowie and Will Dormann have discovered that the Spring4Shell vulnerability exploit worked against sample code provided by Spring.“If the sample code is vulnerable, then I suspect there are indeed real-world apps out there that are vulnerable to RCE,” Dormann explained.
VMware is urging Spring admins to upgrade to Spring Framework 5.3.18 and 5.2.20 in order to protect their applications from potential security threats. We invite you to check out this explainer post on GitHub to learn more about Spring4Shell.



