Microsoft Publishes Advisory About New Spring4Shell Cyberattacks

Microsoft has published details about a critical security vulnerability dubbed “Spring4Shell” in the Spring Framework for Java. The Redmond giant recommends its Azure cloud service customers to patch the critical remote code execution (RCE) exploit immediately.
Disclosed by the WMware owned Spring on March 31, the company has already deployed a hotfix to address the Spring4Shell flaw. The RCE vulnerability (CVE-2022-22965) could be exploited by threat actors by “sending specially crafted queries to servers running the Spring Core framework.”
Spring is a popular open-source framework that is used to develop enterprise-grade Java applications. Microsoft notes that the CVE-2022-22965 vulnerability has received a CVSS score of 9.8, and it affects JDK 9 or higher.
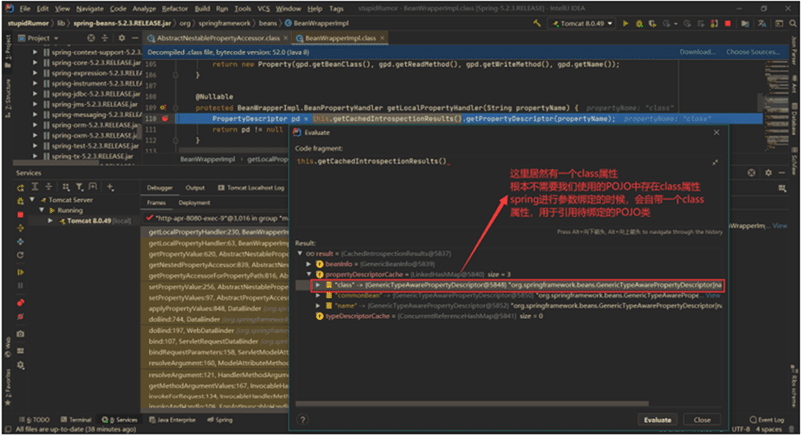
“In Java Development Kit (JDK) version 9.0 or later, a remote attacker can obtain an AccessLogValve object through the framework’s parameter binding feature and use malicious field values to trigger the pipeline mechanism and write to a file in an arbitrary path, if certain conditions are met,” the Microsoft Defender threat intelligence team explained.
Microsoft warns that some additional requirements for exploitation include:
- The application runs on Apache Tomcat
- The application is packaged as a traditional Java web archive (WAR) and deployed in a standalone Tomcat instance.
- The high-severity flaw impacts Spring Framework versions 5.3.0 to 5.3.17, 5.2.0 to 5.2.19, and older versions.
Spring4Shell: Discovery and mitigations
The company has provided a couple of hunting queries to help Microsoft Sentinel & Microsoft 365 Defender customers track the SpringShell exploitation activity in their organizations. Moreover, enterprise admins can use the following nonmalicious command to locate all vulnerable devices: curl host:port/path?class.module.classLoader.URLs%5B0%5D=0
The resolution suggested by Microsoft is to ensure that Spring Framework 5.3.18 and 5.2.20 or later is installed on devices impacted by Spring4Shell.
This announcement comes just days after the US Cybersecurity and Infrastructure Security Agency (CISA) added the Spring4Shell bug to its catalog of known exploited vulnerabilities. CISA also advised all US organizations to patch the security flaw as soon as possible. Security teams interested in investigating the Spring4Shell flaw can check out this explainer post on GitHub.






