Preventing Automatic Update to IE9 with Internet Explorer 9 Blocker Toolkit
Microsoft began to (or will shortly begin to, depending on the time you read this article) distribute Windows Internet Explorer 9 as a high-priority update through Automatic Updates for Windows Vista SP2 for x64 and x86, Windows Server 2008 SP2 for x64 and x86, Windows 7 x86 RTM and higher and Windows Server 2008 R2 RTM and higher for x64.
However, as with most large corporate environments, IT organizations may want to delay the introduction of a new Web browser until they have tested compatibility with internal applications and sites.
Microsoft created a tool called “Internet Explorer 9 Blocker Toolkit” to stop it from updating your desktops without your permission. The toolkit has no expiration date and can be configured either by running the registry file on the client machines, or through Group Policy in domain joined environments.
This Blocker Toolkit is intended for organizations that would like to block automatic delivery of Internet Explorer 9 to machines in environments where Automatic Updates is enabled.
Note that if you previously used the IE7 Blocker toolkit to block IE7 from installing itself, or the IE8 Blocker toolkit to block IE8, you will still need to run the IE9 version. This is because there are different registry keys used to block or unblock automatic delivery of Internet Explorer 7, Internet Explorer 8 and Internet Explorer 9.
Please note: While installation of IE9 may be delayed by administrators, I strongly recommend NOT to leave your machines running the older and ill-fated IE6 version. At least upgrade your browser version to the one prior to IE9.
If you configure the Internet Explorer 9 Blocker Toolkit setting to prevent users from installing Internet Explorer 9 through Windows Update or Automatic Updates, Internet Explorer 9 will not appear in the list of available high-priority or important updates.
If you configure the IE9 Blocker Toolkit setting to prevent users from installing IE9 via WU/AU, IE9 will not appear in the list of available high priority or important updates.
Note that the Internet Explorer 9 Blocker Toolkit will not prevent users from manually installing Internet Explorer 9 from the Microsoft Download Center.
Download
Get the Internet Explorer 9 Blocker Toolkit:
Download details: Toolkit to Disable Automatic Delivery of Internet Explorer 9
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=A6169467-B793-4D17-837D-01776BF2BEA4&displaylang=en
Toolkit Components
After downloading it, you’ll find that the toolkit contains two components:
- An executable blocker script
- A Group Policy Administrative Template (.ADM file)
Registry key
The script creates a registry key and sets the associated value to block or unblock (depending on the command-line option used) automatic delivery of Internet Explorer 9 on either the local machine or a remote target machine.
Registry key path: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Setup\9.0
Key value name: DoNotAllowIE90
- When the key value name is not defined, distribution is not blocked.
- When the key value name is set to 0, distribution is not blocked.
- When the key value name is set to 1, distribution is blocked.
Blocker Script
The script has the following command-line syntax:
IE90Blocker.cmd [<machine name>] [/B] [/U] [/H]
The <machine name> parameter is optional. If not specified, the action is performed on the local machine.
Switches used by the script are mutually exclusive and only the first valid switch from a given command is acted on. The Script can be run multiple times on the same machine without problem.
- /B – Blocks distribution
- /U – Unblocks distribution
- /H or /? – Displays the help
Group Policy Administrative Template (.ADM file)
The Group Policy Administrative Template (.ADM file) can be used to import the new Group Policy settings to block or unblock automatic delivery of Internet Explorer 9. This enables administrators to use Group Policy to centrally execute the action across systems in their environment.
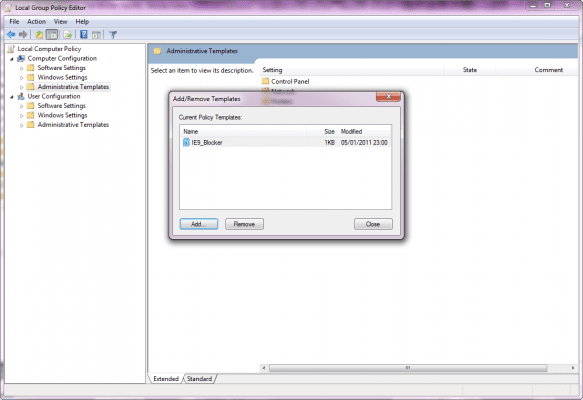
Add the .ADM file to the Group Policy by going to Computer Configuration > Administrative Templates. Right click and select Add/Remote Templates. Browse to the location of the .ADM file and click Ok.
In order to manage this setting, after adding this administrative template to the Group Policy Editor (GPMC), you must clear the “Only show policy settings that can be fully managed” option in the Filtering dialog before the new policy becomes visible in the Group Policy Editor. This option is found by highlighting “Administrative Templates”, then selecting “View” and then selecting “Filtering”.
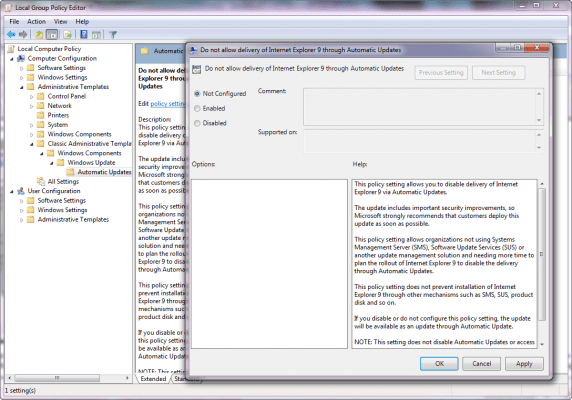
Users running Windows XP or Windows Server 2003 will see the policy under Computer Configuration > Administrative Templates > Windows Components > Windows Update > Automatic Updates Blockers v2.
Users running Windows Vista, Windows 7, Windows Server 2008 or Windows Server 2008 R2 will see the policy setting under Computer Configuration > Administrative Templates > Classic Administrative Templates (ADM) > Windows Components > Windows Update > Automatic Updates Blockers v3.
This setting is available only as a Computer setting; there is no Per-User setting.
Important note: This registry setting is not stored in a policies key and is thus considered a preference. Therefore if the Group Policy Object that implements the setting is ever removed or the policy is set to “Not Configured”, the setting will remain. To unblock distribution of Internet Explorer 9 using Group Policy set the policy to “Disabled”.
Additional information
Internet Explorer 9 – Blocker Toolkit, FAQ, Update | TechNet
http://technet.microsoft.com/en-us/ie/gg615600
IE8 vs IE9: What’s the Big Deal? | Train Signal Training