Mastering Active Directory OU: A Comprehensive Guide to Organizational Units

If you’ve been an IT Pro for many years (OK, decades), you likely know what an Active Directory OU (Organizational Unit) is. But, what if you’re new to the IT field or new to Microsoft Active Directory? No need to fret or get flustered – read my post to find out about OUs, what they are, and best practices for using them!
What is an Active Directory OU (Organizational Unit)?
An Organizational Unit (OU) in Active Directory is a container object used to organize and manage resources within a domain, such as users, groups, computers, printers, and other network objects. OUs provide a hierarchical structure that helps administrators logically group and delegate management of resource objects.
Benefits of using Active Directory OUs
Organizational Units (OUs) offer a number of benefits, including:
- Improved organization: OUs can be used to group objects in your Active Directory domain based on their function, department, location, or other criteria. This can make it easier to find and manage specific objects and to apply consistent Group Policy Objects (GPO) and settings. OU design can be daunting – take the time in the beginning to plan it out right.
- Delegated administration: OUs can be used to delegate administrative tasks to specific users or groups. This can help reduce the workload on IT staff and improve administration efficiency, especially when managing Group Policy settings.
- Security: OUs can be used to isolate objects from each other, and to restrict access to certain resources by way of Group Policy assignments. Group Policies are applied at the OU level. This allows you, as an example, to move three ‘standard’ printers in one OU and then the more expensive color laser printer in another and set a Group Policy to require PIN login to print to said device. This can help to improve security and reduce the risk of accidental or malicious changes or charges in your environment.
What is the difference between an Active Directory OU and a group?
In Active Directory (AD), both Organizational Units (OUs) and groups are fundamental components, but they serve distinct purposes and have different roles within the directory structure. Here, let me clarify the major differences:
- Purpose: OUs are for organizing objects (users, computers, printers, etc.), delegating administrative permissions, and for linking Group Policy Objects (GPOs). Group Policy is a means to efficiently lay down similar policy settings for your users and computers. On the other hand, security groups are used to grant permissions to specific resources.
- Delegation: OUs allow the delegation of administrative tasks within the OU. Groups do not have administrative delegation features.
- Group Policy: Group Policy Objects can be applied to OUs, allowing for configuration and policy enforcement. GPOs cannot be applied to groups.
- Access Control: OUs are used for controlling access to objects in the Active Directory database, whereas groups control access to resources, like printers and distribution lists.
Best Practices for using OUs
Here are some best practices for using Active Directory Organizational Units:
- Plan your OU structure ahead of time. Think about how you want to organize your users, computers, and other objects. Consider factors such as department, location, role, and type of device. Spending time before you start will pay dividends down the road for sure!
- Use a consistent naming convention for your OUs. This will make it easier to find and manage OUs. For example, you could use the following naming convention: OU=[Dept]_[Location-Site]
- Create separate OUs for users, computers, and servers. This will simplify Group Policy management.
- Use OU nesting to create a hierarchical OU structure. This will allow you to apply Group Policy and security settings to specific groups of objects within your organization. This works wonderfully when you are managing various versions of Windows client and server operating systems!
- Delegate administrative permissions to OUs. This will allow you to distribute administrative tasks throughout your organization. This needs to be secure and locked down!
- Document your OU structure. This will help you and other administrators to understand how your OUs are organized and how they are used.
What is the default Active Directory Organizational Unit structure?
When you install a new forest or domain in Active Directory, a default OU structure or template, per se, is laid out. Here are the details:
- Domain Controllers OU – This OU contains all of the domain controllers in the domain.
- Computers OU – This OU contains all of the computer accounts in the domain.
- Users OU – This OU contains all of the user accounts in the domain.
- Built-in container – This container contains special accounts and groups that are used by the Active Directory service.
You can create additional OUs and move objects between OUs to meet your organization’s needs of course. For example, you could create an OU for each department in your organization, and/or an OU for each office location.
It is important to note that the default OU structure is just a starting point. You should design an OU structure that is specific to your needs.
Examples of using Active Directory Organizational Units
There are many ways to logically create and design your Active Directory Organizational Unit structure and framework. Let me list the most common examples of how you can focus your design efforts to allow for seamless and simple design in this arena.
- To group objects by department: You could create OUs for each department in your organization, such as Sales, Marketing, and IT. This would make it easier to manage and organize the objects and to apply consistent policies and settings.
- To group objects by location: You could create OUs for each office location in your organization, such as Milwaukee, Chicago, and Madison. This would make it easier to manage and organize the objects in each location, and to apply consistent policies and settings.
- Organize computers by type: Create an OU for each type of computer in your organization, such as Desktops, Laptops, Servers, and Printers. This will make it easier to apply Group Policy and security settings to computers based on their type.
- To group objects for security purposes: You could create OUs to isolate different groups of objects from each other. For example, you could create an OU for servers, and restrict access to this OU to authorized users.
With recent security events in mind, it is vital to make sure your Active Directory resources and administrative permissions are clearly understood and secure. Here are some specific examples of how OUs can be used to delegate permissions in a secure and robust manner:
- You can delegate administrative permissions to a specific OU that contains mission-critical computer (server) objects. You can then delegate only a small handful of admins to this OU.
- You can delegate administrative permissions to the Servers OU to a member of the IT department. This will allow the IT department members to manage servers in the Servers OU, but they will not be able to manage users and computers in other OUs.
- You should certainly delegate specific admin permissions to the Domain Controllers OU. A good suggestion is to delegate to a single security group. Leave it empty at all times. Then, you can enable AD auditing so that the membership of the group is monitored and audited.
How to Create an Active Directory Organizational Unit
OUs can be created and managed using various tools as part of the Active Directory Domain Services (AD DS) role in Windows Server. The Active Directory Users and Computers (ADUC) console, which is part of the Remote Administration Administrative Tools (RSAT), PowerShell, or the Active Directory Administrative Center (ADAC) are the most common.
Let me show you how to do each of these! You can access these tools directly on a Windows domain controller, or you can utilize best practices and install the Remote Server Administration Tools. You can visit this link to learn how on Windows 10/11 -> [link to RSAT article].
Using Active Directory Users and Computers
To create a new Organizational Unit (OU) in Active Directory Users and Computers (ADUC), right-click on the parent object for your OU and select New > Organizational Unit. Enter a name for the OU. If you want to protect this OU from accidental deletion, make sure the ‘Protect container from accidental deletion‘ checkbox is checked. Click OK to create the OU.
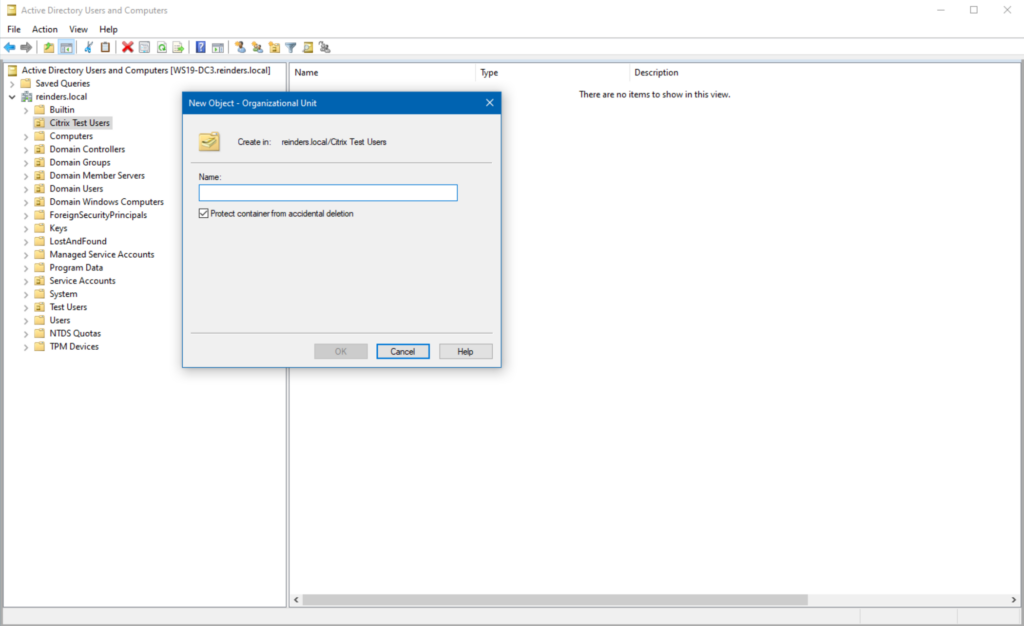
To manage an OU, right-click on the OU and select Properties. This will open the OU Properties dialog box, where you can view and edit the OU’s settings.
Using the Active Directory Administrative Center
If you click the Start Menu and search for ‘Active Directory’, you will find the Active Directory Administrative Center. Go ahead and click on it to open it. Then, click on the parent container for your new OU. On the Tasks menu on the right, click New -> Organizational Unit.
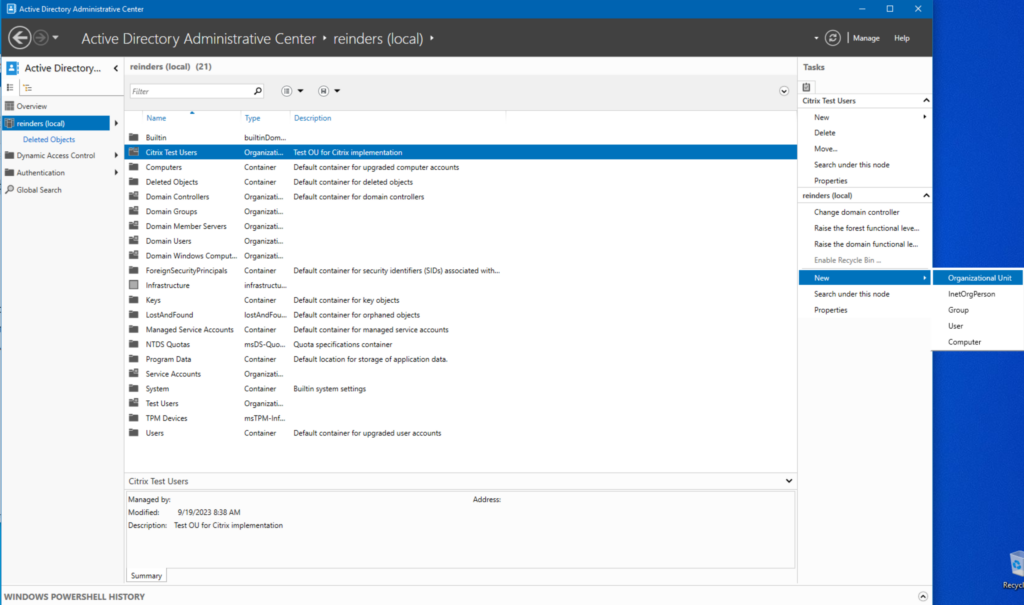
I have filled in the Name and the Description. That is all we typically need. Click OK. Piece of cake!
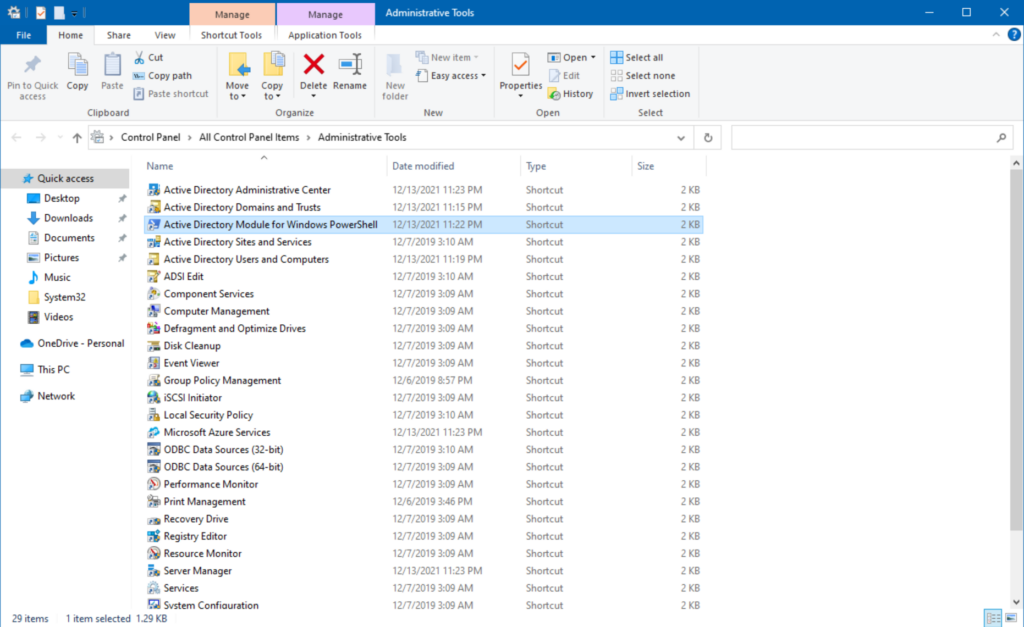
Using PowerShell
From the same Administrative Tools menu, we can launch the Active Directory Module for Windows PowerShell.
Let’s use the following cmdlet – New-ADOrganizationalUnit – thusly.
New-ADOrganizationalUnit -Name “CitrixTestUnit” -Path “DC=reinders,DC=local”
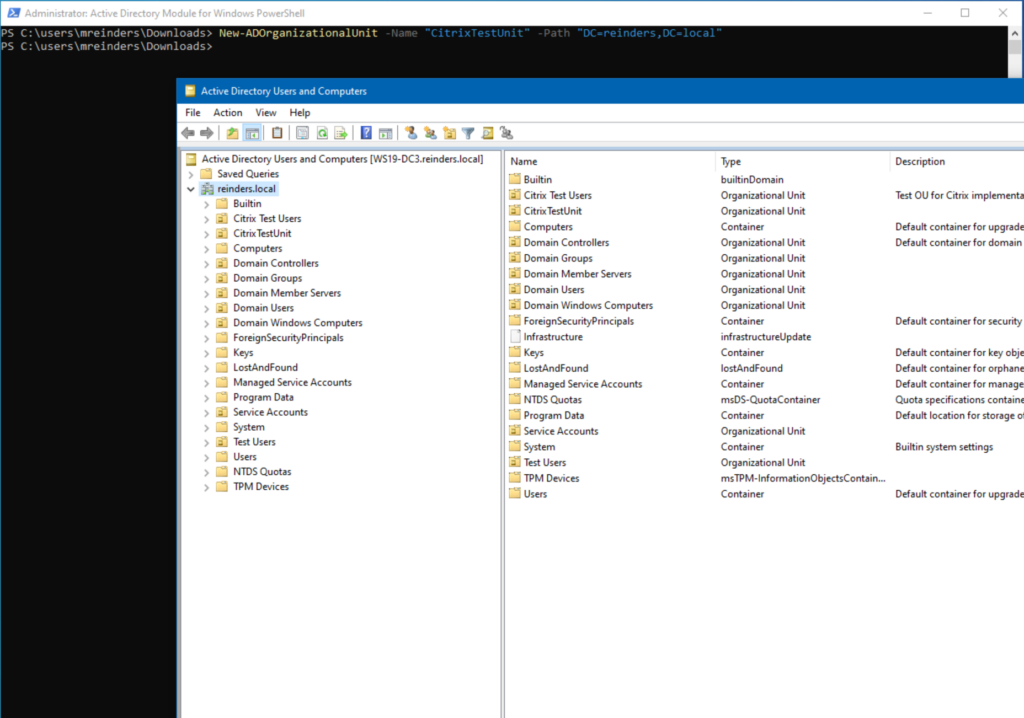
And there it is!
How to delegate Active Directory permissions to Organizational Units?
One of the most powerful features of OUs in AD is the ability to delegate administrative privileges/permissions to a single OU. Let’s use the ADUC tool. Right-click on the OU in question and click Delegate Control.
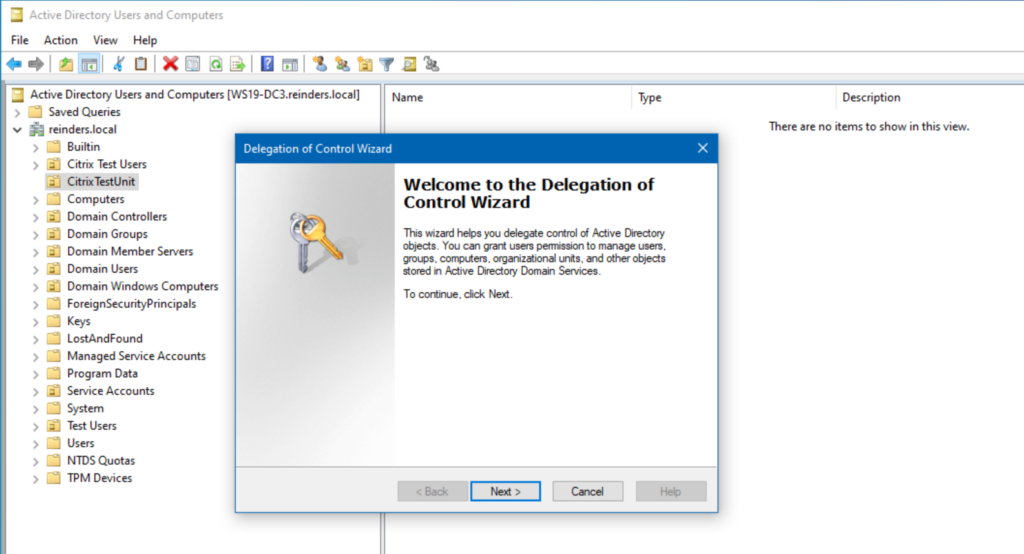
Now, we can go through the wizard and grant permissions to the OU. This will allow the delegated users (and/or groups) to perform the specified steps for all objects in that OU. Click Next.
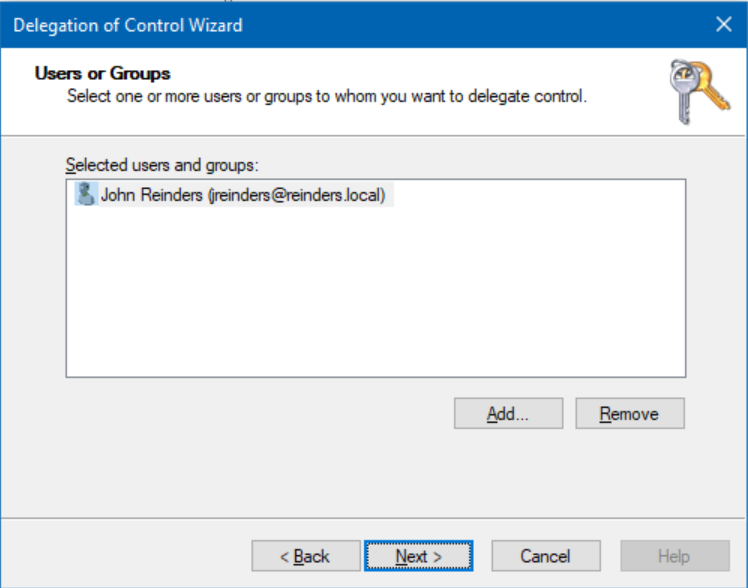
I have selected ‘John Reinders‘. He will receive the permissions defined in the next step.
[image]
After clicking Next, I will choose ‘Reset user passwords and force password change at next logon‘ and ‘Create, delete and manage groups‘. Click Next. On the final screen, review the info and click Finish. Done!
Active Directory OUs improve management
Active Directory Organizational Units (OUs) are a cornerstone of efficient network administration. They enable hierarchical organization, granular delegation, Group Policy application, access control to AD objects, and streamlined resource management within an organization’s directory.
By following best practices such as careful planning, clear naming conventions, and strategic delegation, administrators can maximize the benefits of OUs while maintaining an organized and secure Active Directory structure. As part of an IT Pro’s common administrative tasks, ongoing monitoring, documentation, and disaster recovery planning further contribute to the effective management of OUs and consequently, a well-functioning AD environment.
Table of contents
- What is an Active Directory OU (Organizational Unit)?
- Best Practices for using OUs
- What is the default Active Directory Organizational Unit structure?
- Examples of using Active Directory Organizational Units
- How to Create an Active Directory Organizational Unit
- How to delegate Active Directory permissions to Organizational Units?
- Active Directory OUs improve management



