Why Learn the Active Directory Administrative Center?
For most seasoned professionals, the Active Directory Users and Computers (ADUC) tool is the go-to console for basic AD management, and to a lesser extent, the AD Sites and Services, and Domains and Trusts consoles. But since Windows Server 2008 R2, the Active Directory Administrative Center (ADAC) has provided an alternative that often gets overlooked.
Microsoft Management Console Vs. Active Directory Administrative Center
It’s true that in a simple AD environment, in which you have one forest, one domain, and a limited number of objects, ADUC can sometimes prove to be the most convenient tool for basic user management tasks, if only out of familiarity. But once environments start to be more complex, ADUC is far from the ideal tool.
ADUC’s GUI doesn’t lend itself to the inclusion of advanced features, hence the complete redesign for the Administrative Center, where new features such as PowerShell History Viewer can be more easily incorporated.
Global Search
ADAC offers better management of objects across multiple domains in a forest, including the ability to perform global searches – and not only against the restricted set of attributes held by Global Catalog servers. Complex searches can be constructed using the GUI or with LDAP if maximum flexibility is required. For more information on Global Search, see the post “How to Use Global Search in the Active Directory Administrative Center” on the Petri IT Knowledgebase.
Dynamic Access Control, Recycle Bin, and Fine-Grained Password Policies
Windows Server 2012 introduced Dynamic Access Control, a feature designed to simplify the mess of ACLs that are often used to grant users access to network resources. Dynamic Access Control is managed from the Active Directory Administrative Center, along with much-needed GUI front-ends for the Active Directory Recycle Bin and Fine-Grained Password Policies – both features that previously had to be configured and managed from the command line.
For more information on Fine-Grained Password Policies, see the article “How to Configure Fine-Grained Password Policy in Windows Server 2012 Using ADAC.” For details of the AD Recycle Bin, see “Enable the Active Directory Recycle Bin in Windows Server 2012.” There’s also a detailed four-part series on Dynamic Access Control starting with “Dynamic Access Control: Introduction to the Technology and Components.”
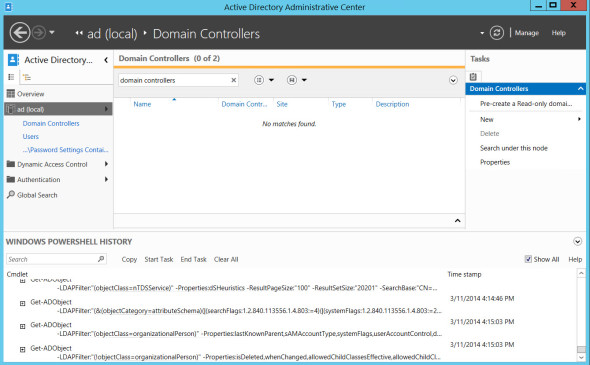
ADAC and Windows PowerShell History Viewer
One of the best features of ADAC is the PowerShell History Viewer. Not only can you see all your actions spelled out as PowerShell commands, which ADAC uses in the background to action all tasks, but it also preserves a history so you can look back and see what happened at a given time, which comes in handy for troubleshooting. For more information on PowerShell in ADAC, see “Use Active Directory Administrative Center to Create PowerShell Commands in Windows Server 2012” here on Petri IT Knowledgebase.
Raise Forest and Domain Functional Levels
ADAC includes the ability to raise forest and domain functional levels. Previously, the Domains and Trusts MMC was used to complete this task.
Improved GUI
Most of the common user attributes that helpdesks might need to configure are laid out clearly in a window that doesn’t involve those fiddly tabs found in the old ADAC pop-ups. It’s not until you get to the less frequently set object attributes that you still have to switch tabs, similar to the old ADUC console. Nevertheless, ADAC provides a more user-friendly way of navigating object attributes, which makes it ideal for helpdesk use.
While it’s still possible to view all your AD domains in a hierarchical view, this is not the default setting in ADAC. You can use search to find the object or Organizational Unit (OU) that you would like to work with. In large multi-domain forests, this makes managing AD simpler. ADAC will also remember recently accessed objects in the left pane, so you don’t have to search for them again.
Get Up To Speed With ADAC
If you’ve ignored ADAC till now, I recommend taking a look and making it your de facto tool for managing Active Directory. Not only is it handy for learning PowerShell, but there’s easy access to a wide range of functionality that was previously spread across several management consoles or only available from the command line.