Microsoft’s PrintNightmare Patch Not Effective Against Vulnerability
Late yesterday, Microsoft released a patch that was expected to close the vulnerability that is known as PrintNightmare. The patch, which you can install via Windows Update and was released out-of-band, was known to not fully address all instances of Windows and Server but now it looks like researchers have uncovered that the patch is ineffective against the vulnerability.
As of the time of this post, it is recommended that you disable the PrintSpooler service immediately to stop attacks on your environments using the zero-day exploit. And considering how widespread this exploit has been covered on sites like Petri and that several attempts to patch it have failed, malicious actors are likely increasing their scans for easy attack targets using the vulnerability.
If you are unsure if the service is running, you can take the following steps to determine if the service is running and how to disable the service with Group Policy:
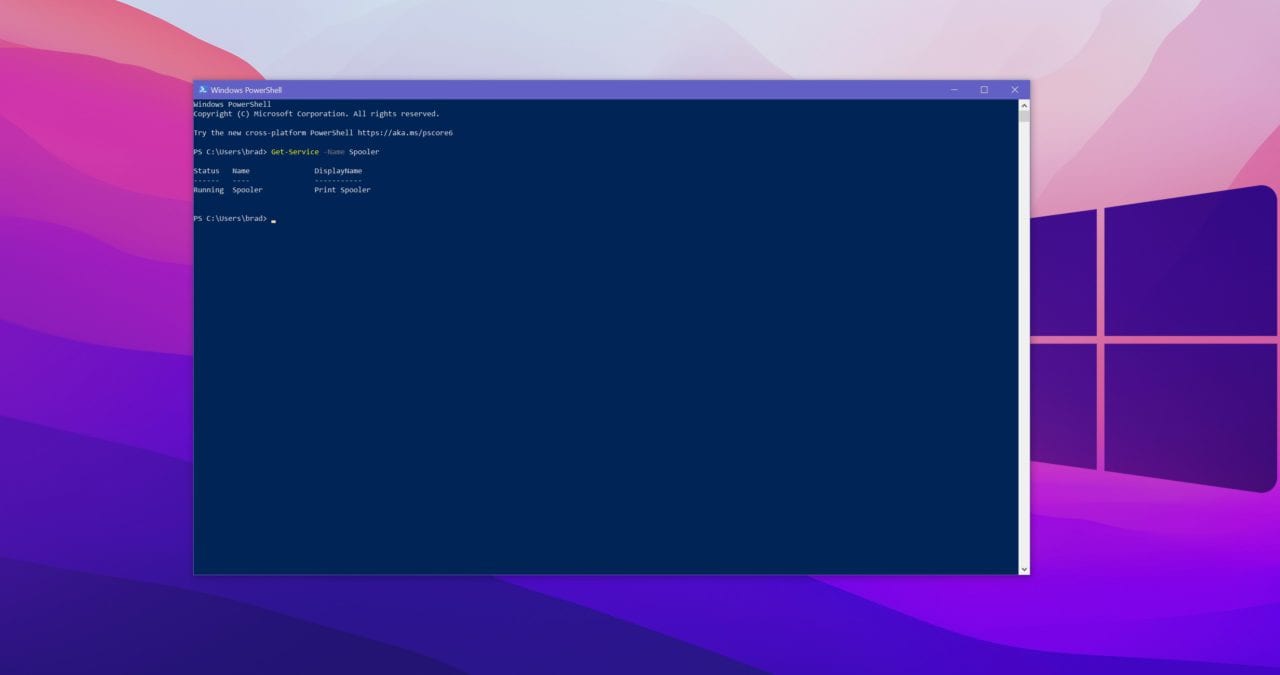
- Hit Windows Key and type PowerShell
- Enter the following command: Get-Service -Name Spooler
- If you see the words “running” this means the service is running.
If the Print Spooler is running or if the service is not set to disabled, select one of the following options to either disable the Print Spooler service, or to Disable inbound remote printing through Group Policy:
Option 1 – Disable the Print Spooler service
- If disabling the Print Spooler service is appropriate for your enterprise, use the following PowerShell commands:
- Stop-Service -Name Spooler -Force
- Set-Service -Name Spooler -StartupType Disabled
- Impact of workaround Disabling the Print Spooler service disables the ability to print both locally and remotely.
Option 2 – Disable inbound remote printing through Group Policy
- Computer Configuration / Administrative Templates / Printers
- Disable the “Allow Print Spooler to accept client connections:” policy to block remote attacks.
- You must restart the Print Spooler service for the group policy to take effect.
While disabling the service is easy on paper, the reality is that when you are working with thousands of servers and if you are responsible for managing multiple customers, this can be a serious headache. Add on top the fact that a patch was released which means admins have been up late patching only to learn that it’s not effective, and you have a recipe for serious frustration.
That does not include the fact that when the initial patch was released yesterday, not every version of Windows 10 or server was included.
But, it’s not like Microsoft is sitting idle and intentionally making this process more painful than it should be as releasing patches comes with its own risks of corrupting other functional parts of an operating system if not properly reviewed and tested before release. That being said, the PrintNightmare continues and for now, the only option is to disable PrintSpooler service.