Microsoft Azure: Enable Encryption for Data at Rest
In today’s Ask the Admin, I’ll show you how to enable encryption for blob storage in Microsoft Azure.
Microsoft announced the availability of Storage Service Encryption (SSE) in September 2016. This service allows you to add 256-bit AES encryption to new or existing storage accounts. Azure encrypts and decrypts data transparently to users and applications, as well as managing the service keys for you. Microsoft is also working on an option that will allow you to manage the service keys yourself.
Data is encrypted as it is written or rewritten to disk. This means that if you want to encrypt an entire blob, encryption needs to be enabled from the get go. Microsoft claims that the performance hit associated with SSE is inconsequential. Additionally, SSE is only supported for Azure Resource Manager (ARM) storage and blob storage accounts (i.e., those created using the new management portal or ARM PowerShell cmdlets).
SSE is available for blob storage in all regions. SSE for Azure File Service is available in preview. At the time of writing this article, SSE for Azure File Service can only be enabled for newly created ARM storage accounts in East US, East US2, Central US, North Central US, South Central US, West Central US, West US, West US2, East Asia, North Europe, West Europe, Australia East, and Australia Southeast regions. For more details on Azure storage accounts, see Understanding Azure Storage: Managed Disks and Storage Accounts on the Petri IT Knowledgebase.
Enable Encryption for Blob Storage
Before enabling encryption, you’ll need at least one storage account. For more information on creating storage accounts, see Create an Azure Premium Storage Account on Petri. For the purposes of this demonstration, a standard tier storage account can be used.
- Log into the Azure management portal.
- Click More services at the bottom of the panel on the left of the management portal window.
- Type storage in the box at the top of the new panel, and then click Storage accounts in the results.
- Click your storage account in the Storage accounts pane.
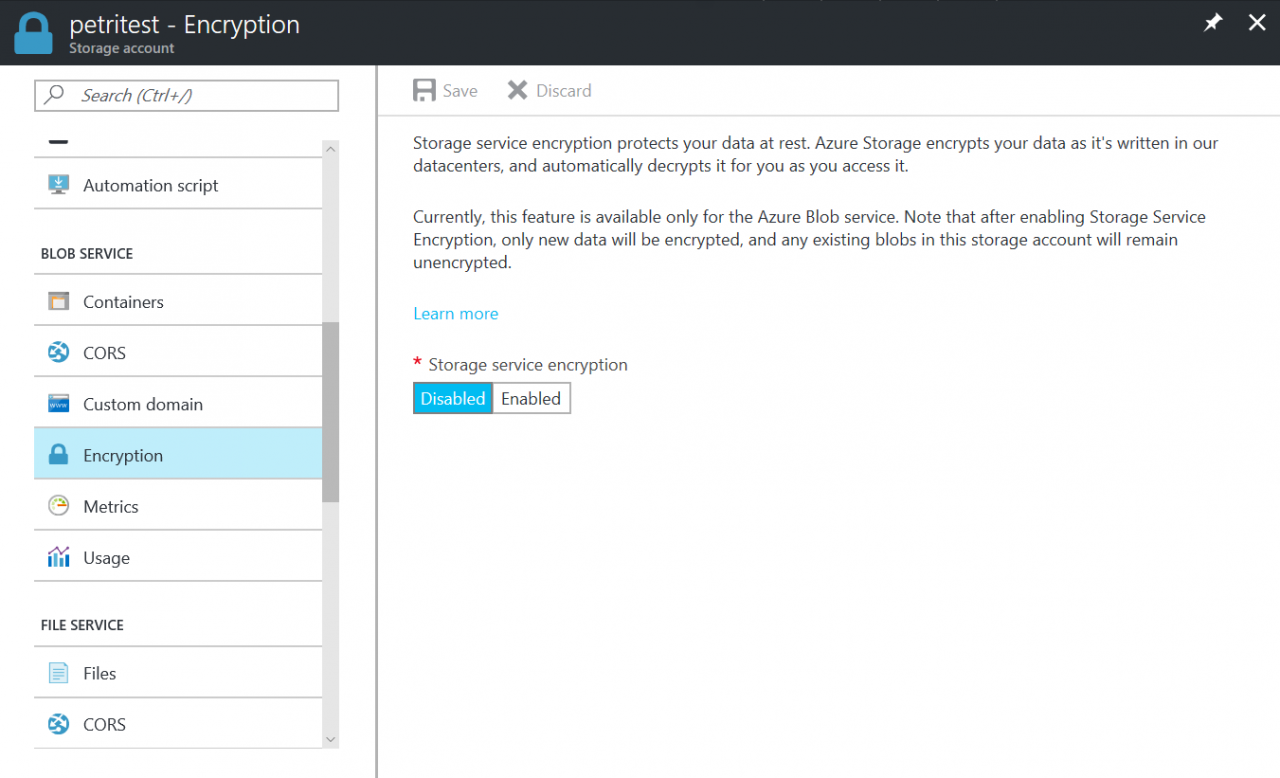
- On the Storage account panel, click Encryption under BLOB SERVICE.
- Toggle the Storage service encryption switch to Enabled, and then click Save at the top of the panel.
Azure will take a few moments to update the encryption settings for the storage account. If encryption is later disabled, new writes will not be encrypted. Keep in mind, existing data remains encrypted unless it gets rewritten to disk.
In this article, I showed you how to enable encryption in Azure for data at rest.




