
With a little help from Power Bi and Azure Log Analytics, Microsoft’s new Project VAST promises to make it easier to identify important security events. At the end of March, Microsoft unveiled Project VAST or the Visual Auditing Security Tool (VAST). VAST takes different SIEM products that aggregate security logs by providing rich interactive data visualization so that organizations can get a better idea of security vulnerabilities. VAST also works alongside existing security solutions, including Advanced Threat Analytics.
In a recent blog post, Microsoft states that many of its customers struggle withsecurity-relatedd activities, such as:
- removing deprecated protocols
- securing LDAP traffic
- controlling service accounts
- enforcing compliant use of Privileged Access Workstations (PAWs)
- safeguarding privileged accounts
- understanding authentication patterns
Project VAST visualizes big data, like aggregated log sets that contain a lot of useful information but that are difficult to effectively make use of. VAST works be capturing domain controller events and aggregating the results using Azure Log Analytics. A new query language (Kusto Query) is then used to find relevant event data in Azure and transfer the information to Power BI. Once in Power BI, the data is displayed visually to help security administrators make intelligence-driven decisions in near real-time.
With the help of Kusto, VAST pinpoints exactly the data which is needed for VAST’s detections and key performance indicators (KPIs). Kusto is borrowed from the Azure AppInsights team and promises to significantly improve Azure Log Analytics, allowing large datasets to be queried faster and making it easier for engineers to construct queries.
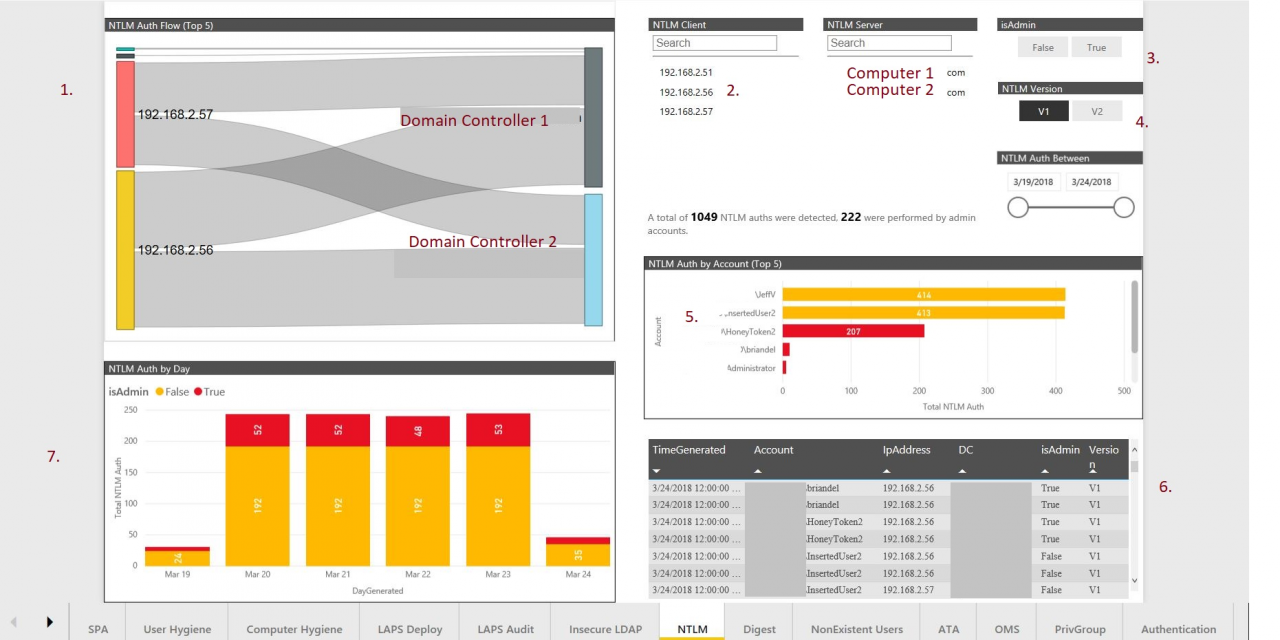
The data in Power BI is separated into tabs, each one representing a vulnerability. The GUI is designed to help organizations discover vulnerabilities and then take specific actions to resolve them. The screenshot below shows how the NTLM authentication protocol is being used in the organization. NTML is a deprecated protocol. The dashboard shows how NTLM traffic flows between clients and servers, and filters can be used to further understand how NTLM is being used. With this information, Microsoft hopes that customers will be able to move towards disabling deprecated protocols like NTLM. Until now, the worry has been that disabling deprecated features could break something. But with VAST, it should be easier for organizations to take concrete steps to improve the security posture.
At the moment, VAST is only available in preview form for Microsoft Premier Customers. But hopefully, VAST will be made more widely available in the coming months as Microsoft shares more information. I think it’s likely that Microsoft will turn VAST into a subscription-based Azure service once the technology has been proven.



