Microsoft Looks to Improve Azure Active Directory Compliance and Security Breach Prevention
Microsoft recently announced that it acquired CloudKnox Security, a security management solution for businesses that use more than one cloud service provider. CloudKnox says that its solutions help IT departments “granular visibility, actionable insights, and control of machine and human identities with excessive high-risk privileges.”
Joy Chik, who is corporate vice president for Microsoft Identity, says that organizations don’t have tools to monitor and assess multicloud permissions. CloudKnox started life as an activity-based authorization product that tracks identity information across Amazon Web Services (AWS), Google Cloud Platform, Microsoft Azure, and VMware vSphere.
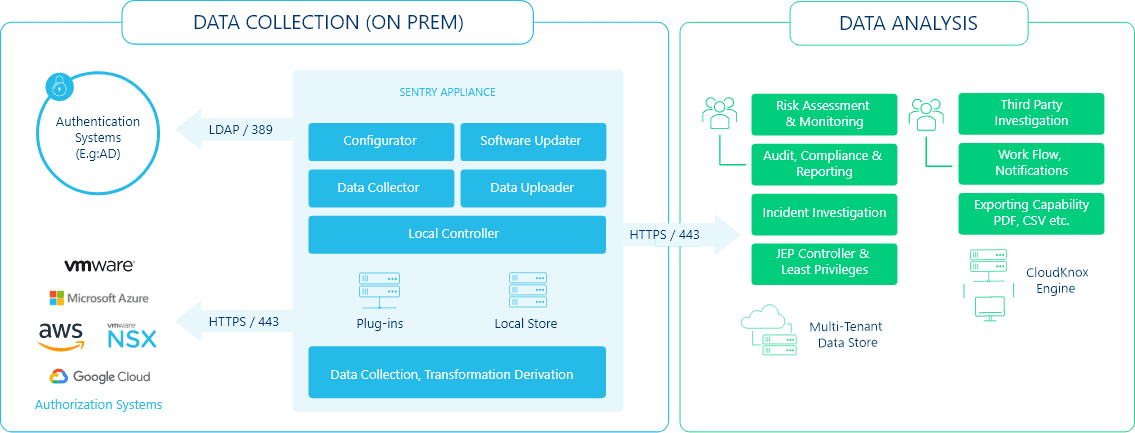
Today, the CloudKnox Cloud Security Platform consists of two components: Sentry and FortSentry. Sentry uses a Linux virtual machine installed in the customer’s environment. One Sentry appliance is required per cloud platform. Sentry collects privilege and activity information from each cloud platform and then sends the data to FortSentry.
CloudKnox claims that installation usually takes less than 30 minutes and once installed, data is pulled immediately from a cloud platform to the Sentry appliance. It then takes around 3 to 4 hours to collect three months’ data, providing a “three-dimensional view of all your machine and human identities, their actions (privileges) and the resources they have accessed at which point you can begin to protect your infrastructure from insider threats.”
Least Privilege for Identity and Access Management
CloudKnox helps IT departments apply the principle of least privilege to Identity and Access Management platforms across multiple cloud solutions. Just as it was and still is a problem for on-premises systems, users are often assigned more privileges in the cloud than required to perform their work duties.
Default roles are often used as a starting point when giving users initial access to cloud apps and infrastructure. Additional permissions or entitlements are then added as required. But even the default roles can lead to users receiving excessive or unused entitlements, which leads to increased risk for the organization.
Cloud Infrastructure Entitlement Management
CloudKnox is a next generation Cloud Infrastructure Entitlement Management (CIEM) solution that is designed to address the shortcomings of today’s Identity and Access Management platforms, like Azure Active Directory.
CIEM is based on a lifecycle framework that continuously discovers, manages, and monitors the activity of every identity, human and machine, over multiple cloud, and on-premises infrastructure. It also helps organizations enforce the principle of least privilege.
CloudKnox says that the CIEM framework is based on the following three stages:
- Discover risk by uncovering who (identities) is doing what (actions), where (resources), and when across your cloud infrastructure
- Apply the least privilege principle to manage risk which is ensuring identities have the least number of permissions needed to perform daily tasks for a specific amount of time
- Monitor risk by continuously tracking and measuring changes in identity activity (behavior) and prioritizing alerts based on pre-defined risk criteria
Microsoft will use CloudKnox to further enable zero-trust security
Zero trust is a security framework that stems from the idea you shouldn’t trust anyone and always assume breach. Microsoft’s identity-centric zero trust model requires that every user accessing an application must be verified.
Zero-trust takes identity as the first line of defense. It lets organizations implement the strongest security and at the same time improve business agility. The acquisition of CloudKnox will allow Microsoft to help its customers more easily enforce least privileged access in the cloud.
As Microsoft integrates CloudKnox into its solutions, it will provide Azure Active Directory with granular visibility, continuous monitoring, and automated remediation for hybrid and multi-cloud environments. Microsoft says that it is committed to automating and simplifying access policy enforcement; providing the widest range of signal-enabling and precision-based machine learning detections; and seamless integration with other Microsoft cloud security services, including Azure Sentinel.