July Patch Tuesday Updates Are Out With ‘Moment 3’ Features
Microsoft has released today the July Patch Tuesday updates for Windows 11 and Windows 10. The KB5028185 patch for Windows 11 version 22H2 brings the new “Moment 3” features that Microsoft previously made available in the optional update released in the last week of June.
Microsoft’s patches for July 2023 also include fixes for 130 vulnerabilities in Windows, Office, Visual Studio, and other components. Five of these vulnerabilities are already being exploited by attackers, which is pretty high.
July 2023 Patch Tuesday updates fix 130 vulnerabilities
As pointed out by the Zero Day Initiative today, Microsoft releasing 130 security fixes this month is “the highest we’ve seen in the last few years, although it’s not unusual to see Microsoft ship a large number of patches right before the Black Hat USA conference.” In addition to five “important” security flaws already being exploited by attackers, the list also includes nine vulnerabilities labeled as “critical”.
Here is what you know about the five vulnerabilities that are already being exploited by attackers:
CVE-2023-36884: This Office and Windows HTML Remote Code Execution vulnerability requires attackers to create a specially crafted Microsoft Office document to perform remote code execution.
CVE-2023-35311: This Microsoft Outlook Security Feature Bypass vulnerability requires users to click on a specially crafted URL to have their device compromised by the attacker.
CVE-2023-36874: Windows Error Reporting Service Elevation of Privilege vulnerability requires attackers to have local access to the targeted machine to gain administrator privileges.
CVE-2023-32046: This Windows MSHTML Platform Elevation of Privilege vulnerability also requires that a user open a specially crafted file to gain the rights of the user that is running the affected application.
CVE-2023-32049: This Windows SmartScreen Security Feature Bypass vulnerability allows attackers to bypass the Open File – Security Warning prompt after a user clicks on a specially crafted URL.
You can find below the full list of security patches Microsoft released this month:
| Product | Impact | Max Severity | Article | Download | Details |
| Microsoft Visual Studio 2022 version 17.0 | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2023-33127 |
| Microsoft Dynamics 365 (on-premises) version 9.0 | Spoofing | Important | 5026500 | Security Update | CVE-2023-32052 |
| Microsoft Dynamics 365 (on-premises) version 9.1 | Spoofing | Important | 5026501 | Security Update | CVE-2023-32052 |
| Windows Server 2012 R2 (Server Core installation) | Remote Code Execution | Critical | 5028228 | Monthly Rollup | CVE-2023-35367 |
| Windows Server 2012 R2 (Server Core installation) | Remote Code Execution | Critical | 5028223 | Security Only | CVE-2023-35367 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 | Remote Code Execution | Critical | 5028222 | Monthly Rollup | CVE-2023-35367 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 | Remote Code Execution | Critical | 5028226 | Security Only | CVE-2023-35367 |
| Windows Server 2016 (Server Core installation) | Remote Code Execution | Critical | 5028169 | Security Update | CVE-2023-35367 |
| Windows Server 2016 | Remote Code Execution | Critical | 5028169 | Security Update | CVE-2023-35367 |
| Windows Server 2019 | Remote Code Execution | Critical | 5028168 | Security Update | CVE-2023-35367 |
| Windows 10 Version 1809 for ARM64-based Systems | Remote Code Execution | Critical | 5028168 | Security Update | CVE-2023-35367 |
| Windows 10 Version 1809 for x64-based Systems | Remote Code Execution | Critical | 5028168 | Security Update | CVE-2023-35367 |
| Windows 10 Version 1809 for 32-bit Systems | Remote Code Execution | Critical | 5028168 | Security Update | CVE-2023-35367 |
| Windows Server 2012 R2 | Remote Code Execution | Critical | 5028228 | Monthly Rollup | CVE-2023-35366 |
| Windows Server 2012 R2 | Remote Code Execution | Critical | 5028223 | Security Only | CVE-2023-35366 |
| Windows Server 2022 (Server Core installation) | Remote Code Execution | Important | 5028171 | Security Update | CVE-2023-35309 |
| Windows Server 2022 | Remote Code Execution | Important | 5028171 | Security Update | CVE-2023-35309 |
| Windows Server 2019 (Server Core installation) | Remote Code Execution | Important | 5028168 | Security Update | CVE-2023-35309 |
| Windows 10 Version 1607 for x64-based Systems | Information Disclosure | Important | 5028169 | Security Update | CVE-2023-35306 |
| Windows 10 Version 1607 for 32-bit Systems | Information Disclosure | Important | 5028169 | Security Update | CVE-2023-35306 |
| Windows 10 for x64-based Systems | Information Disclosure | Important | 5028186 | Security Update | CVE-2023-35306 |
| Windows 10 for 32-bit Systems | Information Disclosure | Important | 5028186 | Security Update | CVE-2023-35306 |
| Windows 10 Version 22H2 for 32-bit Systems | Information Disclosure | Important | 5028166 | Security Update | CVE-2023-35306 |
| Windows 10 Version 22H2 for ARM64-based Systems | Information Disclosure | Important | 5028166 | Security Update | CVE-2023-35306 |
| Windows 10 Version 22H2 for x64-based Systems | Information Disclosure | Important | 5028166 | Security Update | CVE-2023-35306 |
| Windows 11 Version 22H2 for x64-based Systems | Information Disclosure | Important | 5028185 | Security Update | CVE-2023-35306 |
| Windows 11 Version 22H2 for ARM64-based Systems | Information Disclosure | Important | 5028185 | Security Update | CVE-2023-35306 |
| Windows 10 Version 21H2 for x64-based Systems | Information Disclosure | Important | 5028166 | Security Update | CVE-2023-35306 |
| Windows 11 version 21H2 for x64-based Systems | Elevation of Privilege | Important | 5028182 | Security Update | CVE-2023-35305 |
| Windows 10 Version 21H2 for ARM64-based Systems | Remote Code Execution | Important | 5028166 | Security Update | CVE-2023-35303 |
| Windows 10 Version 21H2 for 32-bit Systems | Remote Code Execution | Important | 5028166 | Security Update | CVE-2023-35303 |
| Windows 11 version 21H2 for ARM64-based Systems | Remote Code Execution | Important | 5028182 | Security Update | CVE-2023-35303 |
| Windows Server 2012 (Server Core installation) | Elevation of Privilege | Important | 5028232 | Monthly Rollup | CVE-2023-35299 |
| Windows Server 2012 (Server Core installation) | Elevation of Privilege | Important | 5028233 | Security Only | CVE-2023-35299 |
| Windows Server 2012 | Elevation of Privilege | Important | 5028232 | Monthly Rollup | CVE-2023-35299 |
| Windows Server 2012 | Elevation of Privilege | Important | 5028233 | Security Only | CVE-2023-35299 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) | Elevation of Privilege | Important | 5028240 | Monthly Rollup | CVE-2023-35299 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) | Elevation of Privilege | Important | 5028224 | Security Only | CVE-2023-35299 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 | Elevation of Privilege | Important | 5028240 | Monthly Rollup | CVE-2023-35299 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 | Elevation of Privilege | Important | 5028224 | Security Only | CVE-2023-35299 |
| Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) | Elevation of Privilege | Important | 5028222 | Monthly Rollup | CVE-2023-35299 |
| Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) | Elevation of Privilege | Important | 5028226 | Security Only | CVE-2023-35299 |
| Microsoft SharePoint Server Subscription Edition | Remote Code Execution | Critical | 5002424 | Security Update | CVE-2023-33160 |
| Windows 10 for x64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 for 32-bit Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 Version 22H2 for 32-bit Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 Version 22H2 for ARM64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 Version 22H2 for x64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 11 Version 22H2 for x64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 11 Version 22H2 for ARM64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 Version 21H2 for x64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 Version 21H2 for ARM64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Microsoft Visual Studio 2022 version 17.2 | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2023-33127 |
| Microsoft SharePoint Server 2019 | Remote Code Execution | Critical | 5002423 | Security Update | CVE-2023-33160 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) | Elevation of Privilege | Important | 5028222 | Monthly Rollup | CVE-2023-33154 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) | Elevation of Privilege | Important | 5028226 | Security Only | CVE-2023-33154 |
| Microsoft Office 2013 Service Pack 1 (64-bit editions) | Remote Code Execution | Important | 4464506 | Security Update | CVE-2023-33153 |
| Microsoft Office 2013 Service Pack 1 (32-bit editions) | Remote Code Execution | Important | 4464506 | Security Update | CVE-2023-33153 |
| Microsoft Office 2013 RT Service Pack 1 | Remote Code Execution | Important | 4464506 | Security Update | CVE-2023-33153 |
| Microsoft Office 2016 (64-bit edition) | Remote Code Execution | Important | 4475581 | Security Update | CVE-2023-33153 |
| Windows Server 2012 R2 (Server Core installation) | Security Feature Bypass | Important | 5028167 | IE Cumulative | CVE-2023-35308 |
| Windows Server 2012 R2 | Security Feature Bypass | Important | 5028167 | IE Cumulative | CVE-2023-35308 |
| Microsoft Office 2016 (32-bit edition) | Remote Code Execution | Important | 4475581 | Security Update | CVE-2023-33153 |
| Microsoft Office LTSC 2021 for 32-bit editions | Remote Code Execution | Important | Click to Run | Security Update | CVE-2023-33153 |
| Microsoft Office LTSC 2021 for 64-bit editions | Remote Code Execution | Important | Click to Run | Security Update | CVE-2023-33153 |
| Microsoft 365 Apps for Enterprise for 64-bit Systems | Remote Code Execution | Important | Click to Run | Security Update | CVE-2023-33153 |
| Microsoft 365 Apps for Enterprise for 32-bit Systems | Remote Code Execution | Important | Click to Run | Security Update | CVE-2023-33153 |
| Microsoft Office 2019 for 64-bit editions | Remote Code Execution | Important | Click to Run | Security Update | CVE-2023-33153 |
| Microsoft Office 2019 for 32-bit editions | Remote Code Execution | Important | Click to Run | Security Update | CVE-2023-33153 |
| Microsoft Office 2013 Service Pack 1 (64-bit editions) | Remote Code Execution | Important | 5002069 | Security Update | CVE-2023-33152 |
| Microsoft Office 2013 Service Pack 1 (32-bit editions) | Remote Code Execution | Important | 5002069 | Security Update | CVE-2023-33152 |
| Microsoft Office 2013 RT Service Pack 1 | Remote Code Execution | Important | 5002069 | Security Update | CVE-2023-33152 |
| Microsoft Office 2016 (64-bit edition) | Remote Code Execution | Important | 5002058 | Security Update | CVE-2023-33152 |
| Windows Server 2008 for x64-based Systems Service Pack 2 | Remote Code Execution | Critical | 5028222 | Monthly Rollup | CVE-2023-35366 |
| Windows Server 2008 for x64-based Systems Service Pack 2 | Remote Code Execution | Critical | 5028226 | Security Only | CVE-2023-35366 |
| Microsoft Office 2016 (32-bit edition) | Remote Code Execution | Important | 5002058 | Security Update | CVE-2023-33152 |
| Raw Image Extension | Remote Code Execution | Important | Update Information | Security Update | CVE-2023-32051 |
| .NET 6.0 | Security Feature Bypass | Important | 5028705 | Security Update | CVE-2023-33170 |
| Windows 10 Version 21H2 for 32-bit Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 11 version 21H2 for ARM64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 11 version 21H2 for x64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2022 (Server Core installation) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2022 | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2019 (Server Core installation) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2019 | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 Version 1809 for ARM64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 Version 1809 for x64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 Version 1809 for 32-bit Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Microsoft Visual Studio 2022 version 17.6 | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2023-33127 |
| Microsoft Visual Studio 2022 version 17.4 | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2023-33127 |
| Microsoft Word 2013 Service Pack 1 (64-bit editions) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Microsoft Word 2013 Service Pack 1 (32-bit editions) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Microsoft Word 2016 (64-bit edition) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Microsoft Word 2016 (32-bit edition) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Microsoft Office LTSC 2021 for 32-bit editions | Remote Code Execution | Important | CVE-2023-36884 | ||
| Microsoft Office LTSC 2021 for 64-bit editions | Remote Code Execution | Important | CVE-2023-36884 | ||
| Microsoft Office 2019 for 64-bit editions | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2012 | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2008 for x64-based Systems Service Pack 2 | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2008 for 32-bit Systems Service Pack 2 | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2016 (Server Core installation) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2016 | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 Version 1607 for x64-based Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows 10 Version 1607 for 32-bit Systems | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2012 R2 | Remote Code Execution | Important | CVE-2023-36884 | ||
| Windows Server 2012 (Server Core installation) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Microsoft Office 2019 for 32-bit editions | Remote Code Execution | Important | CVE-2023-36884 | ||
| Microsoft Outlook 2013 RT Service Pack 1 | Security Feature Bypass | Important | 5002432 | Security Update | CVE-2023-35311 |
| Microsoft Outlook 2013 (64-bit editions) | Security Feature Bypass | Important | 5002432 | Security Update | CVE-2023-35311 |
| Microsoft Outlook 2013 (32-bit editions) | Security Feature Bypass | Important | 5002432 | Security Update | CVE-2023-35311 |
| Microsoft Outlook 2016 (64-bit edition) | Security Feature Bypass | Important | 5002427 | Security Update | CVE-2023-35311 |
| Microsoft Outlook 2016 (32-bit edition) | Security Feature Bypass | Important | 5002427 | Security Update | CVE-2023-35311 |
| Microsoft Office for Universal | Remote Code Execution | Important | Release Notes | Security Update | CVE-2023-33158 |
| Microsoft Office LTSC for Mac 2021 | Remote Code Execution | Important | Release Notes | Security Update | CVE-2023-33158 |
| Microsoft Office 2019 for Mac | Remote Code Execution | Important | Release Notes | Security Update | CVE-2023-33158 |
| Windows Server 2012 R2 (Server Core installation) | Remote Code Execution | Important | CVE-2023-36884 | ||
| Paint 3D | Remote Code Execution | Important | Release Notes | Security Update | CVE-2023-32047 |
| .NET 7.0 | Security Feature Bypass | Important | 5028706 | Security Update | CVE-2023-33170 |
| Azure Service Fabric 9.1 for Windows | Information Disclosure | Important | Release Notes | Security Update | CVE-2023-36868 |
| Azure Service Fabric 9.0 for Windows | Information Disclosure | Important | Release Notes | Security Update | CVE-2023-36868 |
| VP9 Video Extensions | Information Disclosure | Important | More Information | Security Update | CVE-2023-36872 |
| Visual Studio Code – GitHub Pull Requests and Issues Extension | Remote Code Execution | Important | Release Notes | Security Update | CVE-2023-36867 |
| Mono 6.12.0 | Spoofing | Important | Release Notes | Security Update | CVE-2023-35373 |
| Microsoft SharePoint Enterprise Server 2016 | Remote Code Execution | Critical | 5002425 | Security Update | CVE-2023-33160 |
| PandocUpload | Remote Code Execution | Important | Release Notes | Security Update | CVE-2023-35333 |
| Windows Server 2012 (Server Core installation) | Elevation of Privilege | Important | 5028167 | IE Cumulative | CVE-2023-32046 |
| Windows Server 2012 | Elevation of Privilege | Important | 5028167 | IE Cumulative | CVE-2023-32046 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) | Elevation of Privilege | Important | 5028167 | IE Cumulative | CVE-2023-32046 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 | Elevation of Privilege | Important | 5028167 | IE Cumulative | CVE-2023-32046 |
| Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) | Elevation of Privilege | Important | 5028167 | IE Cumulative | CVE-2023-32046 |
| Windows Server 2008 for x64-based Systems Service Pack 2 | Elevation of Privilege | Important | 5028167 | IE Cumulative | CVE-2023-32046 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) | Elevation of Privilege | Important | 5028167 | IE Cumulative | CVE-2023-32046 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 | Elevation of Privilege | Important | 5028167 | IE Cumulative | CVE-2023-32046 |
| Microsoft Excel 2013 Service Pack 1 (64-bit editions) | Information Disclosure | Important | 5002434 | Security Update | CVE-2023-33162 |
| Microsoft Excel 2013 Service Pack 1 (32-bit editions) | Information Disclosure | Important | 5002434 | Security Update | CVE-2023-33162 |
| Microsoft Excel 2013 RT Service Pack 1 | Information Disclosure | Important | 5002434 | Security Update | CVE-2023-33162 |
| Microsoft Excel 2016 (64-bit edition) | Information Disclosure | Important | 5002426 | Security Update | CVE-2023-33162 |
| Microsoft Excel 2016 (32-bit edition) | Information Disclosure | Important | 5002426 | Security Update | CVE-2023-33162 |
| Microsoft Office Online Server | Information Disclosure | Important | 5002421 | Security Update | CVE-2023-33162 |
| Microsoft Malware Protection Engine | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2023-33156 |
| Microsoft Word 2013 Service Pack 1 (64-bit editions) | Security Feature Bypass | Important | 5002411 | Security Update | CVE-2023-33150 |
| Microsoft Word 2013 Service Pack 1 (32-bit editions) | Security Feature Bypass | Important | 5002411 | Security Update | CVE-2023-33150 |
| Microsoft Word 2013 RT Service Pack 1 | Security Feature Bypass | Important | 5002411 | Security Update | CVE-2023-33150 |
| Microsoft Word 2016 (64-bit edition) | Security Feature Bypass | Important | 5002406 | Security Update | CVE-2023-33150 |
| Microsoft Word 2016 (32-bit edition) | Security Feature Bypass | Important | 5002406 | Security Update | CVE-2023-33150 |
| Microsoft Office 2013 Service Pack 1 (64-bit editions) | Remote Code Execution | Important | 5002400 | Security Update | CVE-2023-33149 |
| Microsoft Office 2013 Service Pack 1 (64-bit editions) | Remote Code Execution | Important | 5001952 | Security Update | CVE-2023-33149 |
| Microsoft Office 2013 Service Pack 1 (32-bit editions) | Remote Code Execution | Important | 5002400 | Security Update | CVE-2023-33149 |
| Microsoft Office 2013 Service Pack 1 (32-bit editions) | Remote Code Execution | Important | 5001952 | Security Update | CVE-2023-33149 |
| Microsoft Office 2013 RT Service Pack 1 | Remote Code Execution | Important | 5002400 | Security Update | CVE-2023-33149 |
| Microsoft Office 2013 RT Service Pack 1 | Remote Code Execution | Important | 5001952 | Security Update | CVE-2023-33149 |
| Microsoft Office 2016 (64-bit edition) | Remote Code Execution | Important | 5002419 | Security Update | CVE-2023-33149 |
| Microsoft Office 2016 (64-bit edition) | Remote Code Execution | Important | 4493154 | Security Update | CVE-2023-33149 |
| Microsoft Office 2016 (32-bit edition) | Remote Code Execution | Important | 5002419 | Security Update | CVE-2023-33149 |
| Microsoft Office 2016 (32-bit edition) | Remote Code Execution | Important | 4493154 | Security Update | CVE-2023-33149 |
| Microsoft Office 2013 Click-to-Run (C2R) for 64-bit editions | Elevation of Privilege | Important | Click to Run | Security Update | CVE-2023-33148 |
| Microsoft Office 2013 Click-to-Run (C2R) for 32-bit editions | Elevation of Privilege | Important | Click to Run | Security Update | CVE-2023-33148 |
| Windows Admin Center | Spoofing | Important | Release Notes | Security Update | CVE-2023-29347 |
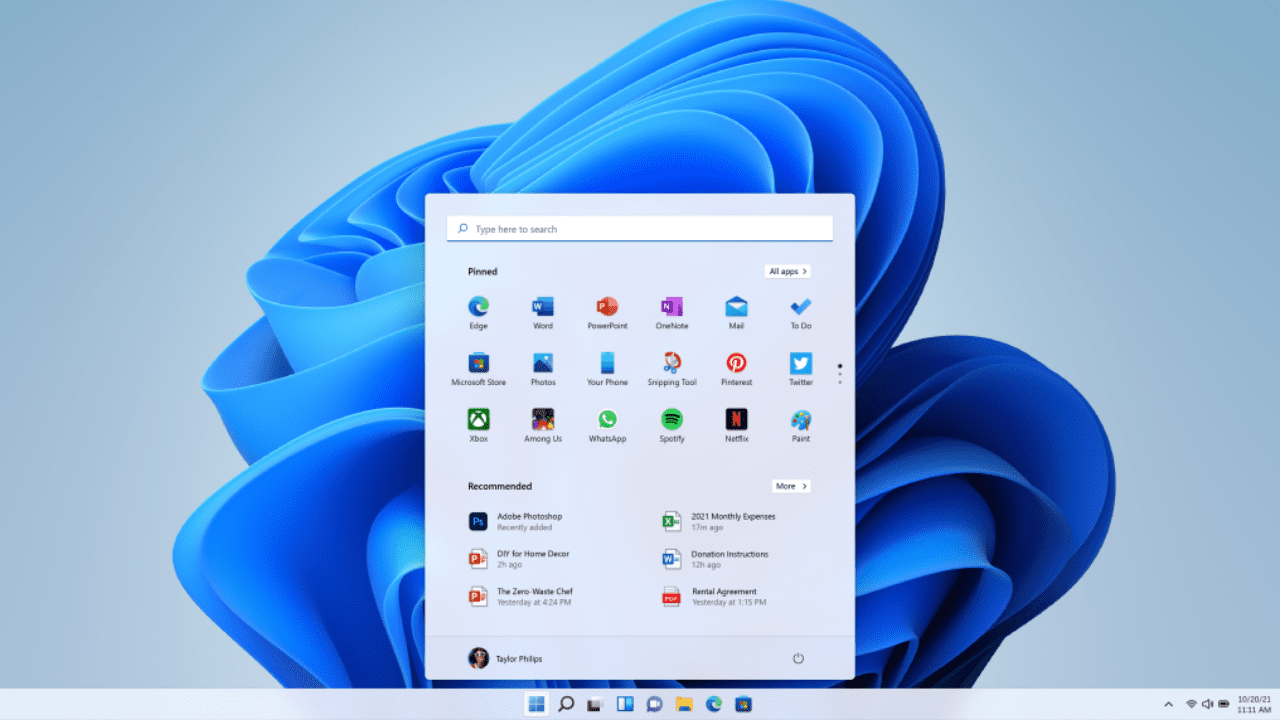
Quality and experiences updates
With this month’s KB5028185 patch for Windows 11 version 22H2, Microsoft is making the “Moment 3” features enabled by default. I previously detailed the main new features in my previous article about the June optional preview release, but here’s what to expect
System tray clock: Users can now choose to display seconds in the system tray clock.
VPN status icon: When connected to a recognized VPN profile, a VPN status icon will appear in the system tray area of the taskbar
2FA codes: This update adds a copy button in notification toasts for copying/pasting 2FA codes more easily
Access Key shortcuts: File Explorer’s context menu adds access key shortcuts to quickly run commands using your keyboard
Multi-app kiosk mode: IT pros can use this lockdown feature to configure distinct types of access and apps to run for different users on one device.
Live kernel memory dump (LKD): In Task Manager, developers can now use an LKD to gather data to troubleshoot an app while the OS continues to work.
Content Adaptive Brightness Control (CABC): This feature must be enabled by the device manufacturer, but it can dim or brighten areas of a laptop or tablet screen based on the content that’s being displayed.
Presence sensor privacy setting: On PCs with compatible presence sensors, the Settings app now lets users choose which apps can access those sensors.
USB4 Settings: The Settings app now offers a dedicated section for USB4 hubs and devices.
Print screen key: Microsoft is changing the behavior of the print screen key, which will now open the Snipping Tool by default. This can be changed in Settings > Accessibility > Keyboard.
Alt+Tab: Microsoft is introducing a limit of 20 most recent tabs when you use Alt+Tab and Snap Assist.
Live Captions: The accessibility feature that launched with Windows 11 version 22H2 is getting support for Chinese, French, German, Italian, Japanese, Portuguese, Spanish, Danish, English, and Korean
Voice Access improvements: Microsoft is adding new commands for selecting and editing text, and the in-app voice access command help page has also been redesigned.
The new Moment 3 features aren’t rolling out to users still running the original version of Windows 11 (21H2). The KB5028182 update is available for those users today, and this patch introduces new features and improvements to Microsoft Defender for Endpoint and other security fixes.
Lastly, the KB5028166 is also available for Windows 10 versions 22H2 and 21H2. The latter reached end of servicing for Home and Pro users last month, but Microsoft is continuing to support the Enterprise and Education editions of the OS.
Windows Update testing and best practices
Organizations looking to deploy this month’s patches should conduct thorough testing before deploying them widely on production systems. That said, applying the patches widely shouldn’t be delayed longer than necessary as hackers start to work out how to weaponize newly reported vulnerabilities.
A best practice is to make sure you have backed up systems before applying updates. Every month, users experience issues with Windows updates that lead to systems not booting, application and hardware compatibility issues, or even data loss in extreme cases.
There are backup tools built into Windows and Windows Server that you can use to restore systems in the event a patch causes a problem. The backup features in Windows can be used to restore an entire system, or files and folders on a granular basis.
If you have any problems with this month’s patches, please let us know in the comments below. Other readers might be able to share their experiences in how to roll back problematic updates or mitigate issues caused by patches that are important to have in place.