Earlier this month, the Azure Sentinel and Microsoft Threat Intelligence Center (MSTIC) teams announced the public availability of ‘Fusion detection for ransomware’. Fusion is designed to automatically correlate security alerts that could be related to ransomware. More precisely, Microsoft said the Fusion machine learning model collates alerts detected in a specific timeframe during defense evasion and execution stages of a ransomware attack.
Fusion machine learning model makes life easier for security analysts using Azure Sentinel
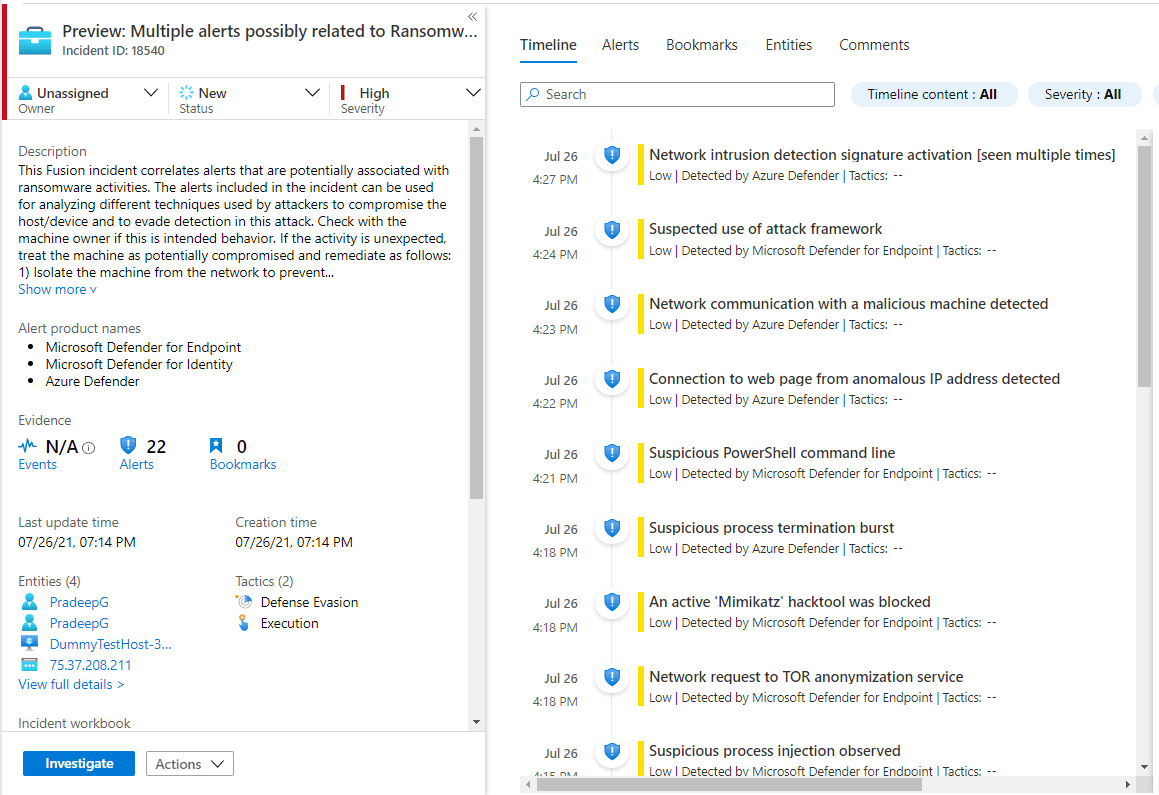
Once collected, the events are surfaced as a high severity incident, called “Multiple alerts possibly related to Ransomware activity detected”, in the Azure Sentinel workspace. Automating the detection and collection of such events helps security analysts quickly identify potential attacks and act to stop them.
Fusion gives analysts a complete picture of the detected activities on a device, and it collects signals from several Microsoft products, and from the network and cloud. Microsoft says that Fusion supports the following data connectors:
- Azure Defender (Azure Security Center)
- Microsoft Defender for Endpoint
- Microsoft Defender for Identity
- Microsoft Cloud App Security
- Azure Sentinel scheduled analytics rules
Ransomware is the number one security threat
According to a report released by PurpleSec, ransomware attacks cost organizations 23 times more in 2020 compared to 2019. And ransomware cost a total of $20 billion in 2020, with downtime caused by ransomware increasing more than 200%.
Prevention is always better than cure, but with the rise of ransomware as a service, the scale and complexity of attacks are increasing. Hackers are resorting to slow and stealth techniques to evade detection.
Fusion reduces Mean Time to Detect and Mean Time to Respond
To combat this trend, Fusion is designed to detect malicious activity at the defense evasion and execution stages of an attack. Fusion helps analytics quickly access the information they need to understand the complete picture and act to stop an attack in its tracks. And most importantly, stop ransomware spreading to multiple devices on a network. Microsoft puts it like this:
The sooner such alerts are raised to security analysts with the details on various attacker activities, the faster the ransomware attacks can be contained and remediated. A detection like this will help analysts by giving the compilation of attacker activity around execution stage helping reduce MTTD (Mean Time to Detect) and MTTR (Mean Time to Respond).
Fusion isn’t completely new. It has already been implemented in Azure Sentinel, Microsoft’s cloud-native Security Information and Event Management (SIEM) product, for some time. Currently there are 35 multistage attack scenarios Fusion-enabled and generally available in Azure Sentinel.
Improving the Fusion machine learning model
If Fusion surfaces a multi-stage event in Azure Sentinel, analysts should ask the device owner if the behavior detected is intentional. If not, the device should be deemed potentially compromised and isolated from the network.
Microsoft would like its clients to provide feedback on Fusion incidents. There’s the option to indicate whether an incident was a true positive, benign positive, or false positive. The more information Microsoft can collect about incidents surfaced by Fusion, the better it can train its machine learning model.
Machine learning data and Customer Managed Keys
Azure Sentinel uses 30 days of historical data to train the ML model. The data is always encrypted as it is sent through the machine learning system. Organizations with Customer Managed Keys (CMK) turned on in an Azure Sentinel workspace should be aware that CMKs are not used to encrypt data sent to machine learning systems. Fusion is turned on by default, but customers using CMKs can turn Fusion off by disabling Multistage Attack Detection in the Azure Sentinel rules configuration.