We started this series with how Windows Firewall started out in Windows XP. This article will cover how Windows Firewall changed between Windows XP and XP SP2. In the other 3 parts of this series, I will show you how the Windows Firewall changed, over time, to be what it is today in Windows 7.
From Internet Connection Firewall to Windows Firewall
Internet Connection Firewall (ICF) that was available as part of Windows XP and Windows XP with Service Pack 1 (SP1) offered a baseline level of security through Stateful Packet Filtering which derives filtering decisions on a packet’s state and the context information of the active session.
This initial firewall service offered as a part of Windows XP was disabled by default due to concerns with backward compatibility with older applications and due to the fact that many end users were not familiar enough to configure their existing applications to work through the firewall.
Because of some high profile worm attacks in 2003 and 2005 against the Windows operating system as evidenced in the Blaster Worm and Sasser Worm events Microsoft totally revamped the Internet Connection Firewall. As part of the release of Service Pack 2 the Windows Security Center was introduced and the Windows Firewall was born.
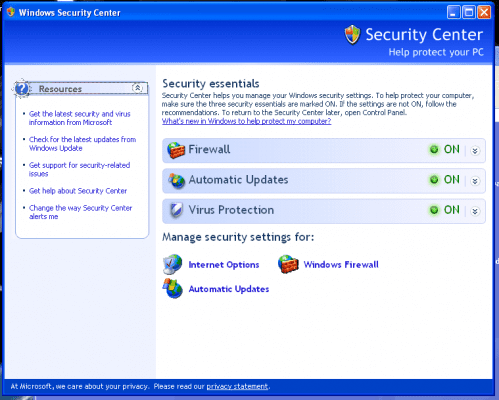
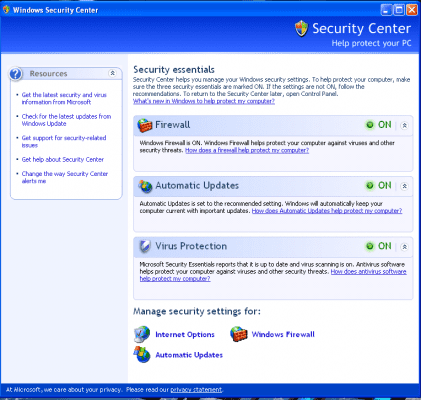
Windows Security Center
The introduction of the Windows Security Center as part of Service Pack 2 was almost as important as the changes to Windows Firewall.
This resource center allow users to have a single place for them to go in order to review the status and the settings for not just their Windows Firewall but also the settings and the status of Automatic Updates and Virus Protection.
Automatic Updates are provided through the operating system as a service but Virus Protection was not but third part virus scanners would be offered a minimal status view within the Security Center. An end user could see whether the virus protection was turned on and whether or not the definitions were up to date provided the third part vendor wrote in the reporting code to give this information out to the Security Center. (If they didn’t you could turn the view off by electing to monitor the virus protect separately).
The Windows Firewall section allowed you to monitor Windows Firewall or even third party firewalls if they were chosen for use and Windows Firewall was disabled.
Many security providers offered full security suites that included their own security center to monitor their virus protection, firewall and spam filter settings for e-mail clients.
If the choice was to just use their firewall and if there were hooks written to leverage the Microsoft Security Center then their status could be shown there as opposed to having another service installed and running to do the monitoring.
Windows Firewall – The Details
The release of the Windows Firewall that was included with Service Pack 2 was a major upgrade to the service as well as a mentality shift for Microsoft.
The change is introduced right at the completion point of the Service Pack 2 installation where the screen informs you that the Firewall is enabled and asks you to keep the recommended settings before continuing.
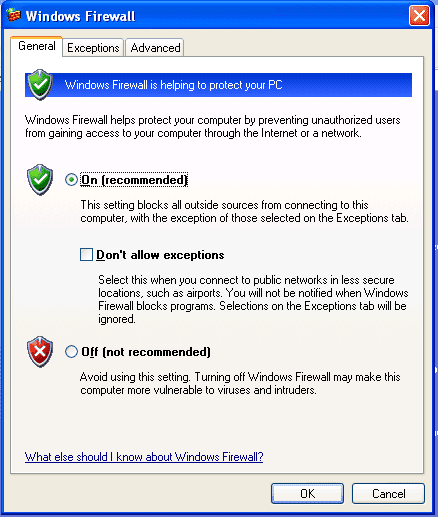
That setting is shown when you view the properties page for Windows Firewall.
Some of the additional enhancements to this release of Windows Firewall is that it is enabled for all network connections by default. Some additional changes were made to available Group Policy parameters so that administrators could configure Windows Firewall enterprise wide for all their client systems.
There are a number of options that you can choose manually on the different properties pages.
On the General Tab you can set the Windows Firewall to ON or OFF in totality for all connections. There is one other setting that could be made which is the “Don’t allow exceptions” check box.
When you enable this setting you’ll be negating any rule exceptions that you might have made on the Exceptions tab. Generally this setting might be something you enable when you are on a public or other untrusted network.
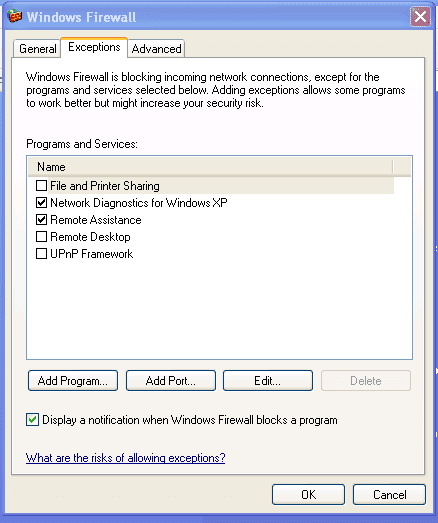
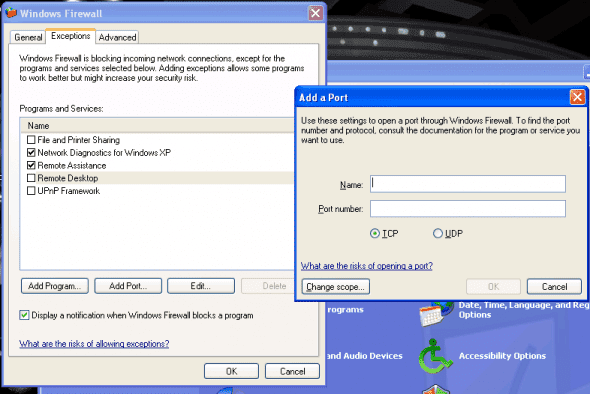
On the Exceptions tab you can see the programs and services that are already listed as being allowed through the Windows Firewall in order to successfully communicate and function correctly.
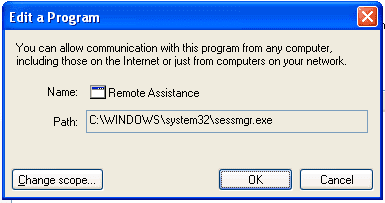
If you need to make any adjustments to an existing application you could highlight it from the list and choose EDIT which would bring up the Edit a Program dialog box.
From here you can change the path of the executable if needed or if you needed to make additional changes you can hit the Change Scope button.
Once you are on the Change Scope page you have the ability to change the scope of the exception for the executable. You can set the unblock exception for Any computer (including those on the Internet) – this is the default setting – or you can choose the other available options which include “My network (subnet) only or “Custom list” which allows you to type in individual IP addresses or a range of addresses.
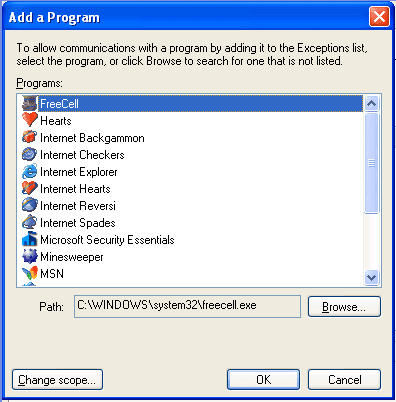
Additionally available to configure on the Exceptions tab are additional programs that are not present in the list. This function might need to be used for legacy applications that need to communicate outbound but do not configure themselves dynamically during installation.
If you need to do this you would hit the Add Program button and choose one of the programs in the Add a Program pane or by browsing for the path of the executable directly.
You also have the ability to change the scope of the newly added program by selecting the Change Scope button which allows you to change the scope of the exception for the newly added program or executable.
As outlined earlier with exceptions that were already present, you can set the unblock exception for Any computer (including those on the Internet) – this is the default setting – or you can choose the other available options which include “My network (subnet) only or “Custom list” which allows you to type in individual IP addresses or a range of addresses.
If you need to configure additional ports to have an exception you would choose the Add Port button which would allow you to assign a Name and the port number you need and whether is uses the Transmission Control Protocol (TCP) or User Datagram Protocol (UDP).
In order to make an exception for port 25 for both TCP and UDP you would need to use the Add a Port option twice as each entry for TCP or UDP is “either or” and not for both. In order to get both you need a second individual entry for the other setting.
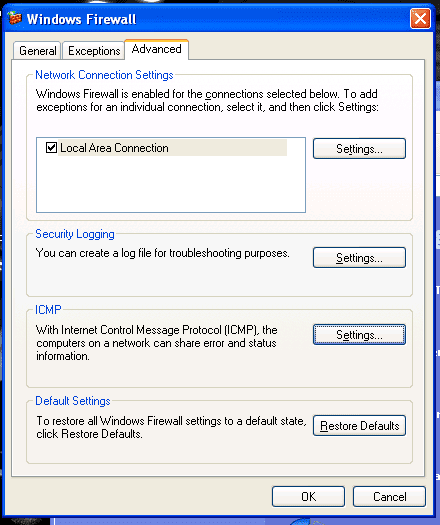
If you need to adjust additional settings you would go to the Advanced Tab.
On this tab you have the ability to configure settings for each of the connections that are listed in the Network Connections Settings section. If you have just one connection you will see only one to configure and it will be selected by the check box to the left by default but if there are multiple settings you can configure each individually.
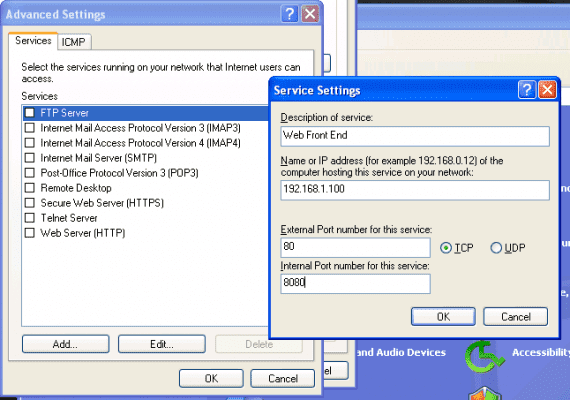
By choosing the Settings button you are able to configure the Advanced Settings for the services on the local system that may be running that you want to allow user access to as well as adding additional ones to the system.
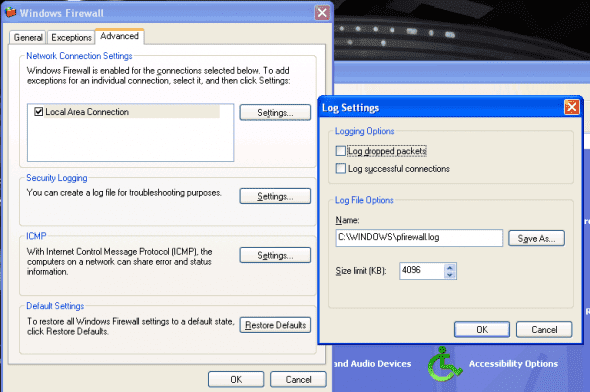
From the Advanced Tab you can go to the Security Logging section to configure the settings for log file creation. The default settings are shown below.
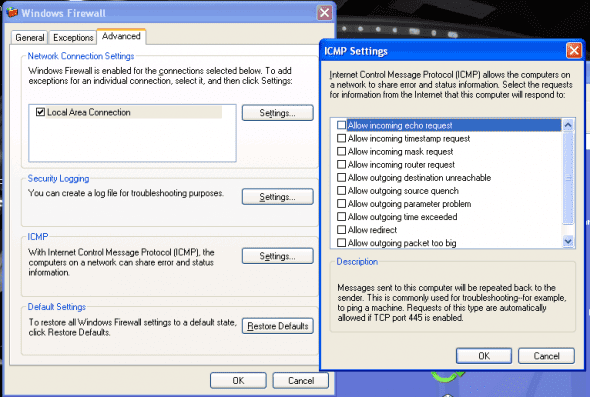
If you need to configure the Internet Control Message Protocol (ICMP) on the Windows Firewall so that you can allow for the ability to troubleshoot network related issues with the client this can be done by selecting the Settings button from the ICMP section of the Advanced tab.
In this tutorial we reviewed how to go about a few of the changes from the original release of the Internet Connection Firewall to the updated version of Windows Firewall in SP2. We also did a quick review of the Windows Security Center.
Continue reading part two of this series at: Evolution of Windows Firewall – Part Three – Windows Vista.