Latest Windows Server Updates Trigger Hyper-V VM Boot Problems

Key Takeaways:
- Microsoft has acknowledged a new issue affecting Windows Server 2022 and Windows Server 2019.
- The bug is caused by the October 2023 Patch Tuesday updates, resulting in virtual machines (VMs) running on Hyper-V hosts failing to start.
- Microsoft is actively investigating the problem, and affected users are advised to uninstall the problematic October 2023 Patch Tuesday updates.
Microsoft has acknowledged a new issue that is currently affecting Windows Server 2022 and Windows Server 2019. Found in the latest Patch Tuesday updates released on October 10, this new bug breaks virtual machines (VMs) running on Hyper-V hosts.
Specifically, Microsoft says that users might notice that the virtual machines fail to start or are not found on affected systems. The problem can occur after installing the KB5031361 and KB5031364 updates on Windows Server 2019 and Windows Server 2022 machines.
“After installing this update on guest virtual machines (VMs) running Windows Server 2022 on some versions of VMware ESXi, Windows Server 2022 might not start up. Only Windows Server 2022 VMs with Secure Boot enabled are affected by this issue. Affected versions of VMware ESXi are versions vSphere ESXi 7.0.x and below,” Microsoft explained.
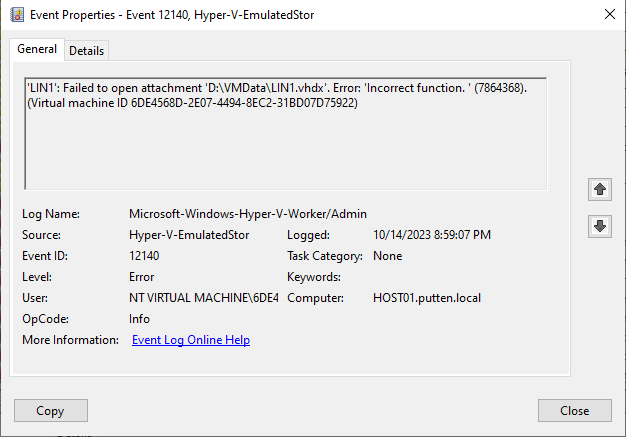
Users who attempt to start a virtual machine on a Hyper-V system will see the following error messages in the event viewer:
- Failed to Power on with ‘Incorrect function’ error.
- Failed to open attachment ‘vhdx_path’. Error: ‘Incorrect function.’
- Failed to start virtual machine tools. Error: ‘TOOLS’ failed to start.
Temporary workaround to fix issues with Hyper-V VMs
Microsoft and VMware are currently investigating the problem and will provide additional information as soon as it’s available. If you happen to run into this issue, you will need to wait for an update that fixes the problem. In the meantime, it’s recommended to uninstall the buggy updates to address the Hyper-V boot issues. To do this, open the command prompt and execute the following commands:
- wusa /uninstall /kb:5031364
- wusa /uninstall /kb:5031361
This is among the most recent issues affecting the October 2023 Patch Tuesday updates. Just earlier this week, Microsoft provided a solution for a problem that was blocking users from installing the KB5031356 update on Windows 10 PCs. The company has introduced a Known Issue Rollback (KIR) policy to address this problem with enterprise-managed devices.
Windows administrators can find this special Group Policy in Computer Configuration -> Administrative Templates, and you can check out this support page to learn more about the deployment process.



