Using Startup Scripts to Manage Local Active Directory Groups
Following the first three installments of our article series on managing local Active Directory group, we’ll end the series with this fourth and final post by focusing on how you can use startup scripts to manage membership of local groups.
Managing Local Active Directory Groups Article Series
- Part 1: Manage Local Active Directory Groups using Group Policy Restricted Groups
- Part 2: Using “This group is a member of” controls to manage local AD groups
- Part 3: Manage Local Active Directory Groups using Group Policy Preferences
- Part 4: Using Startup Scripts to Manage local Active Directory groups
You can write these scripts as command-shell batch scripts ending with the .bat or .cmd extension, or as scripts that use the Windows Script Host (WSH) written in a scripting language, such as VBScript.
In this article, we’ll use an example found on the Petri forums that’s written by one of our moderators, Rems.
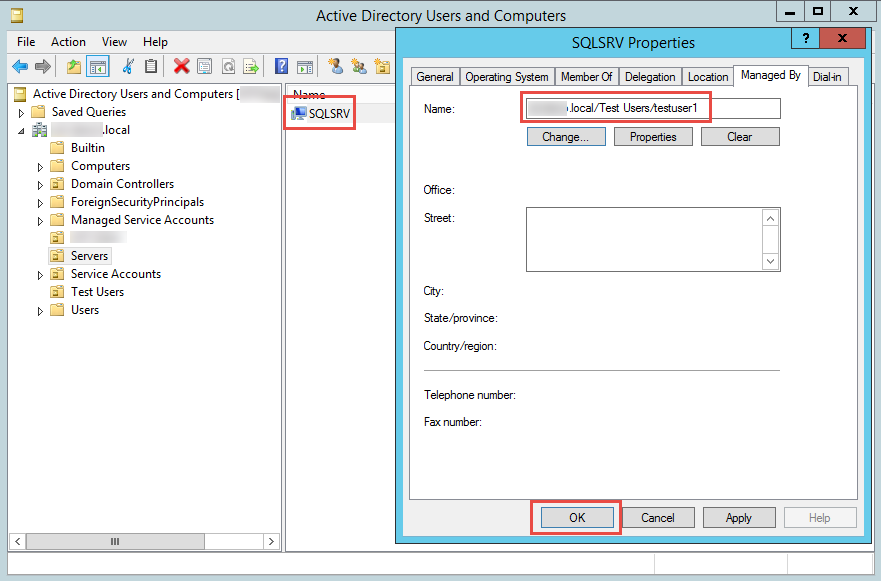
When there is need to add a particular user to the local administrators group on a client computer, one can use a combination of the computer name found in the computer object in Active Directory, plus the ManagedBy attribute of the computer object, which should be manually changed to match the user account that currently uses that computer.
This sample computer startup script determines the distinguished name of the client and uses it to bind to the computer object in AD. It then reads the ManagedBy attribute of the computer object and adds the user to the local administrators group. In addition, the previously added domain user is deleted from the local administrators group.
Note: Of course you can use it to add the user to any other group, just modify the script.
Warning: Use caution when working with scripts, and always test in a lab environment before applying in you production environment.
Sample script:
With CreateObject( "WinNTSystemInfo" )
strComputer = .ComputerName
strDomain = .DomainName
End With
' Bind to the local Administrators group
Set objAdmGroup = GetObject("WinNT://" & _
strComputer & "/Administrators,group")
' Remove all current *domain\objects* of the group.... !
For Each objMember In objAdmGroup.Members
strMember = objMember.AdsPath
IsDomainAcc = instr(1, _
strMember, strDomain & "/" & strComputer & "/",1)=0
If IsDomainAcc = true Then
IsDomAdmins = instr(1, _
strMember, strDomain & "/domain admins",1)
' And..
If IsDomAdmins = false Then objAdmGroup.Remove(strMember)
End If
Next
On Error Resume Next
' Set objRootDSE = GetObject("LDAP://" & strComputer & "/RootDSE")
' Bind to the computer object to get the manager.
With CreateObject("ADSystemInfo")
Set objComputer = GetObject("LDAP://" & .ComputerName)
strManagerDN = objComputer.managedBy
End With
' Bind to 'manager' (<span style="color: #000000;" data-mce-style="color: #000000;">user</span>-)object
Set objManager = GetObject("LDAP://" & strManagerDN)
strManager = replace(objManager.SAMAccountName,"$","")
strManager = "WinNT://" & strDomain & "/" & strManager
' Make it a member of the group
If Err.Number = 0 Then
If objAdmGroup.IsMember(strManager) = false _
Then objAdmGroup.Add(strManager)
End If
' On Error Goto 0
Save this as a text file with a .VBS extension and configure it as a startup script on the GPO that affects the computer objects on which you want to manage the group membership.
To assign a computer startup script, follow these steps:
1. Copy the script.
2. In the GPMC, edit the GPO that is linked to the organization unit (OU) that contains the computer objects you want to work with.
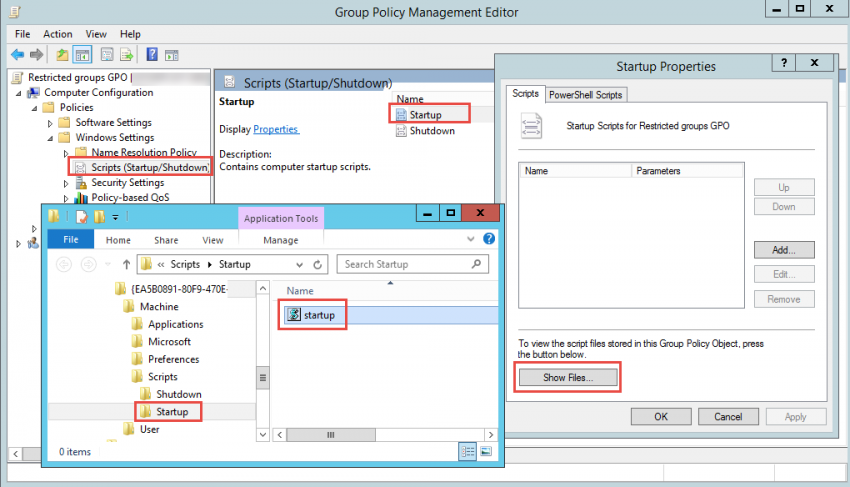
3. Expand “Computer Configuration” > “Windows Settings” > “Scripts”.
4. Right-click Startup and then select Properties.
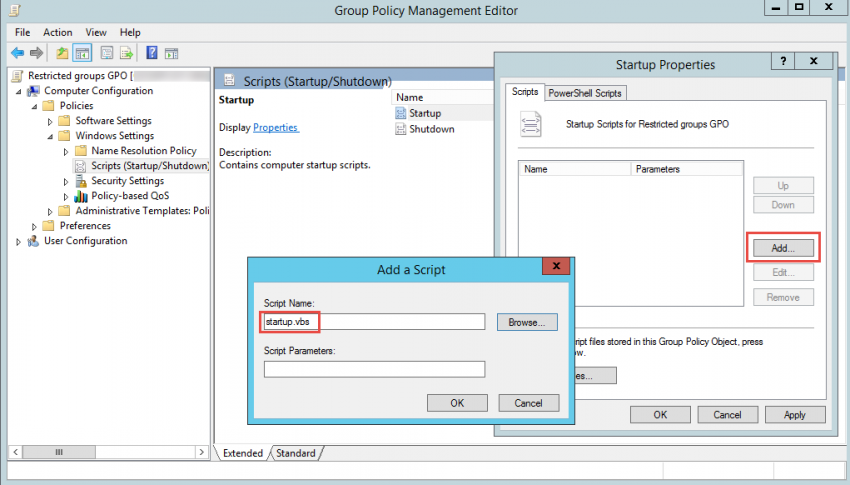
5. Click “Show Files”. Paste the copied script in the folder that opens.
6. Click “Add”. This opens the “Add A Script” window. In the Script Name field, browse to the script you copied to the Machine\Scripts\Startup folder for the related policy. If you have any, in the “Script Parameters” field, enter any command-line arguments to pass to the command-line script.
Note that scripts are executed in the order in which they’re listed, but you can use the up and down buttons as necessary to change the scripts’ order.
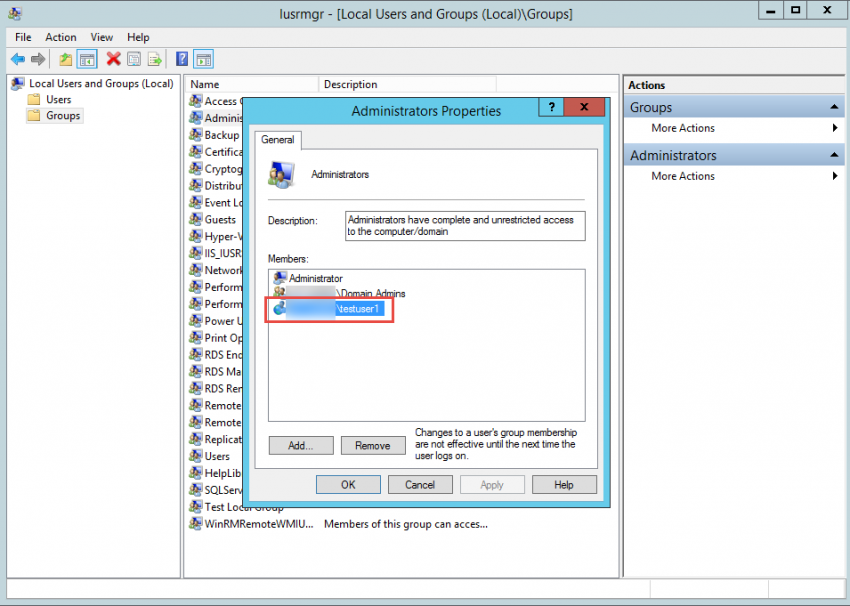
7. Close the GPO editor and reboot the target computer. Look at the Administrators group, and you should find our sample user “testuser1”.
Do you have additional examples of such scripts? Send them over, and I will add them to this page.