Promote a Member Server to Domain Controller in Windows Server 2012
Configuring Active Directory on Windows Server 2012 is a process worthy of patience and attention to detail. It involves installing the Active Directory Domain Services role, defining a new AD forest, creating the first (or root) domain in the forest, configuring DNS, and promoting a member server to a domain controller. Whew, that seems like a bunch of work!
Never fear, Petri is here! A previous Petri post details how to get the Active Directory Domain Services role installed and running on a Windows Server 2012 machine. This article will walk you through the remainder of the process.
Installing AD on Windows Server 2012 and Adding a Forest
Before going any further, it’s important to verify that the member server to be promoted has the Active Directory Domain Services role installed. It also should have a static IP configured. A dynamically configured IP on a domain controller can produce incredibly unpredictable results.
- Login to the server where the Active Directory Domain Services role has been installed using an account that’s a member of the local administrator’s group.
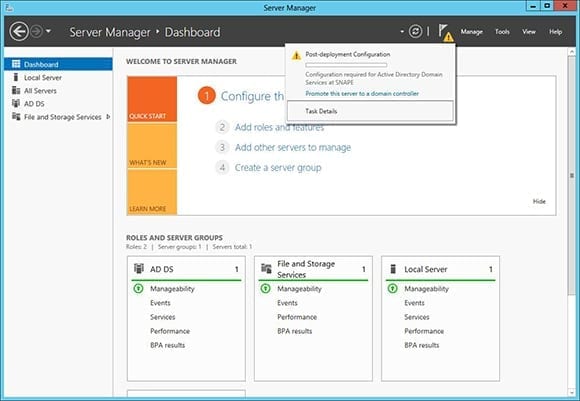
- Open Server Manager.
- Click the Notifications icon. It looks like a flag and is found next to the Manage menu.
- Click Promote this server to a domain controller.
- This will fire up the Active Directory Domain Services Configuration Wizard.
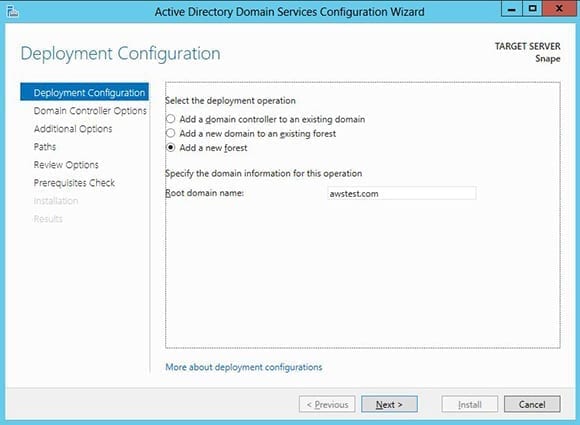
- Select the radio button to Add a new forest.
- Enter the name for the new root domain. Remember, this will also become the name of the forest. For this example, I’ll use awstest.com.
- Click Next.
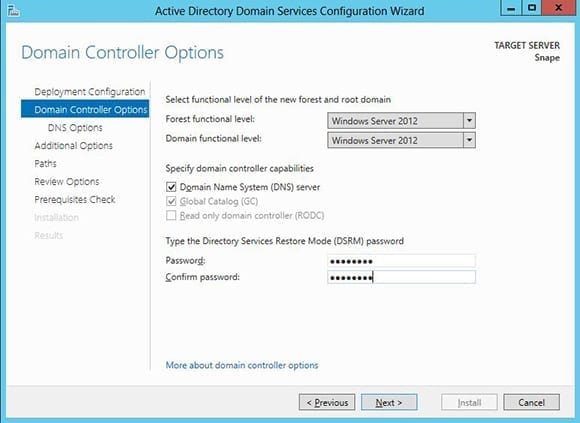
- Leave the defaults selected for the Domain Controller Options. Enter a Directory Services Restore Mode password, which will be used for disaster recovery operations. This password does need to confirm to certain complexity requirements, but the wizard will warn you if they aren’t met.
- Click Next.
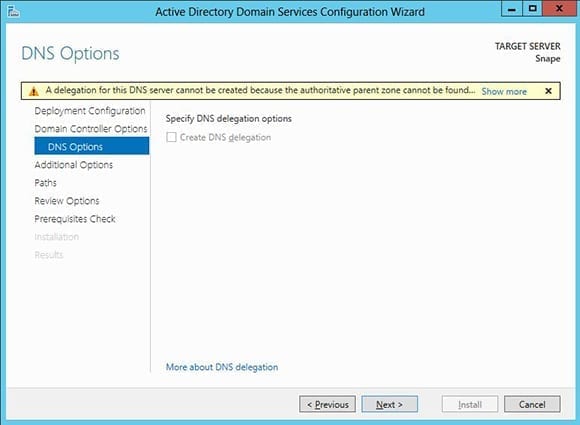
- Since a DNS Server is being configured as part of our efforts, you’ll be warned that a delegation for this DNS server cannot be created. This can be safely ignored.
- Click Next.
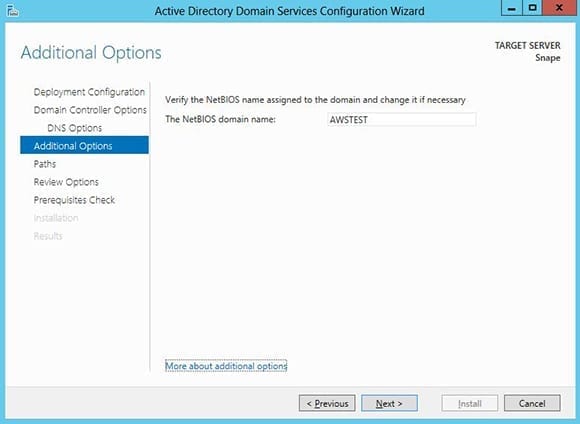
- The wizard will assign a NetBIOS domain name based on the domain name chosen earlier. I suggest leaving this and clicking Next.
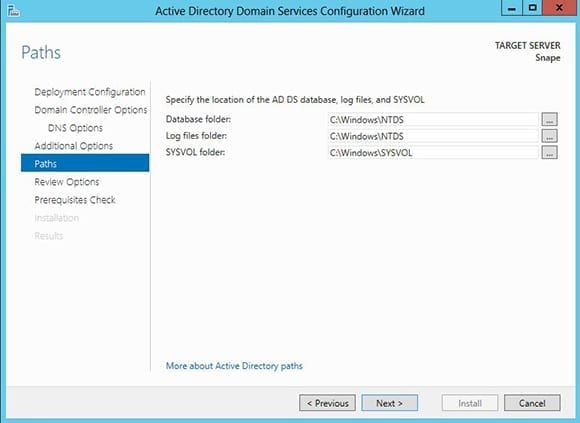
- Confirm the AD database locations displayed, then click Next.
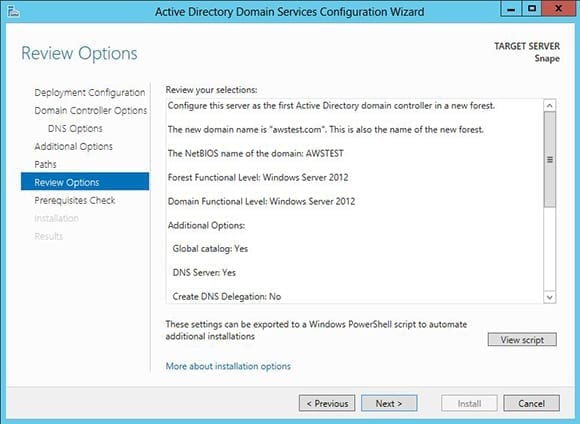
- The Review Options screen gives a final chance to make sure everything has been selected that needs to be selected.
- Click Next.
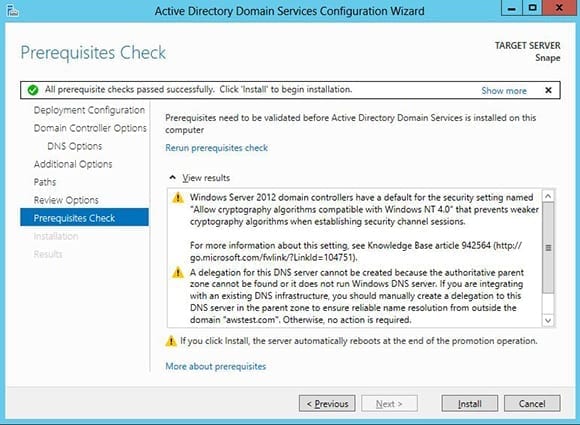
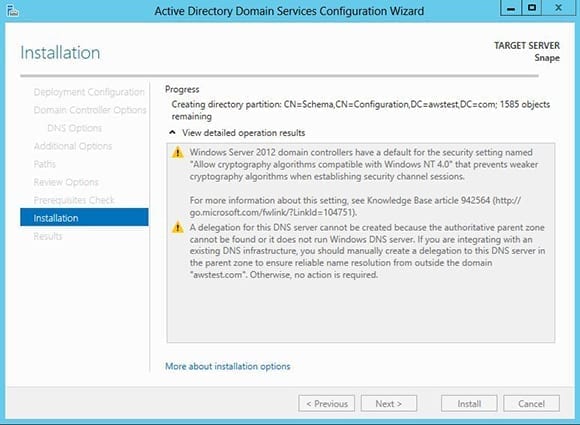
Prerequisites Check
One of the great features of Windows Server 2012’s Active Directory Domain Services Configuration Wizard is that before starting installation it will perform a prerequisites check. This does a good job of making sure nothing is missing that would tank the install. There are a couple warnings you’ll almost always be presented with. The first notifies you that Windows Server 2012 has defaults for certain security settings that can affect very old OSes on the network such as Windows NT 4.0. The second appears when a DNS Server is going to be added by the wizard. It’s a repeat of the message earlier that a DNS Server delegation can’t be created. Both of these errors are safe to ignore in most cases.
- Click Install.
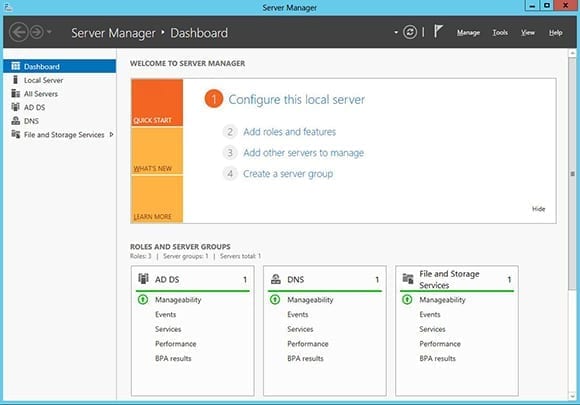
If you selected the option to allow automatic restarts don’t be alarmed when the computer reboots at will. Sit back, relax, and watch the magic happen. When the computer comes back up, logon with either the local administrator account or the new domain administrator account. Either way, you’ll notice new options in Server Manager for AD DS and DNS.
Setting Domain Controllers Using PowerShell
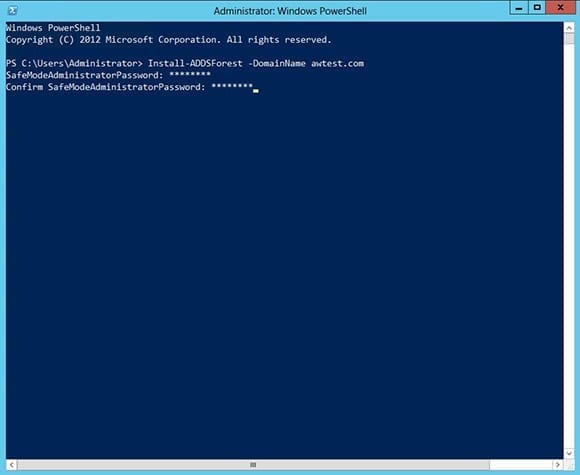
Now for a really neat trick. How would you like to do all of the above with a single PowerShell one-liner? Here’s how to do it.
- Logon to the server as an administrator.
- Open an elevated PowerShell prompt by right-clicking the PowerShell icon and selecting Run as Administrator.
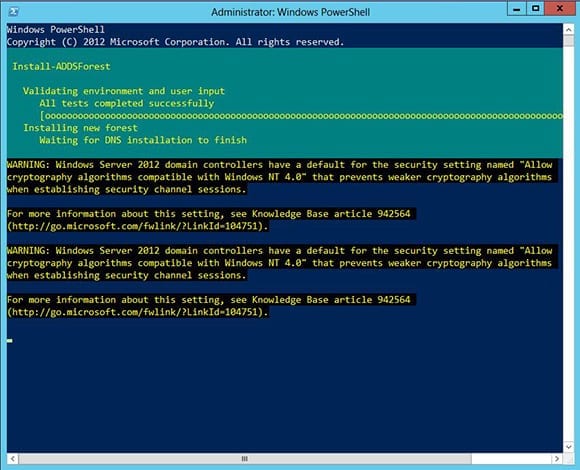
- Type Install-ADDSForest -DomainName awtest.com and hit Enter. Of course, replace awstest.com with your domain name.
- The cmdlet will prompt for a SafeModeAdministratorPassword. This is the Directory Services Restore Mode Password I mentioned earlier. Type in the password you’d like to set, then press Enter. You’ll need to confirm the password by entering it one more time.
- Press A to select Yes to All when prompted to confirm everything. The system will spring into action.
There’s no more to it than that! This cmdlet does everything including adding the DNS Server role if necessary. How’s that for efficient?
Since this is the first and only domain controller in existence for the new AD forest and domain, it will perform a number of additional functions. It will act as a Global Catalog (GC), containing an entire replica of the forest. This domain controller will also hold all five FSMO roles. After promoting additional domain controllers it’s possible to move some or all of these added responsibilities. This allows for better load balancing and redundancy. At minimum, I suggest two DCs in even the most basic AD infrastructure.
You can smile with the satisfaction of a job well done! You’ve installed Active Directory on Windows Server 2012, created a new AD forest, a new domain, and even configured a DNS server. Watch for a coming Petri article where I’ll walk you through adding a “headless” domain controller to the domain using Windows Server 2012 Server Core. Windows Server 2012 and Active Directory are truly made for one another!