Big Brother Watches Your Email with Office 365 Supervision Policies
The Need for Supervised Email
None of us likes the idea that someone might be watching what we send in mail, but in some highly regulated industries, review of communications is a necessary evil. For example, FINRA, the U.S. Financial Industry Regulatory Authority, enforces rules governing the activities of brokers and dealers to ensure market transparency and fairness.
In the past, on-premises organizations had to write and install special software to capture and examine messages sent between employees. The software was inserted in the transport pipeline to capture copies of messages and route them for review to ensure that no problems exist.
Supervision Policies are Microsoft’s second version of policies to create a framework for email review and reached general availability in May 2017. These policies are part of Office 365 Advanced Data Governance, which means that all accounts coming under the scope of a supervision policy need to have an Office 365 E5 license or the Advance Compliance SKU.
Components of a Supervision Policy
A supervision policy includes the following components:
- Reviewees: The people (individuals or groups) whose communications need to be reviewed. You can use email distribution groups to define the reviewees for a policy.
- Conditions: Queries and conditions to find items for review. Like content searches, queries are in KQL syntax. However, supervision policies only support relatively simple queries when compared to content searches. Conditions include size limits and types of attachments.
- Sample size: The percentage of messages satisfying the policy conditions captured for review. You can capture 100% of messages or a smaller amount.
- Reviewers: The people who will access the items captured for review to decide whether the content of those items are compliant. The reviewers can access review items with OWA or Outlook 2016 and mark the status of an item as compliant or not.
- Reports: A set of reports about supervision policy activity in the Reports section of the Security and Compliance Center.
You can deploy multiple supervision policies within a tenant, each of which monitors the communications for a distinct group of reviewees. Supervision policies only cater for Exchange messaging today. Communications through Yammer or Microsoft Teams are not subject to review.
Creating a Supervision Policy
You manage supervision policies through the Data Governance section of the Security and Compliance Center. Only users who hold the Supervisory Review permission can work with supervision policies.
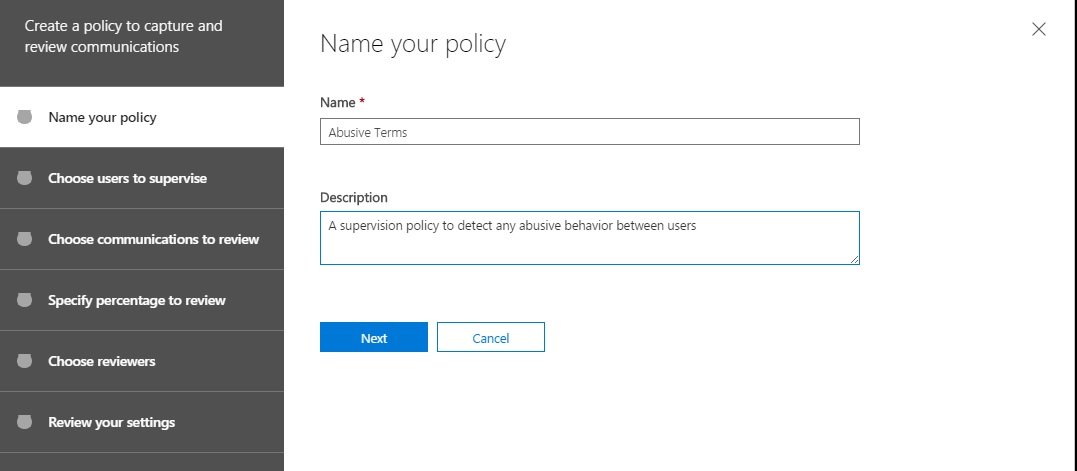
Supervision policies are created and edited using the wizard-style approach implemented by Microsoft for all policies managed through the Security and Compliance Center. The first part of the process is to name the policy (purely for administrative purposes as end users have no idea that such policies exist). You can also provide an optional description of what the policy is intended to do (Figure 1).
Reviewees
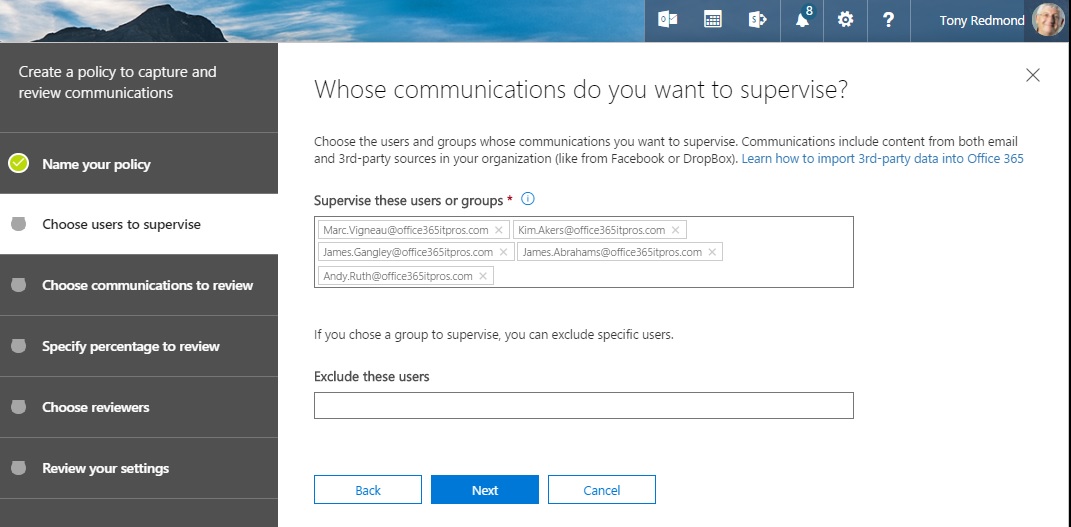
Next, you need to define whose email the policy will monitor (Figure 2). You can input individual user names or you can use email distribution groups. If you use groups, Office 365 expands the membership into individual accounts and adds them to the policy when it is saved. This is a one-time operation and future additions or deletions to the group membership are not carried through to the policy.
Conditions
The heart of the policy are the words or phrases that trigger capture of copies of messages. As you can see from Figure 3, our policy will monitor for some nasty words that might pass in anger between the reviewees. After all, we want our tenant to be a nice place to work.
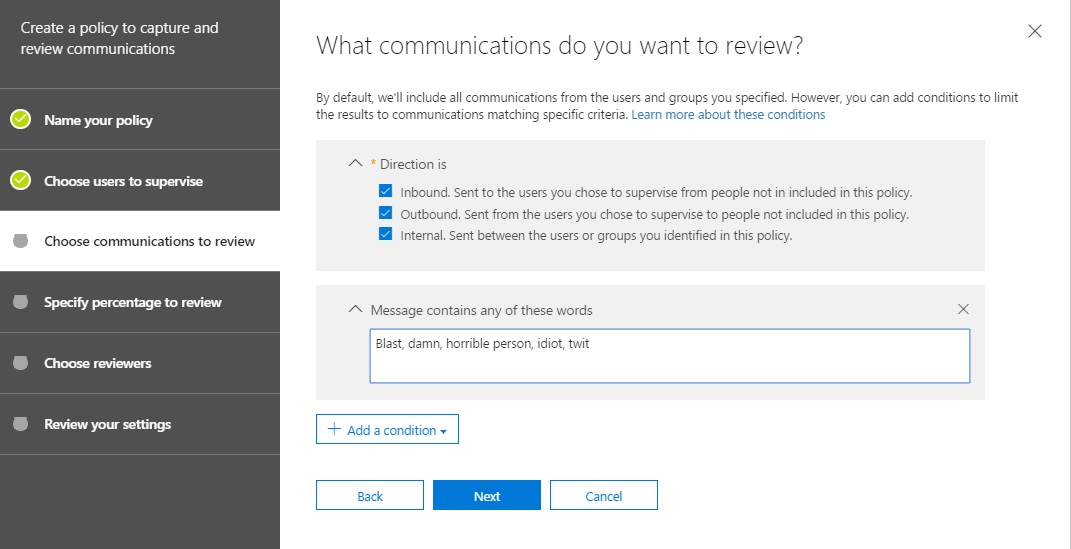
You can capture copies of every message passing to, from, and between the reviewees by selecting the direction of the traffic to monitor and not adding a condition. Apart from words that appear in the message, other conditions include the presence of a certain kind of attachment, words appearing in an attachment, or overall message size.
Review Percentage
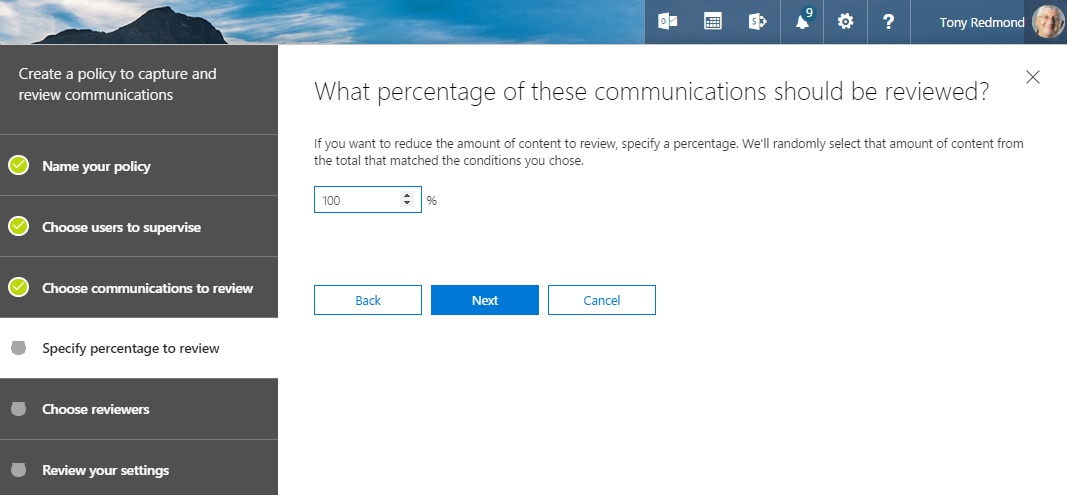
Now we decide on the percentage of traffic that meet our monitoring criteria we want to review. Typically, you might start by reviewing 100% of traffic (Figure 4) to ensure that the policy works as expected and then reduce the percentage to a more manageable level.
Picking Reviewers
The last part of creating a supervision policy is to define who will do the work of reviewing the captured items. Depending on the expected workload, this might be one or more people. For now, we’ll do with just one (Figure 5).
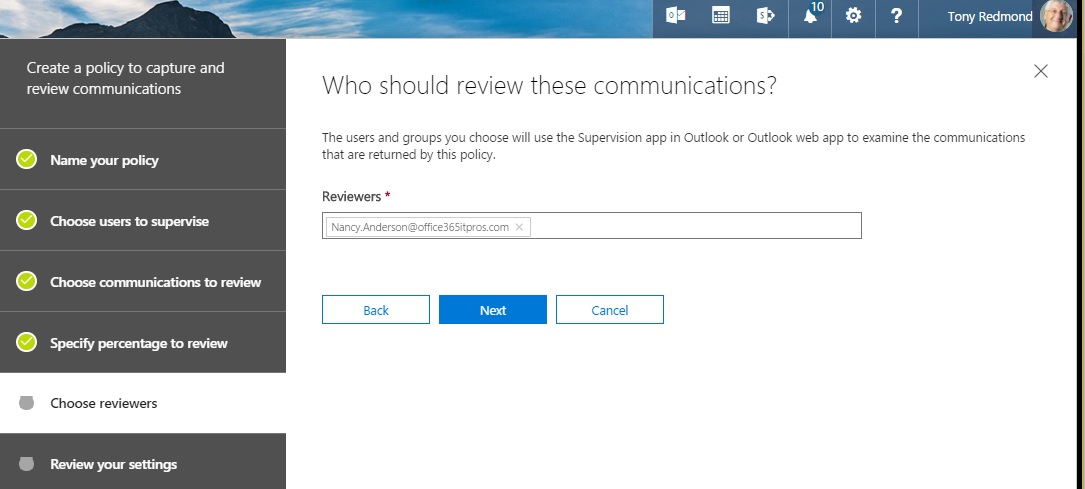
Clicking Next gives us an opportunity to review the policy. If all looks good, click Finish to tell Office 365 to provision the policy. During this process, the add-in to allow the review of items is inserted into OWA so that the reviewer can access items captured for review the next time they sign in. You have to follow a different process to configure the add-in for Outlook desktop.
Processing Review Items
A few minutes after saving the policy, it will be effective in the transport pipeline and messages that meet the policy criteria are captured for review. When reviewers open OWA, they see a new resource called “Supervision – Policy Name” (Figure 6) that looks like a shared folder. In effect, this is a link to the Inbox folder of the special review mailbox where Exchange stores captured items for review.
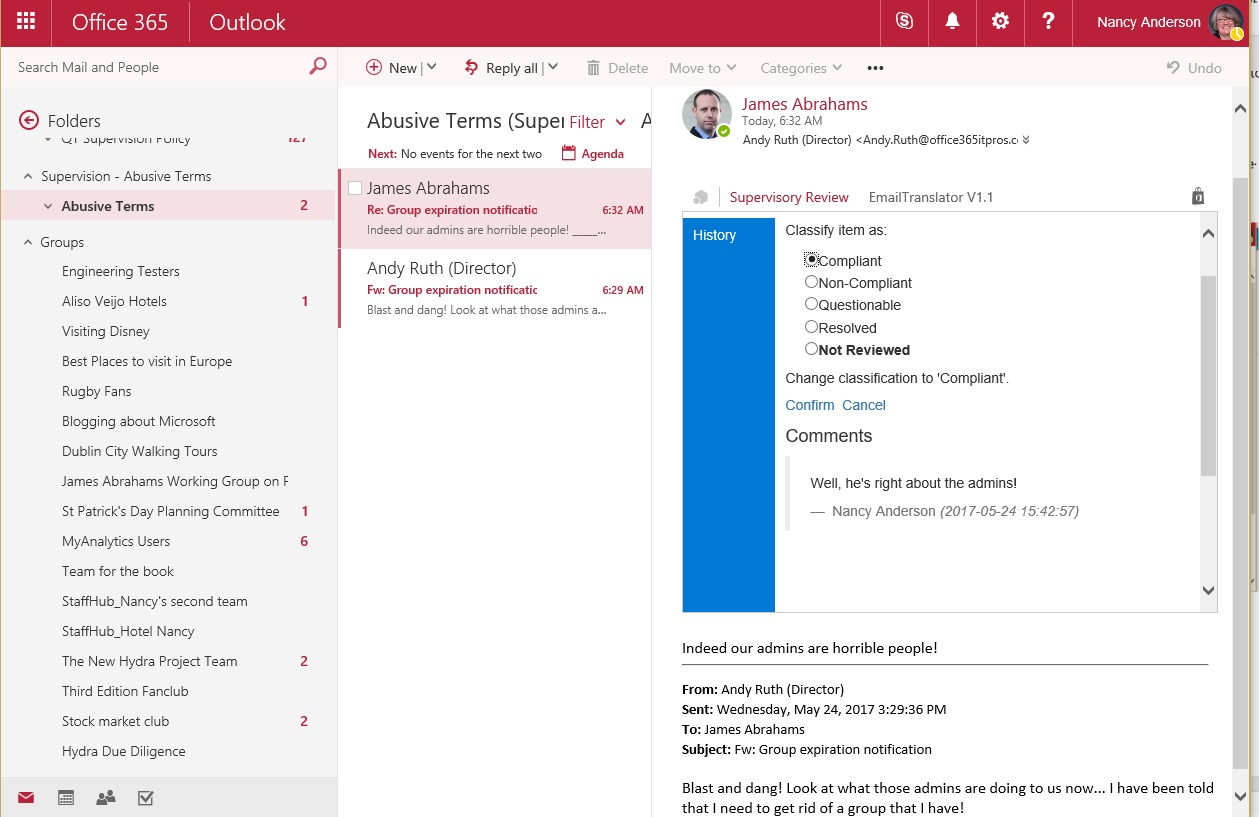
To resolve an item, the reviewer clicks the Supervisory Review add-in within a message. OWA then presents a form to gather information about the compliance status of the item and any comments that the reviewer wants to make. You cannot change the classifications as they are hard-coded. Click Confirm to complete the classification of the item.
Office 365 gathers statistics about the disposition of review items into each of the classifications and presents this data in the Reports dashboard of the Security and Compliance Center. The data are normally two or three days behind live processing because of the need to gather, aggregrate, and process the data for Office 365 Reports.
A Necessary Evil
No one likes the thought that someone else might be reading their email (apart from known recipients, of course). Today’s world is full of regulations and if you work in an industry that is governed by regulations, you might find the need exists for someone to throw a watchful eye over email traffic, just to make sure that everyone stays on the right side of the line. Office 365 Supervision Policies provide an automated way to monitor email traffic. I’m sure that they will be popular in some industries.
Follow Tony on Twitter @12Knocksinna.
Want to know more about how to manage Office 365? Find what you need to know in “Office 365 for IT Pros”, the most comprehensive eBook covering all aspects of Office 365. Available in PDF and EPUB formats (suitable for iBooks) or for Amazon Kindle.




