
Microsoft has announced the release of version 14.0 of Sysmon. The latest release brings a new feature that lets IT admins prevent processes from creating harmful executable files in certain locations.
System Monitor (Sysmon) is a free tool that allows administrators to monitor systems for malicious activities to detect advanced threats. It provides details about several system events like possess creations, network connections, registry activities, and file changes. IT admins can view these activities in the Windows Event Log.
The latest version of Sysmon introduces a new event type called “FileBlockExecutable.” Once enabled, the feature considers the name, path, hash, and malicious program to block the creation of executable files such as DLL, EXE, and SYS.
“Sysmon now impedes executables, based on the file header from being written to the filesystem according to the filtering criteria. This can be a very powerful feature into blocking certain programs writing malicious files to disk,” the Sysinternals team explained.
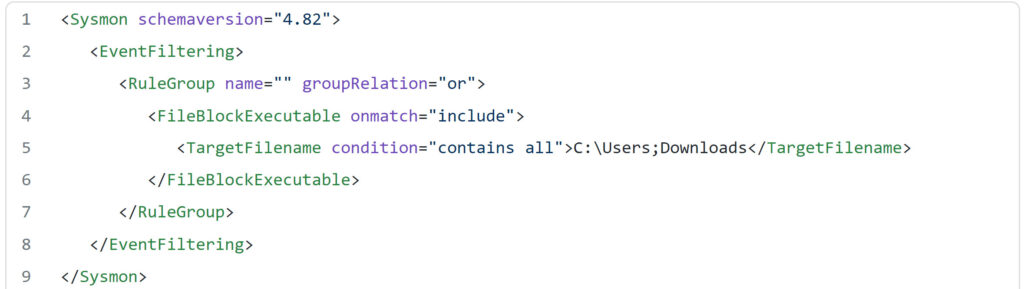
Here’s an example that illustrates how this feature works to block malicious downloads on affected systems:
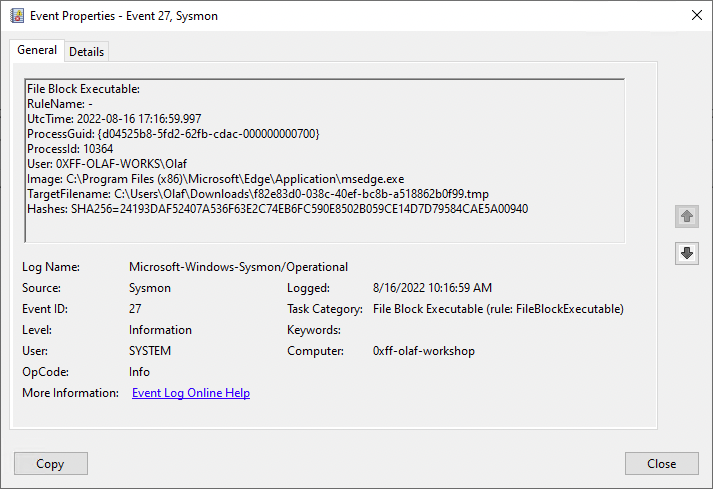
Additionally, Sysmon will add an ‘Event 27, Sysmon’ entry in Event Viewer. Users will see valuable information in the event logs, including process id, user name, name of the malicious program, as well as details about the blocked file and its hash.
Microsoft Sysmon’s new feature already bypassed
The new security feature is a welcome addition that can help organizations to protect their enterprise networks from malicious payloads. However, security researcher Adam Chester has already bypassed the FileBlockExecutable directive.
To get started, IT admins can use the Sysmon configuration files published by SwiftOnSecurity and Florian Roth on GitHub to block malware attacks. If you’re interested, we invite you to check out this support document to learn more about Sysmon.



