Microsoft to Add SMB NTLM Blocking Support to Windows 11

Key takeaways:
- Windows 11 Preview Build 25951 bolsters network security by allowing administrators to block NTLM for outbound connections, thwarting potential attacks.
- The update also simplifies SMB dialect management by allowing administrators to prevent the use of older and potentially vulnerable SMB protocols within their organization.
- IT administrators can configure these security features through various methods like Group Policy, PowerShell, and NET USE.
Microsoft has announced the release of a new Windows 11 Preview Build 25951 to the Canary Channel. This release comes with notable improvements to the Server Message Block (SMB) protocol, SMB NTLM Blocking, and SMB Dialect Management, offering practical enhancements in the realm of network security.
The first major change that Microsoft highlighted today is the ability to use the SMB client to block NTLM for remote outbound connections. The legacy behavior allowed Windows SPNEGO to negotiate Kerberos, NTLM, and other mechanisms with destination servers. This release now allows IT admins to block outbound NTLM over SMB.
According to Microsoft, the new security feature offers additional protection against password cracking, pass-the-password, and brute-force attacks. It eliminates the need to shut down NTLM usage in Windows completely.
“With this new option, an administrator can intentionally block Windows from offering NTLM via SMB. An attacker who tricks a user or application into sending NTLM challenge responses to a malicious server will no longer receive any NTLM data and cannot brute force, crack, or pass a password, as they will never be sent over the network,” the Windows Insider team explained.
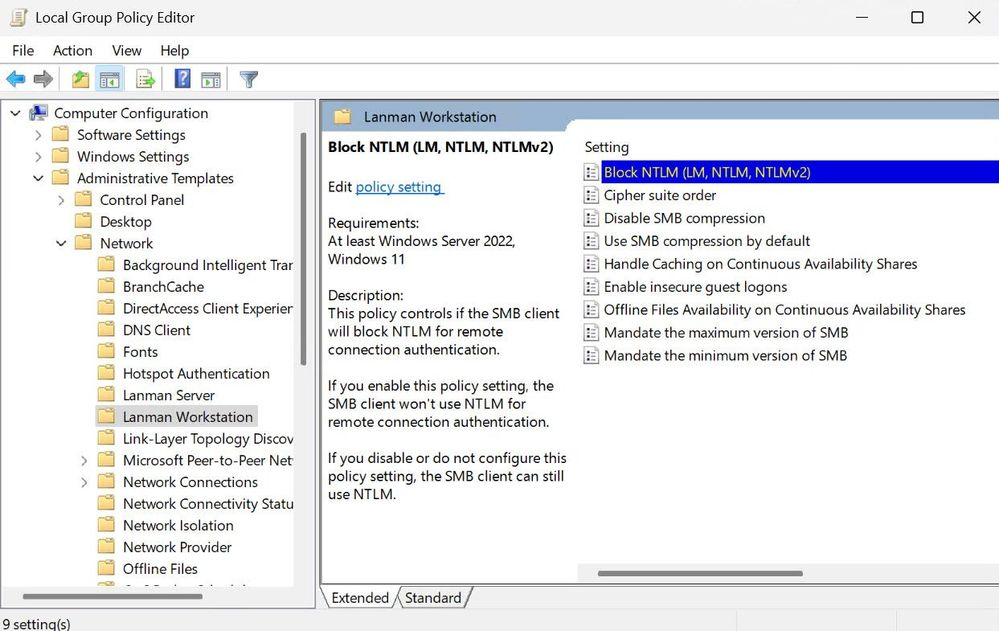
Microsoft says that IT admins can configure this option with Group Policy and PowerShell. It’s also possible to use NET USE and PowerShell to block NTLM on SMB connections on demand.
SMB dialect management capabilities coming to Windows 11
Microsoft has introduced support for SMB dialect management in the Windows 11 Canary build 25951. Previously, Windows SMB would automatically negotiate the highest matched server dialect between SMB 2.0.2 to 3.1.1 clients. This new capability lets IT admins prevent the use of older SMB protocols within their organization. They can configure this option to block connections to potentially vulnerable Windows devices and third-party systems.
With this release, both SMB client and server provide full management support on Windows devices. It eliminates the need for manual registry editing on the client side. If you’re interested, you can find more details about configuring SMB dialects on this support page.


