Microsoft Warns Attackers Now Leveraging Raspberry Robin to Distribute Clop Ransomware

Microsoft has warned users that threat actors have deployed a Clop encryption malware to encrypt enterprise networks affected by the Raspberry Robin worm. The company detailed in a security advisory that the payload had infected around 3,000 devices in 1,000 organizations in the last month.
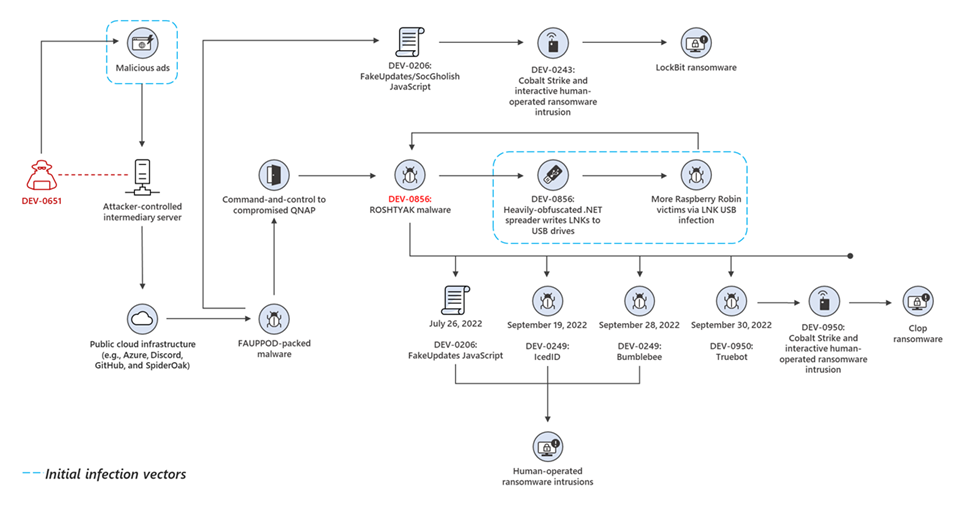
Security firm Red Canary first discovered the Raspberry Robin worm in September 2021. It’s a sophisticated malware that infects machines via malicious USB drives containing a Windows shortcut file that looks like a legitimate folder. The Raspberry Robin has previously been used to deploy the Lockbit ransomware, and Bumblebee, IcedID, and Truebot malware.
According to Microsoft’s Security Threat Intelligence unit, Raspberry Robin is now a part of the complex malware ecosystem with connections to other ransomware infections. The attackers are leveraging the worm to provide unauthorized access to infected Windows devices to deploy ransomware. The data connected by Microsoft Defender for Endpoint indicated that almost 3,000 systems in 1,000 companies had detected at least one threat alert in the past 30 days.
“Raspberry Robin’s infection chain is a confusing and complicated map of multiple infection points that can lead to many different outcomes, even in scenarios where two hosts are infected simultaneously. There are numerous components involved; differentiating them could be challenging as the attackers behind the threat have gone to extreme lengths to protect the malware at each stage with complex loading mechanisms,” Microsoft researchers noted.
How to defend against Raspberry Robin infections
Microsoft’s security experts found some similarities between the code of Raspberry Robin and the malware family Fauppod. The Fauppod malware delivers a JavaScript backdoor to gain unauthorized access to the target system and deploy additional malware.
Microsoft believes that Raspberry Robin will continue to evolve into an increasingly dangerous threat. The company suggests customers to create a robust protection mechanism and enable the attack surface reduction rules to protect their organization. Moreover, Microsoft Defender for Endpoint and Microsoft Defender Antivirus can help to detect Raspberry Robin and other security threats such as Fauppod and Clop.






