Microsoft Defender for Endpoint Gets New Dynamic Tagging Feature to Simplify Device Management

Key Takeaways:
- Microsoft has announced the general availability of dynamic rules for tagging devices in its Defender for Endpoint solution.
- The dynamic rules feature allows administrators to automatically assign tags and device values based on specific conditions.
- Microsoft says that IT admins can create dynamic rules defining conditions using multiple attributes.
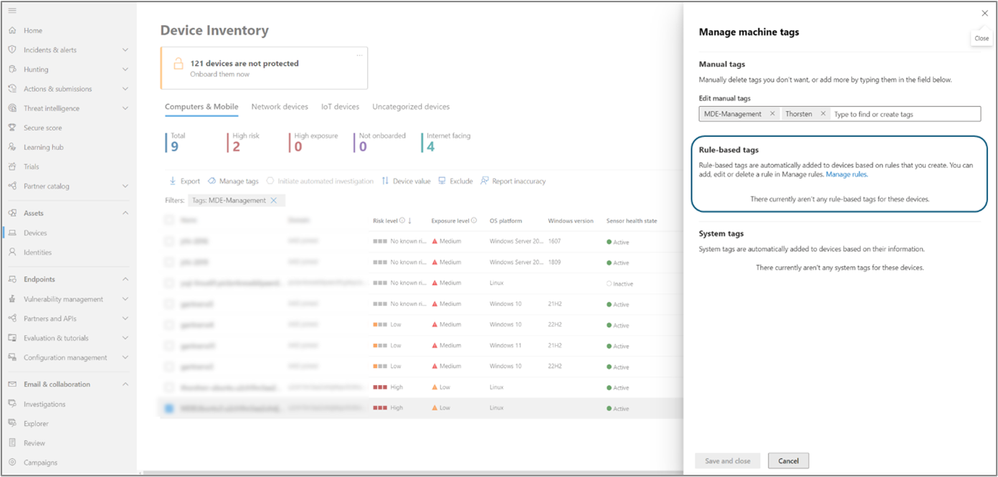
Microsoft has announced that support for dynamic rules for tagging devices is now generally available for its Microsoft Defender for Endpoint solution. This feature allows organizations to create and manage rules, allowing the automatic assignment and removal of tags from devices according to user-defined criteria directly within the Microsoft Defender portal.
Microsoft explained that managing device tags might pose a significant challenge, especially given the dynamic nature of the security landscape. The constant change in device attributes and evolving security requirements may give rise to potential errors, increased complexity, and inefficiencies in security operations.
With dynamic rules, IT administrators can automatically assign tags and device values based on specific conditions. For example, tags can be assigned to devices based on an operating system version. It’s also possible to assign specific values to devices that follow a particular naming convention.
“Admins can now create dynamic rules that define certain conditions using multiple attributes. As devices meet or do not meet these specified criteria, the associated tags are automatically applied or removed. This fluid approach ensures that device tags stay up-to-date, relevant, and aligned with the organization’s evolving security requirements,” Microsoft explained.
Why you should use dynamic tagging?
Microsoft highlighted several benefits of using dynamic tagging for enterprise customers. With dynamic rules, security teams can automate tagging to ensure accurate device classification and improved security insights. Moreover, the feature streamlines the device monitoring and resource allocation process. Dynamic tags make it easier to proactively identify risks and enhance overall security posture.
Overall, the new dynamic tagging capability should help organizations address the complexities associated with device management in today’s rapidly changing cybersecurity landscape. It provides an efficient method for automating security workflows, optimizing device management, and ensuring compliance proactively. We invite you to check out this support page to learn more about dynamic tagging.
