Microsoft Defender for Endpoint to Enable Tamper Protection for All Customers

Microsoft Defender for Endpoint will soon turn on tamper protection by default for all existing enterprise customers. The tamper protection feature prevents malicious apps from making unwanted changes to important security configuration settings on Windows, Windows Server, and macOS.
Microsoft introduced tamper protection in its enterprise endpoint security solution back in 2019. Currently, the feature is turned on by default for new customers with an active Microsoft 365 E5 or Defender for Endpoint Plan 2 subscription. With this release, Microsoft also plans to enable it for all existing enterprise customers.
“Tamper protection in Microsoft Defender for Endpoint protects your organization from unwanted changes to your security settings. Tamper protection helps prevent unauthorized users and malicious actors from turning off threat protection features, such as antivirus protection. Tamper protection also includes the detection of, and response to, tampering attempts,” Microsoft explained in a blog post.
How to opt out of the tamper protection default setting
Microsoft will send notifications to organizations that haven’t configured tamper protection in their tenants. These notifications will alert customers that it will be switched on in 30 days.
Microsoft encourages businesses to turn on the feature to prevent security threats such as human-operated ransomware attacks. However, there is also an option to explicitly opt out of this change by following the steps mentioned below:
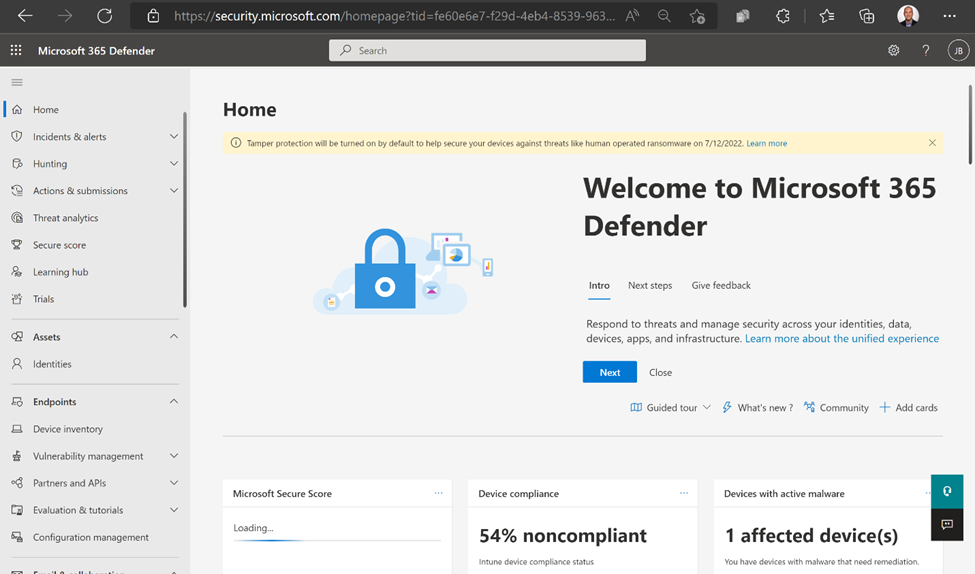
- Head to security.microsoft.com and log in.
- Navigate to Settings >> Endpoints >> Advanced features, enable the tamper protection toggle button and click the Save preferences button.
- Now, disable the tamper protection option and click Save preferences to apply the changes.
Microsoft says that organizations can also choose to disable tamper protection on select devices due to application compatibility issues. IT admins can either use Security Management for Defender for Endpoint or create a profile in Microsoft Endpoint Manager. Let us know in the comments below if you have enabled tamper protection in your organization.



