Making Microsoft Azure Penetration Testing Work to Combat Threats
This short guide explains how Microsoft Azure penetration testing solutions can work to enhance a native public cloud platform within Azure, and what IT professionals can do to proactively defend against evolving numbers of serious threats, thus bolstering their security posture.
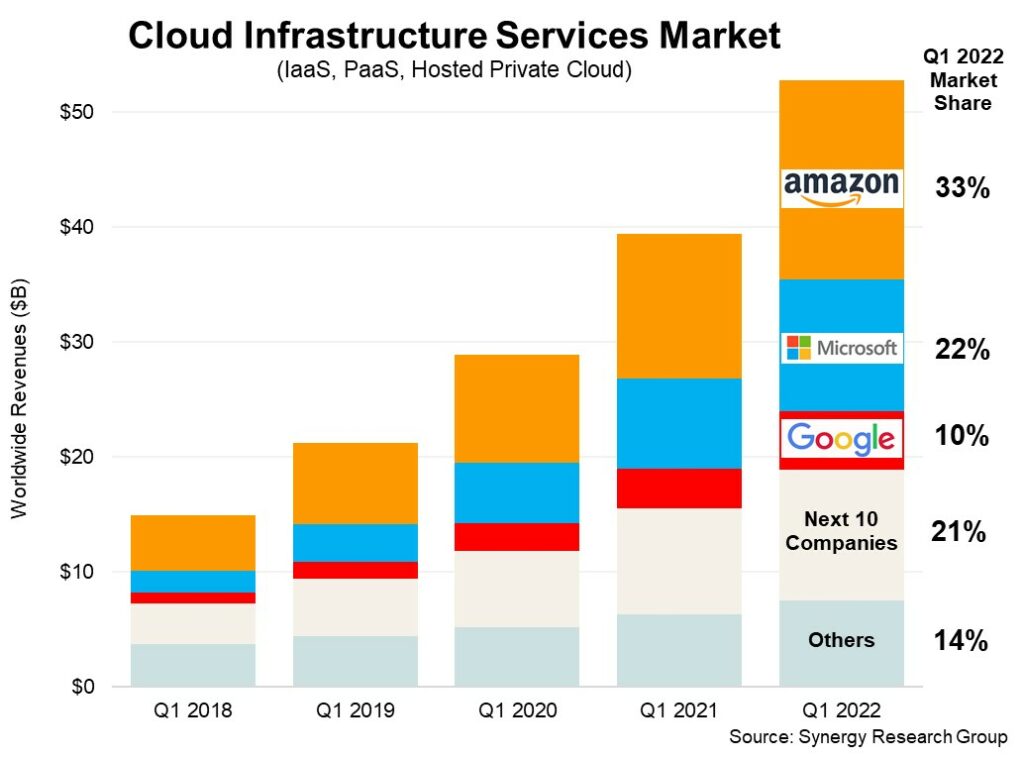
As far as public cloud infrastructure solutions go, there is perhaps none more versatile or worthwhile than Microsoft Azure. The growth in Microsoft Azure usage across enterprises is apparent, with a 26% growth in Q4 2023; it’s no wonder why the platform now occupies a huge portion of the cloud infrastructure services market share. It’s estimated that the total number of worldwide Azure users borders around 1 billion, with the platform generating over $75.3 billion last year alone.
Despite Azure services being entrusted by numerous organizations to build scalable environments for applications, storage, networking, and many others, the inherent security issues that lie within public cloud services remain. For every scalable Azure configuration that an organization deploys comes increased cyber risks and threat vectors that demand proactive, responsive solutions without compromising data integrity or environmental stability. IT professionals and experts must also comply with stringent and demanding protection standards, regulations and legislation if they are to avoid scrutiny and hefty fines.
Microsoft Azure penetration testing
One of the most proactive solutions to bolster cyber posture is by utilizing penetration testing, which minimizes a business’s attack surface and combines incumbent Azure resources and controls with strengthened external validation.
The need for validation testing in Azure environments
Azure comes packed with identity and access management, network security, and monitoring controls, to name but a few. Features like Entra ID, Azure DDoS Protection, and Microsoft Sentinel provide fundamental safeguards that are worth deploying if you are to create a stable foundational level of security in your organizational infrastructure and networks.
However, native security tools only take you so far when considering the diversifying threat landscape. Organizations need specialist external solutions such as enterprise-grade penetration testing services to uncover hidden and previously unexplored vulnerabilities, ranging from unpatched endpoints to insecure and non-encrypted protocols between servers.
When consulting with Microsoft Azure penetration testing providers, your organization will be aided by third-party cyber security experts who can ethically hack into systems and networks to uncover weaknesses both evident and covert. In the same way that a malicious actor might execute a calculated attack on an organization, penetration testing involves leveraging human ingenuity and creativity to find and exploit the flaws lying dormant in a system. The most sophisticated attacks draw similarities to known cyber security assessments like red team, blue team and purple team exercises, blending elements from proactive vulnerability scanning, risk assessments, and incident response solutions.
Put simply, these sophisticated penetration tests (or pen testing) emulate how methodical real-world cybercriminals and hackers would operate given the opportunity.
Is penetration testing disruptive?
While penetration testing may seem like an invasive measure on the surface, proper rules of engagement ensure ethical conduct and transparency. Specialist firms with proper accreditation from institutions like CREST are being held accountable for their service quality and delivery. It’s also required by regulations like PCI DSS and ISO 27001, so if you consult a firm with these compliance credentials in tow, you’ll know that the firm can effectively deliver solutions for highly regulated and enterprise organizations.
A pen testing company’s main goal is to help organizations using Azure fortify their in-house security measures and controls, not to exploit data or demand ransoms like hackers might. That said, penetration testing may involve requiring access to sensitive business or personal information during the attack simulations. However, most pen testing providers will declare what could be uncovered during their simulations and give you ample time to back that data up for your peace of mind.
When coordinated responsibly, Microsoft Azure penetration testing provides objective, unbiased insights that capitalize on your native Azure infrastructure controls. Both your internal IT team and third-party pen testers can align efforts and findings to give you complete reassurance of data integrity and stability.
Key benefits of penetration testing for Azure users
Conducting periodic penetration testing exercises on systems and networks using Azure offers an organization many benefits.
Uncovering unknown vulnerabilities
The major benefit of security testing is revealing vulnerabilities that companies did not know existed. Azure Firewall’s intuitive encryption controls offer threat protection for workloads, but cannot identify anomalies outside of these confines. Azure developers cannot anticipate every single weakness in a company’s bespoke setup. Human-powered penetration testing uncovers issues that native, automated scans – such as those from Sentinel and Azure DDoS – may miss.
Using pen testing tools and techniques such as phishing, patch exploitation, brute force, and social engineering attacks, Azure pen testers can bypass defenses and expose risks that Azure controls may not adequately mitigate.
Providing an objective assessment
While Azure users have more familiarity with their in-house environments, penetration testing experts have the distinction of obtaining an impartial view. Their fresh eyes and perspectives identify gaps that in-house users often overlook or underestimate, and that require further investigation.
Third-party specialists may be less concerned about the nature of an Azure environment deployment, instead focusing on ways that systems and software can be exploited. This neutrality allows for more objective assessments and findings.
Prioritizing remediation efforts
Sometimes, Microsoft Azure penetration testing can uncover overwhelming numbers of vulnerabilities in the infrastructure. Third-party testing firms will usually rate findings based on potential impact, severity, and frequency.
Azure Security Center and Microsoft Sentinel provide centralized SIEM and SOAR solutions that aggregate data, which can often correlate to an anomalous incident, but penetration testing accounts for findings outside of your infrastructure as well as within it.
Upon the delivery of findings and results, a test can help organizations prioritize which flaws are the most dangerous or prone to exploitation, and remediate them accordingly.
Demonstrating due diligence
Organizations are under increased scrutiny to safeguard customer, client, and stakeholder data. Companies in highly regulated industries, like healthcare and finance, often face severe fines if they fail to secure data, which, in turn, can have a profound effect on their reputations.
Recent examples range from the ARcare data breach which impacted hundreds of thousands of patients, to OneTouchPoint’s hack which compromised sensitive and personally identifiable information of members.
Penetration testing simulations prove to stakeholders and customers that you take cloud security seriously and are conducting due diligence proactively. Even if tests fail, you are holding yourself accountable for addressing weaknesses, leading to improved confidence all around.
Enhancing cyber resilience
Ultimately, penetration tests prepare teams of Azure users to handle real attacks with increased confidence. They are conducted to help you understand all potential vulnerabilities and address them before they are exploited by a malicious actor.
Addressing weak spots proactively will make Azure environments more resilient against targeted data breaches, which have proven devastating for firms making use of this reliable cloud technology before.
Integrating pen testing into Azure management processes
To maximize value from penetration testing, organizations should make it an integrated component of cloud management. It’s recently been reported that it takes 71% of penetration testers a week to a month to conduct a simulation, with few organizations waiting longer than a week to receive results. However, given how fast threats are evolving, this brief period can leave companies prone to exploitation.
Penetration testing should be integrated as a key strategy from the outset, whether that involves a white, black or gray box test methodology, or a specific web application, wireless network, or server. Incorporate periodic testing into your long-term plans with your Azure setup. To prevent it from being overlooked, budget for regular Azure penetration testing, making them part of your regular governance and due diligence processes.
Define Rules of Engagement (ROE)
Penetration testing rules of engagement establish your team’s legal authority and responsibility to conduct tests in an ethical, controlled manner. Rules specify limitations and restrictions, such as testing hours and methodologies, which testers must acknowledge and comply with. Establishing firm procedures will foster increased feelings of trust and accountability.
Integrate internal staff
While penetration testing is vital to obtain an outside perspective, internal Azure developers and security engineers should be included when assessing asset vulnerability. Their key insights and system familiarity can prove effective at making tests more worthwhile and impactful, rather than a simple tick-box exercise. Combining internal and external security expertise will allow for more thorough and conclusive evaluations.
Bolstering Azure cloud security requires both internal and external efforts
Microsoft Azure provides users with numerous native controls to establish baseline security. However, organizations cannot solely rely on in-house tools and software add-ons to create a multi-layered approach.
Periodic penetration testing by accredited third-party experts offers the most thorough evaluation of cloud defenses. Leveraging Azure’s native controls and engaging third-party professionals will solidify an organization’s security so that threats and anomalies can be detected with complete reassurance.
Table of contents
- Microsoft Azure penetration testing
- The need for validation testing in Azure environments
- Is penetration testing disruptive?
- Key benefits of penetration testing for Azure users
- Providing an objective assessment
- Prioritizing remediation efforts
- Demonstrating due diligence
- Enhancing cyber resilience
- Integrating pen testing into Azure management processes
- Define Rules of Engagement (ROE)
- Integrate internal staff
- Bolstering Azure cloud security requires both internal and external efforts



