Malicious npm Packages Masquerade as Trusted Libraries to Steal Credentials
Rogue npm packages mimic trusted libraries to steal developer credentials.
Key Takeaways:
- Ten malicious npm packages mimic popular libraries to steal developer credentials.
- Attackers use fake CAPTCHAs and layered malware to evade detection.
- Developers are urged to verify package names and tighten supply chain security.
Cybersecurity company Socket has discovered ten malicious npm packages that masquerade as widely used libraries to stealthily harvest developer credentials. This sophisticated attack uses fake CAPTCHA, obfuscated code, and multi-stage payloads to harvest sensitive data from unsuspecting victims.
An npm package is a reusable piece of code that developers can share and integrate into their projects using the Node Package Manager (npm). These packages often contain libraries, tools, or modules that simplify tasks like building web applications, managing servers, or handling data. Developers can install them with a single command, which makes them a convenient way to add functionality without writing everything from scratch.
How are malicious npm packages targeting developers?
The attack begins with the installation of a typosquatted npm package that closely mimics the name of a legitimate library. Once installed, the package uses a post-install script to automatically execute malicious code. This script opens a new terminal window to bypass visibility in the original install process, and displays a fake CAPTCHA prompt to distract the user while the malware begins its operation.
Behind the scenes, the code is heavily obfuscated using multiple techniques such as eval wrapping, XOR encryption, and control flow manipulation to avoid detection. The malware fingerprints the victim by sending their IP address to a remote server, then downloads a large binary payload built with PyInstaller. This payload is designed to extract sensitive credentials from system keyrings, browsers, configuration files, and cloud services, which makes it a stealthy credential-harvesting tool.
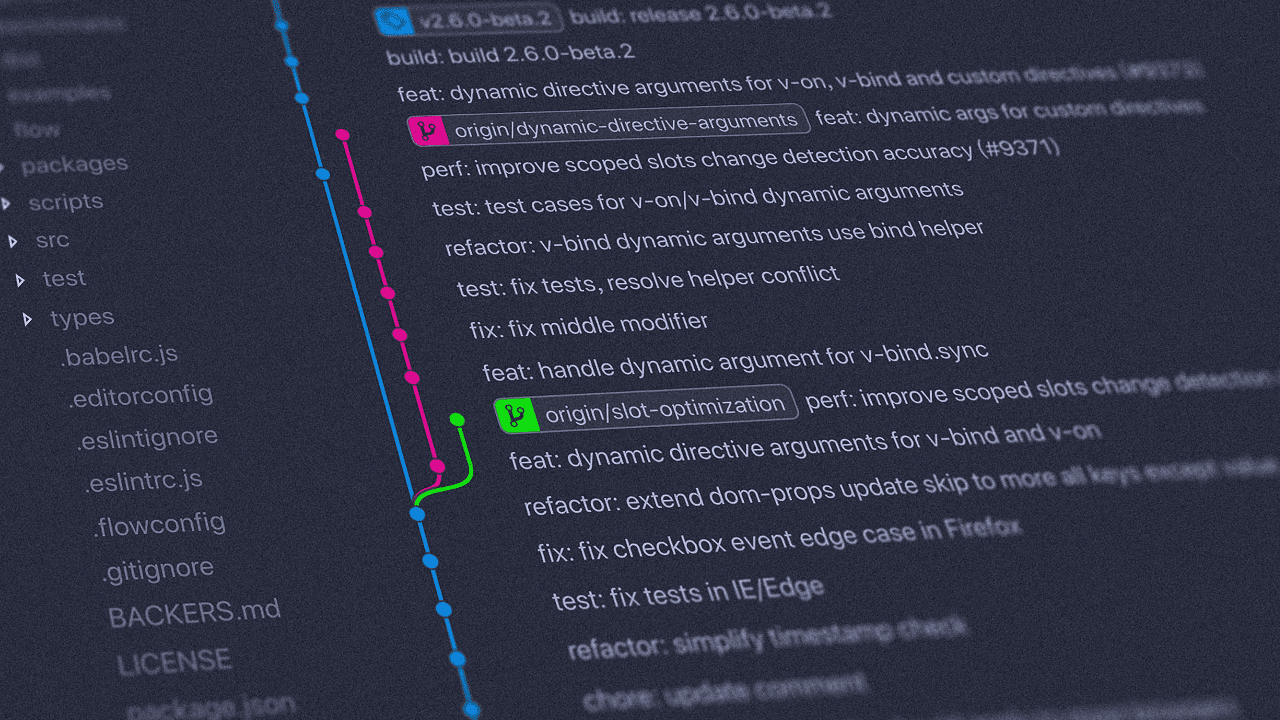
The attackers crafted malicious npm packages that closely resembled trusted libraries by using subtle typos in their names. These fake packages targeted popular tools like TypeScript, discord.js, ethers.js, nodemon, react-router-dom, and zustand, which are widely used in web and JavaScript development.

Tools and best practices for securing the npm supply chain
To defend against typosquatting attacks on npm, developers should carefully verify package names before installation, especially when working with unfamiliar dependencies. Moreover, security teams must use automated security tools (like Socket’s GitHub app or CLI) to flag suspicious packages, and dependency monitoring services also help alert about changes or risks in their software supply chain
Organizations should enforce secure development practices such as enabling two-factor authentication, rotating credentials regularly, and auditing systems for signs of compromise. They must use network monitoring to detect unusual outbound connections, and sandbox environments for testing new packages to prevent malicious code from affecting production systems.






