Install and Configure Puppet 5 Part 2: Set Up Puppet
As a companion to my series on managing Windows Server with Puppet 5, this short two-part article will guide you through installing your own Puppet 5 server on Red Hat Linux in Hyper-V.
In the final part of this two-part article, I’m going to show you how to install Puppet 5 on Red Hat Linux. In the first part, I installed Red Hat Enterprise Linux (RHEL) in a Hyper-V virtual machine running on Windows 10. I also registered and subscribed RHEL using my Red Hat Developer Program account.
If you missed my series of articles on managing Windows Server using Puppet, here are the links to the pieces published so far.
Managing Windows Server with Puppet Part 1: Configure Puppet Master and Bootstrap the Puppet Agent in Windows Server
Managing Windows Server with Puppet Part 2: Log in to Puppet Master, Accept Node Certificate, and Test Connectivity
Managing Windows Server with Puppet Part 3: Install Modules and Edit the Site Manifest
Managing Windows Server with Puppet Part 4: Working with Files and ACLs
Managing Windows Server with Puppet Part 5: Managing Local Users and Groups
Managing Windows Server with Puppet Part 6: Installing, Updating, and Removing Software
Managing Windows Server with Puppet Part 7: Installing Active Directory
Download and Install Puppet
Let’s get started and install Puppet. The VM will need Internet connectivity to complete the steps below.
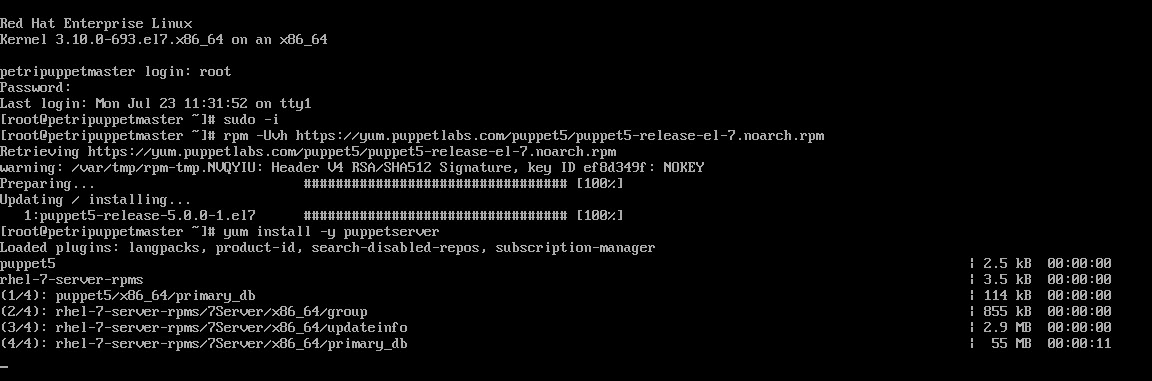
- Boot the Red Hat VM using Hyper-V manager.
- Log in to Red Hat using root. Type root at the login prompt. Type the password for the root account when prompted and press ENTER.
- Type sudo -i and press ENTER to make sure the following commands run with elevated privilege.
- Download the Puppet 5 repository using the rpm command as shown here:
rpm -Uvh https://yum.puppetlabs.com/puppet5/puppet5-release-el-7.noarch.rpm
- Install Puppet server using yum:
yum install -y puppetserver
Configure Puppet
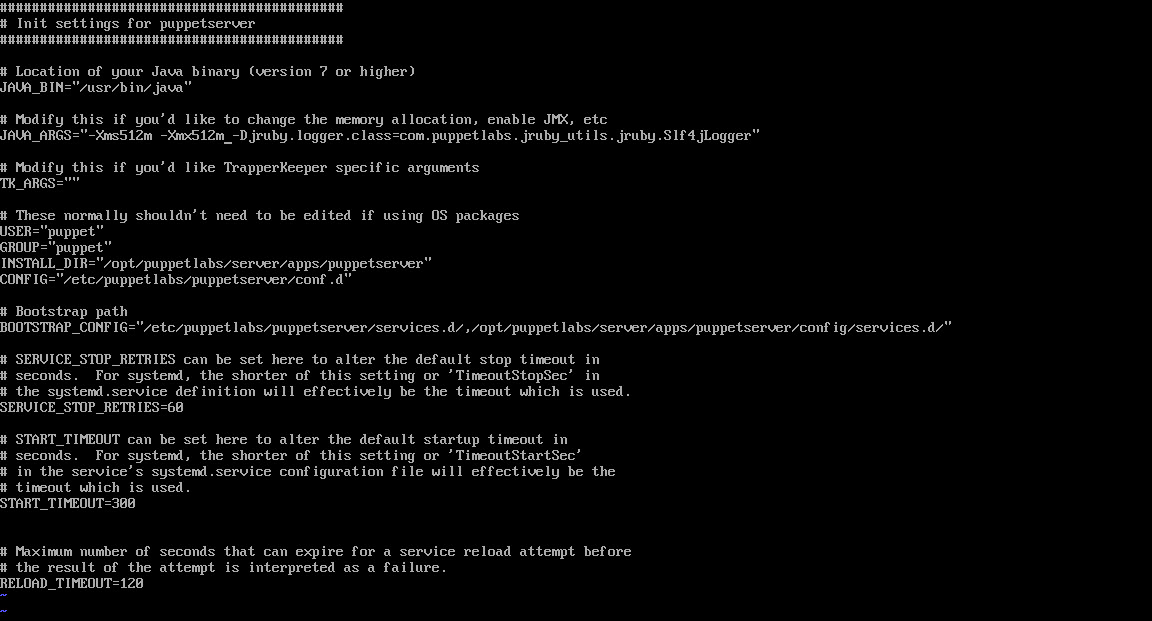
The next step is optional. I want to configure Puppet to use a maximum of 512MB of RAM because I want to assign the VM just 1GB of RAM. If you have enough available memory, you can skip this step and leave the default RAM assignment.
- Use the vi text editor to change the RAM assignment in the puppetserver config file. If you’re not familiar with vi, see Edit the Site Manifest in Managing Windows Server with Puppet Part 3 on Petri.
vi /etc/sysconfig/puppetserver
- Change the JAVA_ARGS parameter so that it reads -Xms512m -Xmx512m
- Quit vi and write the file to disk.
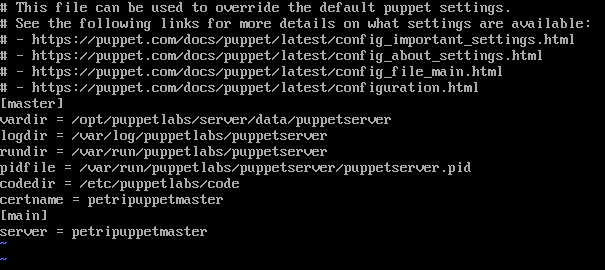
- Edit the puppet.conf file to add the server name and certificate name.
vi $confdir/etc/puppetlabs/puppet/puppet.conf
- Add the certname parameter to the existing [master] section of the file. The certname should be the same as the name of the Puppet Master server you will provide when installing agents. If the names don’t match, Puppet agents will fail to connect to the master.
certname = petripuppetmaster
- Add the server parameter to the [master] section of the file. If the section doesn’t exist, add it to the file. The parameter is used to give the server a name.
[master]
server = petripuppetmaster
- Quit vi and write the file to disk.
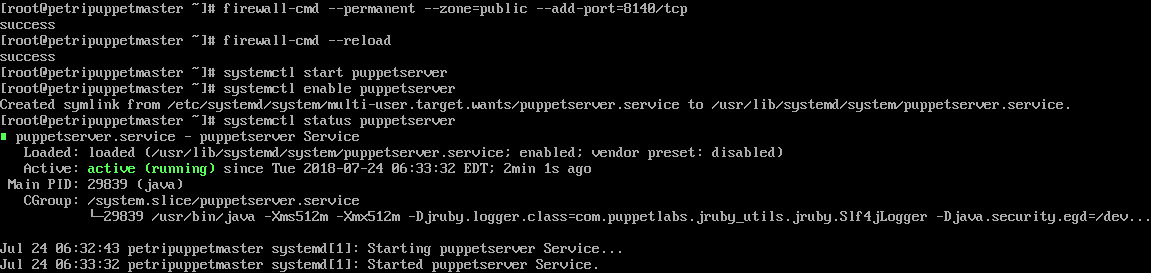
- Configure the firewall using firewall-cmd to allow inbound tcp connections on port 8140:
firewall-cmd --permanent --zone=public --add-port=8140/tcp firewall-cmd –reload
- Now start and enable the Puppet Master service using systemctl. Enabling the service sets it to start automatically.
systemctl start puppetserver systemctl enable puppetserver
- Finally, restart the server to get access to the Puppet commands in the VM console.
Troubleshooting
That’s it! The Puppet Master is now ready to receive incoming requests from agents. You can check the status of your server using the following commands. Use puppet status to check the version number and whether the server is active. Netstat can be used to check that Puppet is listening on port 8140. Puppet is a Java application, so you’ll see Java and not Puppet listed in the command’s output.
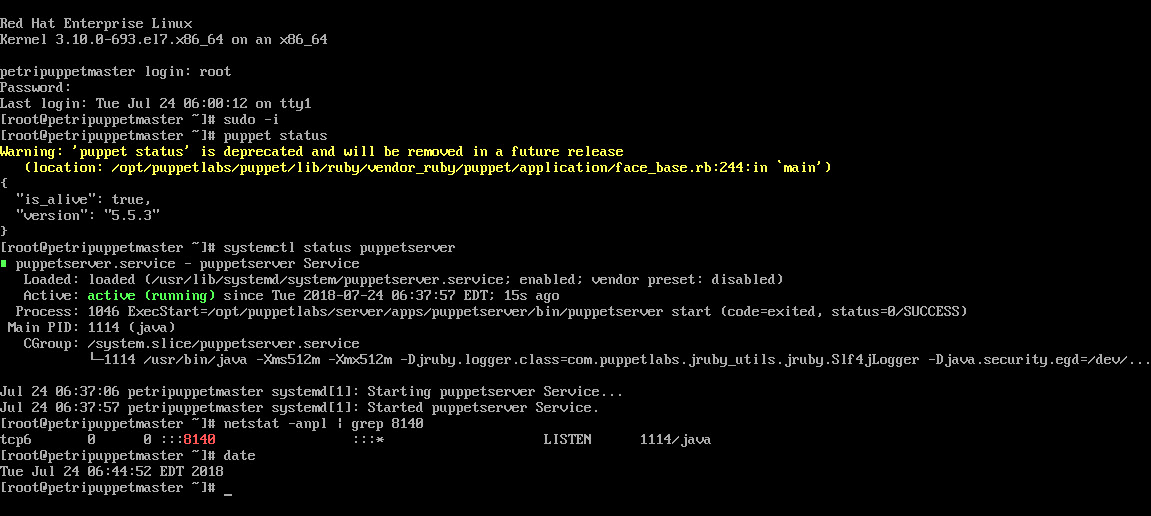
systemctl status puppetserver puppet status netstat -anpl | grep 8140
Puppet relies on DNS, so make sure that you can access agents and servers by domain name. You can add entries to the hosts file on Linux using vi if necessary:
vi /etc/hosts
Additionally, the Puppet Master time and date must be in-sync with your Puppet agents. You can check the time, date, and time zone using the date command.
date
Don’t forget to follow my series on managing Windows Server using Puppet for more information on how to work with Puppet 5.