How to Solve Invalid_Client Error When Joining Windows 10 to Azure AD
Windows 10 devices can be registered or joined (connected) to Azure Active Directory (recently renamed Microsoft Entra ID) domains. But not for the first time, I’ve come across a problem when trying to connect a device to Azure AD. In this article, I’ll show you how to solve the Invalid_Client error when joining Windows 10 to Azure AD.
There are two ways that you can join Windows 10 to Azure AD. The first is during the OOBE phase of Windows 10 setup. If you are installing Windows 10 Enterprise, by default you are prompted to enter a Microsoft work or school account with which you join the device to Azure AD. Secondly, a device can be joined to Azure AD in the Access work or school section of Accounts in the Windows 10 Settings app.
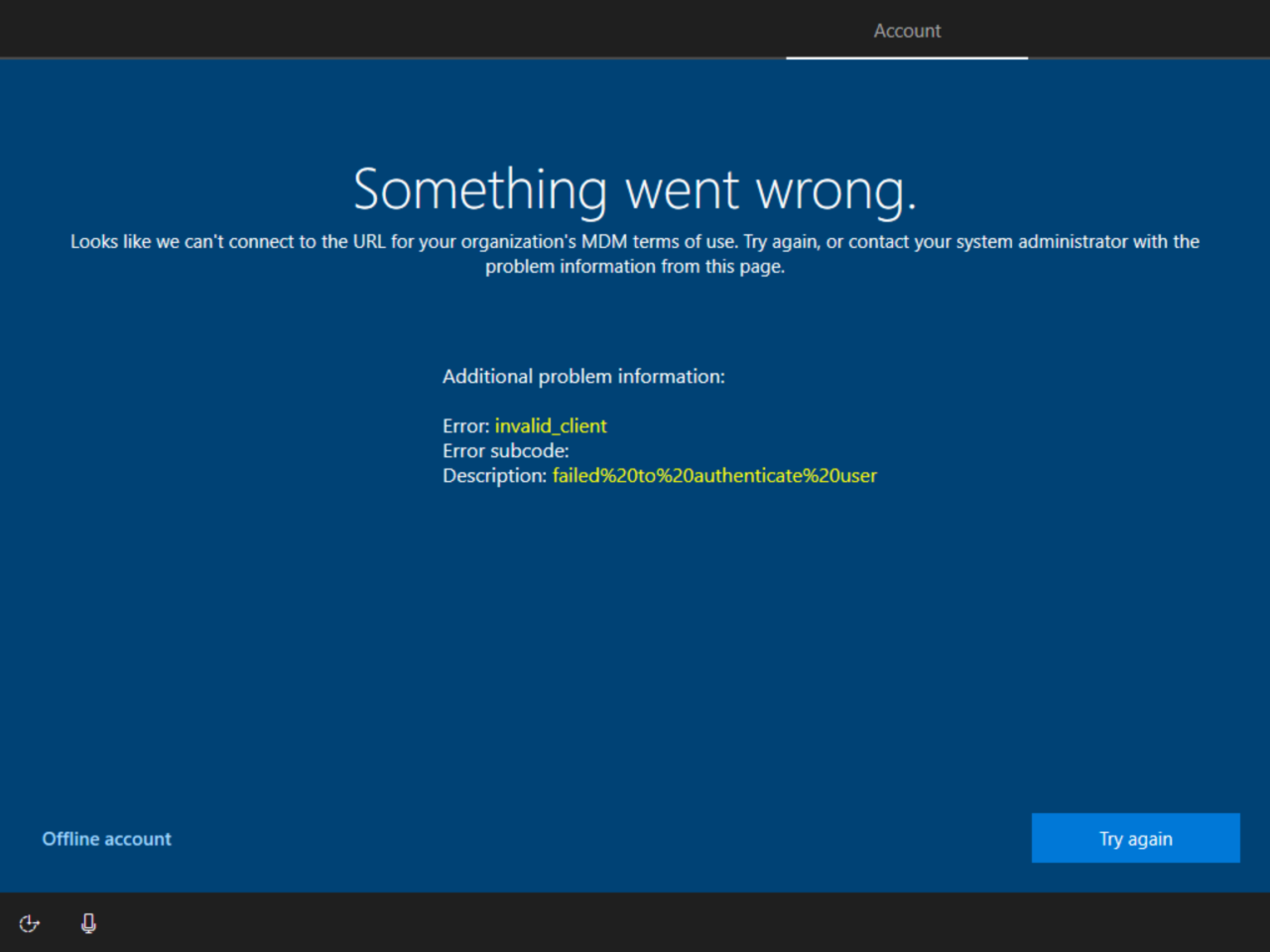
Both methods were throwing the same error: ‘Something went wrong.’ Looks like we can’t connect to the URL for your organization’s MDM terms of use. Try again, or contact your system administrator with the problem information from this page. Error: invalid_client Description: failed%20to%20authenticate%20user.
Troubleshooting Azure AD Join
There are a few items you need to check when dealing with these kind of errors. The first is that the user account has the necessary rights to join Windows 10 to Azure AD. There’s a setting in Azure AD which controls whether users can join devices to Azure AD and how many devices they can join. For more information on that setting, check out Join Windows 10 to Azure Active Directory During OOBE on Petri.
Azure Active Directory Licensing
Next on the list is licensing. Microsoft 365 and Office 365 subscriptions include the free edition of Azure AD, which supports Azure AD Join and many other features. You can find a comparison of Azure AD editions on Microsoft’s website here.
But you should note that the free edition of Azure AD doesn’t include all the features of Azure AD Join. To get the features listed below, you’ll need Azure AD P1 or P2 licenses:
- Mobile Device Management (MDM) autoenrollment
- Local admin policy customization
- Self-service BitLocker recovery
- Enterprise state roaming (ESR)
The account I was using to join Windows 10 to Azure AD was assigned a Microsoft 365 Business Standard license. That means there is no Microsoft Intune license included with the Microsoft 365 subscription. To get Intune, which is Microsoft’s MDM service, I would need to either license Intune separately or upgrade to a Microsoft 365 Business Premium license. Nevertheless, I should be able to perform an Azure AD join using a Microsoft 365 Business Standard account.
Disable MDM autoenrollment
After some digging around on the Internet, I found that the issue is likely connected to MDM autoenrollment. As the Microsoft 365 Business Standard account isn’t licensed for Intune, Azure AD join fails because the account is enabled for MDM autoenrollment.
The solution is to disable MDM autoenrollment for the account, or all accounts, in the Azure AD tenant. But hold up. Without an Azure AD P1 or P2 license, there is no access to modify MDM autoenrollment settings.
This led me to call Microsoft support. I was advised to assign a trial Azure AD Premium license to an account and turn off MDM autoenrollment. So, that’s what I did. And hey presto, I was able to join the Windows 10 device to Azure AD with no errors. To be clear, the work or school account used to join Windows 10 to Azure AD does not need an Azure AD Premium license. The license is only required to modify the MDM enrollment settings.
To disable MDM autoenrollment, follow these instructions:
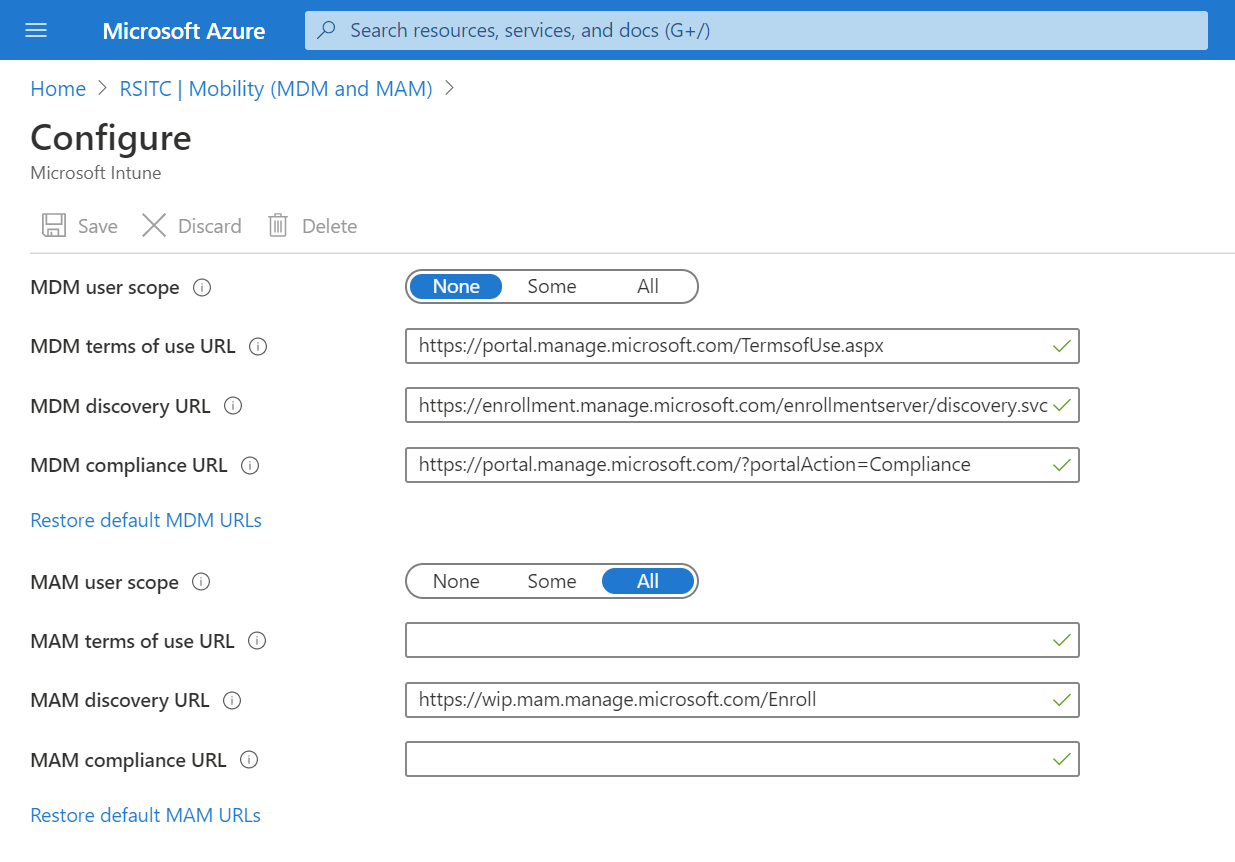
- Open the Azure management portal using this link and sign in to an account with global admin rights. The link takes you straight to the Mobility (MDM and MAM) section of Azure AD.
- Click Microsoft Intune on the right of the portal.
- On the Configure screen, set MDM user scope to None.
- Alternatively, you can enable MDM autoenrollment for specific users only by selecting Some and then selecting some groups.
- Click Save to commit the changes.
Once the changes have been saved, you should be able to join Windows 10 to Azure AD using work or school accounts that are not enabled for MDM autoenrollment.