How to Enable Windows Sandbox
Back in August, I wrote on Petri about a new feature that Microsoft was reportedly introducing in Windows 10 Enterprise called InPrivate Desktop. Exposed during a bug-bash quest in the Feedback Hub, the text of the quest said that InPrivate Desktop would provide admins a way to launch a throwaway sandbox for secure, one-time execution of untrusted software. As Brad reported, this feature is now being officially previewed in the latest Windows Insiders update for Windows 10, build 18305.
InPrivate Desktop Renamed Windows Sandbox
Windows Sandbox provides an isolated, temporary desktop where users can run software that might make unwanted changes to Windows. Every time Windows Sandbox is started, users are presented with a clean installation of Windows, meaning no files are preserved from the previous session. And unlike Hyper-V virtual machines, you won’t need to download load a Windows image file to work with Windows Sandbox.
Enable Windows Sandbox
There are a few prerequisites before you can use Windows Sandbox. You must be running Windows 10 (18305 or later) 64-bit Pro or Enterprise SKUs, with at least 4GB of RAM, virtualization capabilities enabled in the BIOS, 1GB of free disk space, and at least 2 CPU cores.
Windows Sandbox is a built-in Windows feature which you can enable from the Control Panel.
- Open the Control Panel.
- Click Programs.
- Under Programs and Features, click Turn Windows features on or off.
- Give consent or provide an administrator password in the UAC prompt.
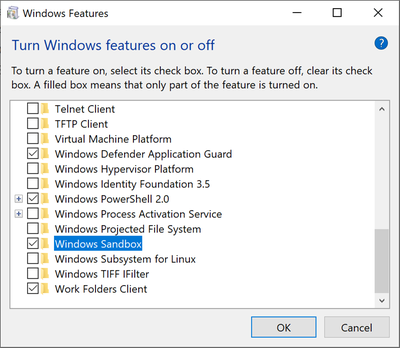
- Scroll down the list in the Windows Features dialog and check the box next to Windows Sandbox.
- Click OK to install the feature.
You might be prompted to restart your device.
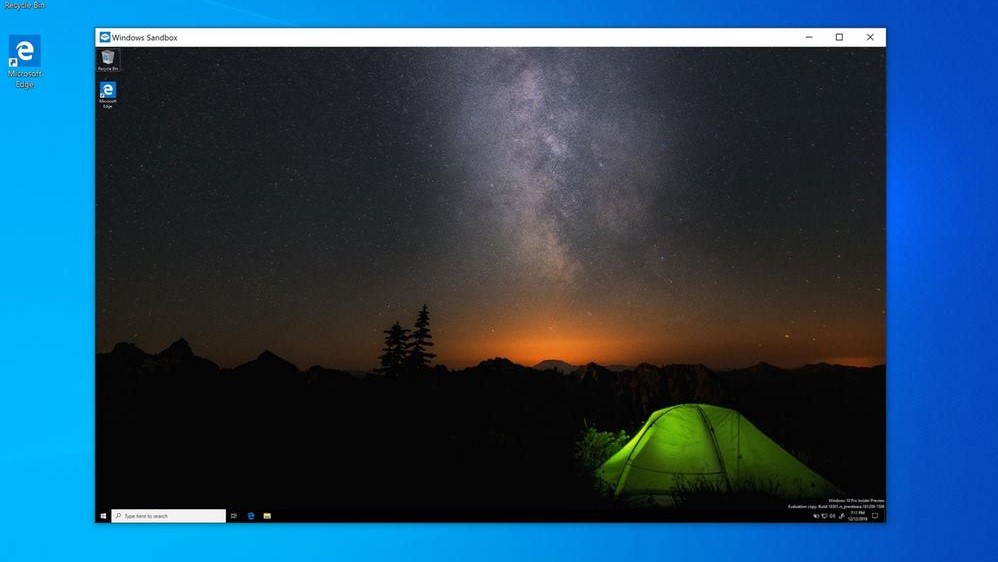
Using Windows Sandbox
Once the installation is complete, you can start the sandbox from the Start menu. You’ll need to provide UAC consent to run the sandbox. Once Windows has booted in the sandbox, you can copy any files you want to run on the desktop from the host device. As soon as the sandbox window is closed, all the files and changes made are discarded.
Windows Sandbox vs Virtual Machine
Windows Sandbox uses a dynamically generated image based on the host’s Windows 10 installation, meaning you won’t have to manually download a VHD file or install Windows from an ISO file in the sandbox. The base image is around 100MB in size and only 25MB in compressed form when Windows Sandbox is not installed.
Memory management is also slightly different, allowing the host to reclaim memory from the sandbox if required. And ‘Direct Map’ allows the sandbox to securely use the same physical memory pages as the host OS. The integrated kernel scheduler lets the host OS decide when Windows Sandbox runs, much like the threads for any normal process, making sure that the host stays responsive under load. Microsoft says that these technical differences from Hyper-V virtual machines aim to treat Windows Sandbox like an app but at the same time provide the security guarantees of virtual machines.
From a performance perspective, Windows Sandbox uses snapshots and cloning to save the memory, CPU, and device state to disk so that you don’t need to boot Windows from scratch every time the sandbox is started. Additionally, hardware accelerated graphics rendering is supported by allowing apps in the sandbox or Hyper-V to directly use graphics APIs, providing that you have a compatible graphics card and WDDM 2.5 or newer drivers.
Don’t forget that Windows Sandbox is in preview and is likely to have bugs and performance issues. I’ll be updating Petri with more information on Windows Sandbox when the next feature update for Windows 10 reaches general availability.
