Windows Sandbox: A New Lightweight Desktop Environment for Running Untrusted Apps
We have all be there before, you download an application you think is safe, but in the back of your mind, you are second-guessing yourself. You run a virus scanner, maybe toss it into a VM, but eventually, you double-click the executable and hope that the application isn’t going to crypto-lock all your data.
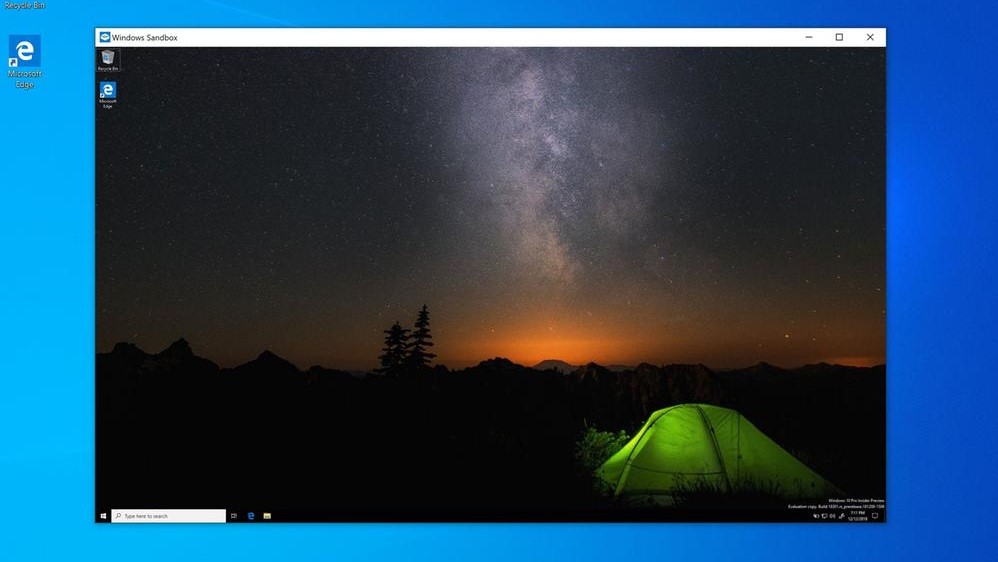
With the next major update to Windows 10, Microsoft will introduce Windows Sandbox, a new feature that will make running these types of application significantly more secure. When you run Windows Sandbox, it creates an isolated, temporary, desktop environment where you can run untrusted software without the fear of lasting impact to your environment.
Microsoft made this announcement in the Windows Kernel Internals blog, but considering how significant this feature is, you would think that they would have attempted to make a bit more noise as this security functionality is a perfect carrot to get users to migrate from Windows 7 to 10.
As the post notes, Windows Sandbox has the following properties:
- Part of Windows – everything required for this feature ships with Windows 10 Pro and Enterprise. No need to download a VHD!
- Pristine – every time Windows Sandbox runs, it’s as clean as a brand-new installation of Windows
- Disposable – nothing persists on the device; everything is discarded after you close the application
- Secure – uses hardware-based virtualization for kernel isolation, which relies on Microsoft’s hypervisor to run a separate kernel which isolates Windows Sandbox from the host
- Efficient – uses integrated kernel scheduler, smart memory management, and virtual GPU
And to run this feature, your PC will need to meet the following requirements:
- Windows 10 Pro or Enterprise build 18301 or later
- AMD64 architecture
- Virtualization capabilities enabled in BIOS
- At least 4GB of RAM (8GB recommended)
- At least 1 GB of free disk space (SSD recommended)
- At least 2 CPU cores (4 cores with hyperthreading recommended)
This feature has been talked about for some time and was previously known as InPrivate Desktop. As Foley notes, its codename was Madrid and if you are running the latest insider builds, you can try out the feature today.
But, as always with a new feature, especially one like this, there may be bugs and I wouldn’t go intentionally testing running viruses in this sandbox in a production environment. If you aren’t running an insider build, look for this feature in the next update to Windows 10 which should arrive around March of 2019.