Hardware-Enforced Stack Protection Preview Arrives For Windows 10
Back in 2016, Intel announced in partnership with Microsoft that it was working on a new system for its CPUs to block malicious code that uses Return-Oriented Programming (ROP) and Jump-Orientated Programming (JOP).
Dubbed Control-flow Enforcement Technology (CET), Intel’s new protection tech uses the hardware architecture of the CPU to create controls, otherwise known as shadow stacks, to help prevent code-reuse attacks. Intel explains in its blog post:
Previously, the preferred method of making a computer follow your malicious desires was to inject code directly into memory to be run. This tactic has become progressively more difficult due to the introduction of several security features over the years. So now, savvy aggressors have turned to rely on code-reuse attacks like Return Oriented Programming (ROP) and Jump Oriented Programming (JOP) which allow for exploitation without code injection. According to Microsoft, almost all exploits discovered in recent years targeting their products have used ROP techniques.
Because ROP/JOP legitimately harvest code already in memory for reuse, attackers use these techniques to create malware in a way that can be difficult to detect. And because no code-injection is required, protections already part of Windows 10 and Intel CPUs, like Address Space Layout Randomization (ASLR), Data Execution Prevention (DEP), and No Execute (NX) bit, can be easily bypassed.
Return addresses and shadow stacks
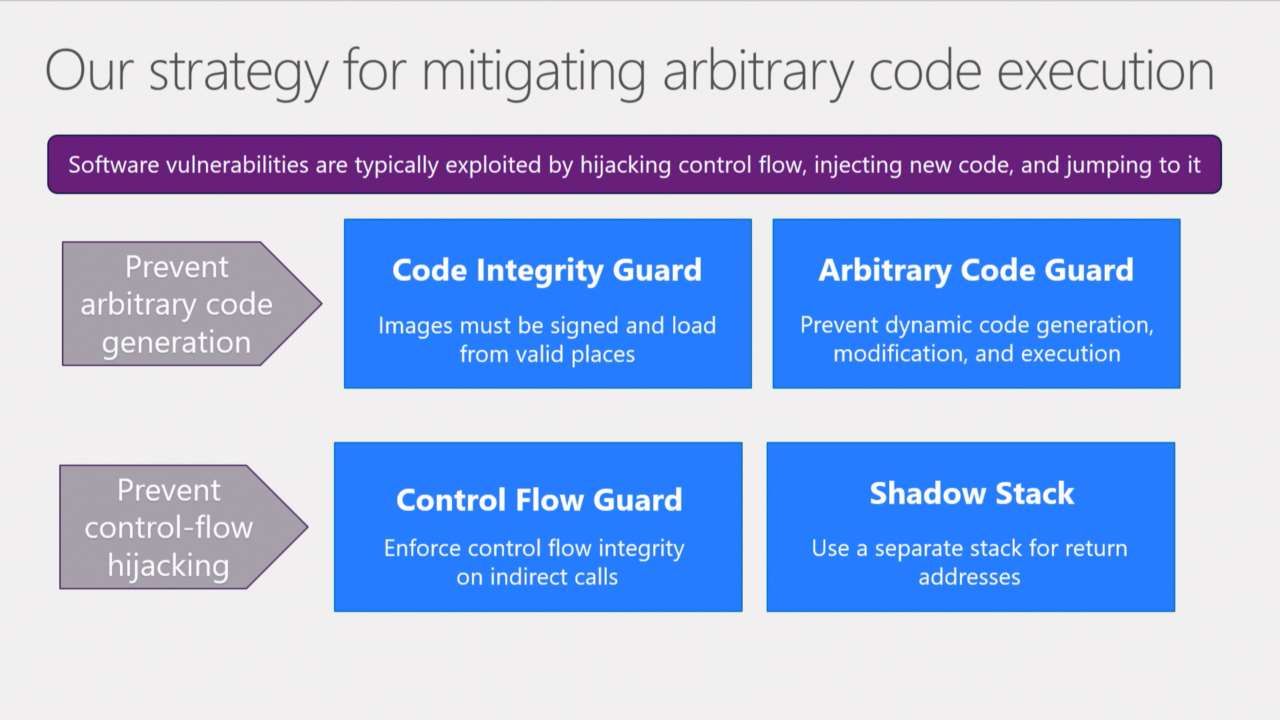
In a post on Microsoft’s website in late March, Microsoft’s kernel protection team wrote that memory safety vulnerabilities, like buffer overruns, were the most common. Windows 10 Control Flow Guard (CFG) already helps enforce integrity on indirect calls. Hardware-Enforced Stack Protection enforces integrity on return addresses on the memory stack.
CET uses a shadow stack that is protected by the CPU’s memory management unit (MMU). The shadow stack only contains return address and it cannot be accessed by normal program code. When a subroutine is called, the return address is recorded on the thread’s stack and in the shadow stack.
When a return instruction is processed, the CPU checks that the return address stored in the thread stack and the shadow stack match. In short, when returning from a subroutine, CET checks that the stack hasn’t been modified to take over the flow of the software.
Is CET effective at stopping memory-based attacks?
There seems to be a consensus that CET should make systems much more resistant to common memory attack techniques. And even better, with little in the way of a performance hit.
The kernel protection team at Microsoft says that applications need to be compiled with a new linker flag to request protection from the kernel. Hardware-Enforced Stack Protection is an opt-in feature on Windows Insider builds and hardware that supports it. Making the feature opt-in gives developers the chance to test and validate their apps.
When and where will CET protection be available?
None of Intel’s commercially available processors currently support CET. According to Yarden Shafir and Alex Ionescu of Windows Internals Training & Consulting, CET will be part of Intel’s Tiger Lake lineup of CPUs, which are due later in 2020.
Microsoft’s recent post on Hardware-Enforced Stack Protection indicates that the feature requires a Windows 10 Insider Preview build on the Fast Ring. But Shafir and Ionescu say that work started on this feature in Windows 10 version 1903. And that more work is being completed in every new Windows 10 release.
Windows 10 version 2004, due in spring 2020, should include support for the User Mode Shadow Stack features of CET. That is to say that Hardware-Enforced Stack Protection will only protect code running in user mode, and not in kernel mode, on Windows 10 version 2004.
There should be more posts from the kernel protection team arriving in the coming months explaining how to rebuild Windows 10 apps for compliance with shadow stacks. And the team will provide more information on best practices and deeper technical documentation.