Deploy a Read Only Domain Controller
In today’s Ask the Admin, I’ll show you how to deploy a Windows Server 2012 R2 Read Only Domain Controller (RODC).
Read Only Domain Controllers were introduced in Windows Server 2008 as a response to the security risks of placing DCs in branch office locations that lack the physical security of centralized datacenters. Hosting read-only copies of the Active Directory (AD) database partitions, SYSVOL folder, and optionally the DNS database, RODCs can limit the damage caused if the server is compromised. The AD database is replicated from a writeable DC to each RODC, but not vice versa, so even if an RODC is hacked, global changes cannot be made to Active Directory.
RODCs communicate with a writeable DC for user authentication because they don’t store account credentials locally, although you can elect accounts to have their passwords cached on a RODC for fast logons, which is useful for regular users of a branch office network. To protect privileged AD accounts, there’s also a deny list to prevent local password caching. Administrator role separation also gives local administrator access to an RODC but without any access to AD.
While RODCs provide several security advantages over writeable DCs, it’s worth bearing in mind that not all applications are compatible with RODCs. So it’s important to check that server applications are compatible and that you test thoroughly before deploying RODCs in a production environment.
Install an RODC
An RODC can’t be the first domain controller in a domain, so you must have at least one writeable DC online. The good news is that the installation process doesn’t differ much from installing a writeable DC, for which you can find the instructions in Add Windows Server 2012 as a Domain Controller on the Petri IT Knowledgebase.
I’m not going to outline the entire process here again, but just the differences when choosing to install an RODC.
Using Server Manager
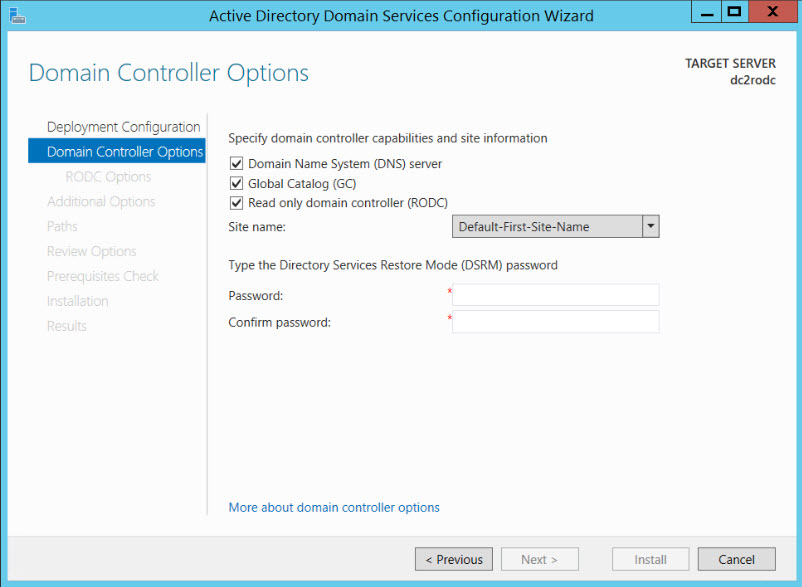
After having installed the AD Directory Services bits, when promoting the server to a DC, make sure you check Read only domain controller (RODC) on the Domain Controller Options screen before proceeding.
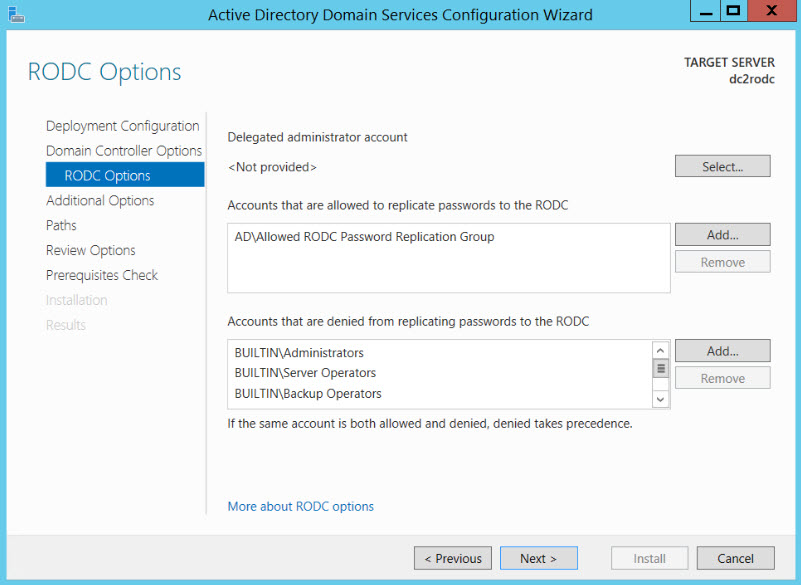
Once you’ve opted to install an RODC, you get an additional page with RODC-specific settings. On the RODC Options screen, you have the chance to nominate an account for local administrator access to this RODC only, something you can’t achieve with a writeable DC, and decide which accounts can have their credentials cached locally for fast logins. There’s a default list of accounts already added to the deny list, but you can add your own. Denies override allows.
Then you continue to install the DC as normal.
Using PowerShell
We need to set a few parameters before starting, including the NetBIOS name and fully qualified domain name (FQDN) for the existing AD domain, and the NTDS and SYSVOL paths.
$domain = 'AD' $domainName = 'ad.contoso.com' $NTDSpath = 'C:\Windows\NTDS' $SYSVOLpath = 'C:\Windows\SYSVOL'
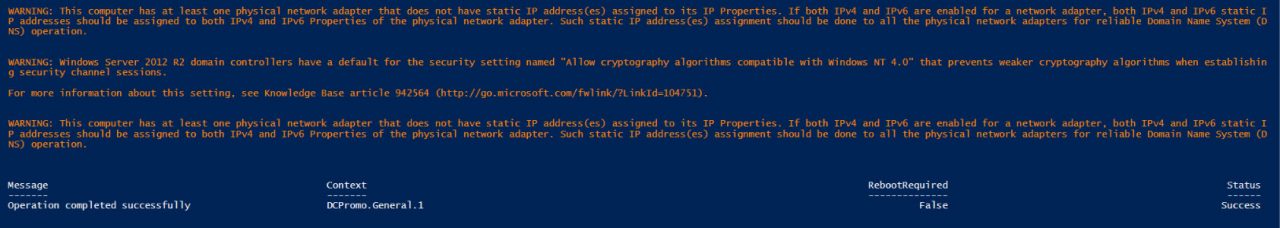
We’ll use the Install-WindowsFeature cmdlet to install the ADDS bits along with the AD management tools. Finally, the Install-ADDSDomainController cmdlet is used to install the RODC. Note the ReadOnlyReplica parameter is set to true, which designates this DC as a RODC. You’ll be prompted to enter the credentials for an account that has permission to add a DC to the domain, and to provide and confirm a Directory Services Restore Mode (DSRM) password.
Install-WindowsFeature –Name AD-Domain-Services -includemanagementtools Install-ADDSDomainController -Credential (Get-Credential) -CriticalReplicationOnly:$false -DomainName $domainName -InstallDNS:$true -LogPath $NTDSpath -DatabasePath $NTDSpath -ReadOnlyReplica:$true -SiteName "Default-First-Site-Name" -SYSVOLPath $SYSVOLpath -Force:$true
Optionally you can add the -AllowPasswordReplicationAccountName and -DenyPasswordReplicationAccountName parameters to specify accounts to be added to the allow and deny password caching policy lists. Also the -DelegatedAdministratorAccountName parameter allows you to specify an account that will be delegated local administrator rights to this RODC only.
-DenyPasswordReplicationAccountName @("BUILTIN\Administrators", "BUILTIN\Server Operators", "BUILTIN\Backup Operators", "BUILTIN\Account Operators", "AD\Denied RODC Password Replication Group")
If you exclude the -AllowPasswordReplicationAccountName and -DenyPasswordReplicationAccountName parameters from the cmdlet, the default settings will be used.
In this article, I explained the differences between RODCs and DCs, and how to install an RODC using Server Manager and Windows PowerShell.