Using Microsoft Graph API To Help Admins Quickly Deploy Policies at Scale
At this week’s Ignite conference, Microsoft announced the general availability of Microsoft Graph API support for Azure Active Directory (AD) Conditional Access. Conditional Access is Azure AD’s policy engine, which is used to set granular and adaptive access controls on applications that use Azure AD for identity management. Microsoft says that the new controls will protect users more comprehensively and at scale. In addition to the Microsoft Graph API, insights and recommendations for Conditional Access are now provided in the Azure AD advisor tool.
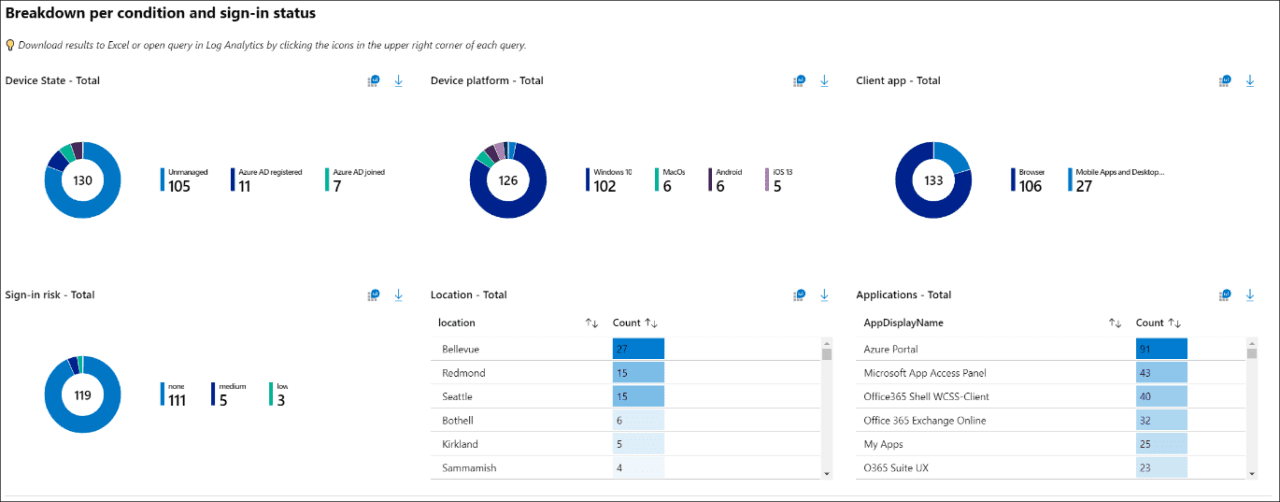
Conditional Access insights and Microsoft Graph API
In a blog post by Corporate Vice President of Microsoft Identity, Joy Chik writes:
Zero Trust principles are at the core of how we build and invest in identity. We never trust, and we always verify. Zero Trust starts with cloud identity, using real-time risk assessment powering fine-grained access controls. Many of you use Azure AD Conditional Access as your Zero Trust policy engine. Now, with Conditional Access insights in public preview, recommendations that identify gaps in your policies help you stay more protected. For example, a common recommendation is to block legacy authentication by default to protect your accounts from malicious authentication requests.
To help simplify configuration, the Azure AD Conditional Access API is now generally available in Microsoft Graph. You can use PowerShell or another custom scripting to automate and scale policy management.
Conditional Access is part of Microsoft’s zero-trust network solution
Conditional Access is part of Microsoft’s zero-trust network solution, a security framework for remote access where the idea is that you shouldn’t trust anyone, not even your own employees. Every person accessing your network must be verified. Policies limit the access employees have to corporate IT resources. Policies should provide just enough access to complete work-related tasks and nothing more. And that’s where Conditional Access comes in.
Users access corporate apps remotely through Azure AD’s Application Proxy. Conditional Access works with Application Proxy to ensure certain conditions are met before access is granted. For example, some conditions might include whether the user’s device is fully patched, whether the device’s IP address is in a defined range, and the user’s group membership.
For more information on the technologies behind Microsoft’s zero-trust solution, check out Choosing between Virtual Private Network and Zero Trust Remote Access Solutions on Petri.
Automating Conditional Access at scale using Microsoft Graph
Microsoft describes Graph as a gateway to data and intelligence in Microsoft 365. Not only is it a unified programmability model for accessing data in Microsoft 365, but also it can be used to manage features. You can find more information on Microsoft’s website here.
There isn’t a PowerShell module specifically for working with Conditional Access. Instead, you need to know how to work with PowerShell and the Graph API. The Microsoft Graph PowerShell SDK makes working with Graph and PowerShell easier. The PowerShell modules included with the SDK are also published in the PowerShell Gallery, so you can install them independently of the SDK.
Conditional Access policies are defined programmatically using JSON and then ‘posted’ to Microsoft Graph. Unfortunately, at the time of writing, there’s no easy way to get the JSON for a policy from the Azure management portal. But you can extract the JSON for existing policies using PowerShell and the Microsoft Graph API.
Microsoft Graph support and Conditional Access insights make it easier to secure users at scale
Tapping into the Microsoft Graph programmatically isn’t as simple as it could be. But Conditional Access insights are at least easy to use. Nevertheless, Microsoft Graph API Conditional Access support is more likely to be used by large organizations that have the resources to make it work without too many problems. And at a time when more users need to work remotely, these two new Conditional Access features will prove useful.