Microsoft Brings Advanced Threat Protection to SharePoint Online
More Anti-Malware Protection for SharePoint Online
Microsoft’s December 5 announcement that Advanced Threat Protection (ATP) is now available for “SharePoint, OneDrive for Business, and Microsoft Teams” generated a lot of excitement. And so it should, because increasing the level of protection against malware infections is always a good thing. And given that more people than ever before are storing files in the cloud, making sure that the bad stuff is detected and stopped in place is sensible.
The Cost of Protection
My excitement faded a little when I read the blog to find that ATP for SharePoint (for that is what this is) requires tenants to buy either Office 365 E5 licenses or separate add-on licenses, Microsoft is steadily increasing the number of features that you can only use if you have E5 grow the average revenue per seat. When you have 120 million active users, Office 365 can drive a lot of extra dollars.
How ATP for SharePoint Works
ATP for SharePoint works differently to ATP for email, which is also part of Office 365 E5. The Exchange Online mail transport service is a single chokepoint where email moving into and out of a tenant must pass through. ATP for email examines inbound messages to detect and remove malware, using techniques like Dynamic Delivery to process potentially suspicious attachments. Overall, ATP works well for email.
But SharePoint does not have a single chokepoint where content can be checked. This is the same problem that the Data Loss Prevention (DLP) team ran into when they wanted to check documents for sensitive data types like credit card numbers or social security numbers. DLP does not try to check every file to detect sensitive data and concentrates instead on preventing users sharing sensitive data when they should not. Likewise, ATP “does not scan every single file.” Instead, ATP scans files asynchronously as users share files to detect possible problems.
Of course, this is a simple description of what is very complex processing. ATP uses other inputs to decide when sharing documents might cause issues, including “smart heuristics” and intelligence about potential threats. The implementation is reasonable because although you might want to scan every file stored in your SharePoint Online and OneDrive for Business sites, such an operation would consume huge resources.
Stopping Malware Spreading
Scanning every file in Office 365 might catch some problematic files, but if those files are in place and doing nothing they cannot do any harm. Problems only happen when people share files with others and spread infection to places where someone might open and activate malicious content.
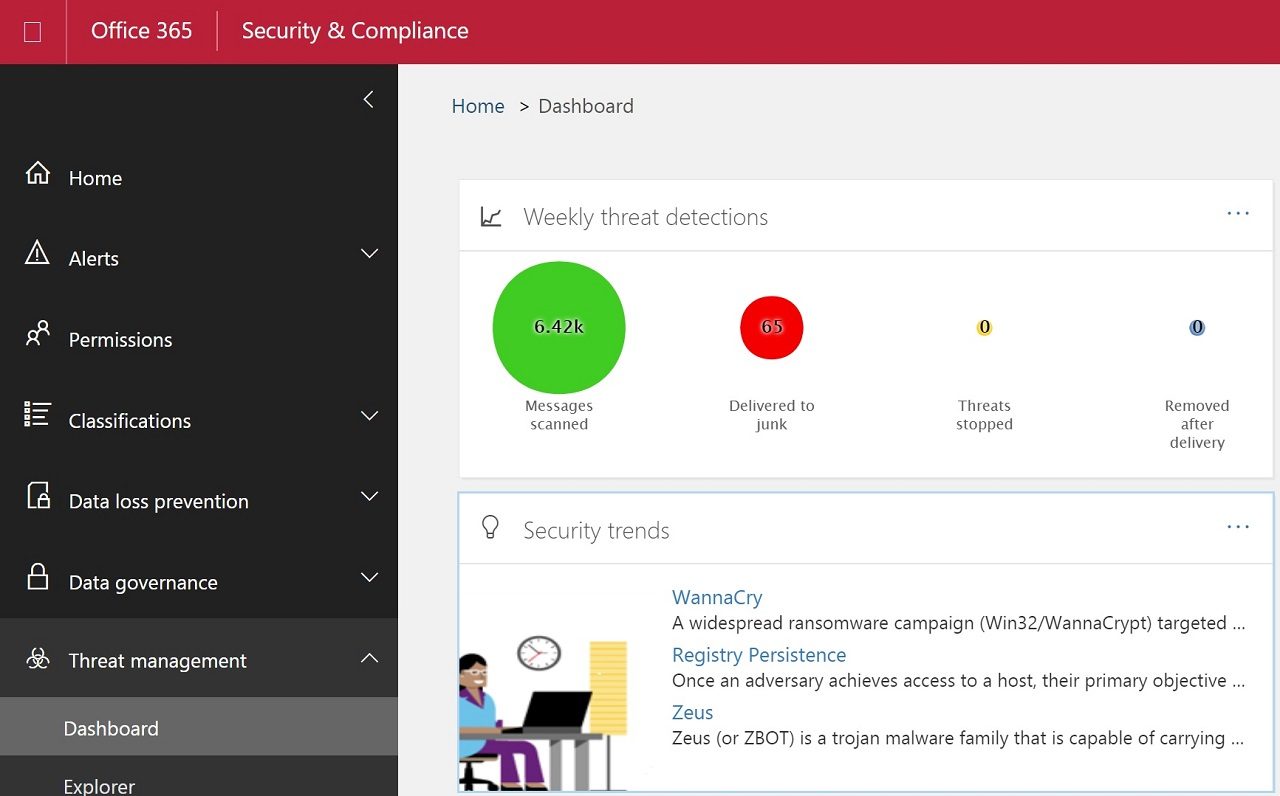
When ATP for SharePoint finds malware in a file, it locks the file and stops users from opening, downloading or sharing it. The file remains in the library and the user can delete it. Administrators can keep an eye on what’s happening with the Threat protection status report in the Security and Compliance Center, where they can see a report of all files detected and blocked by ATP for SharePoint.
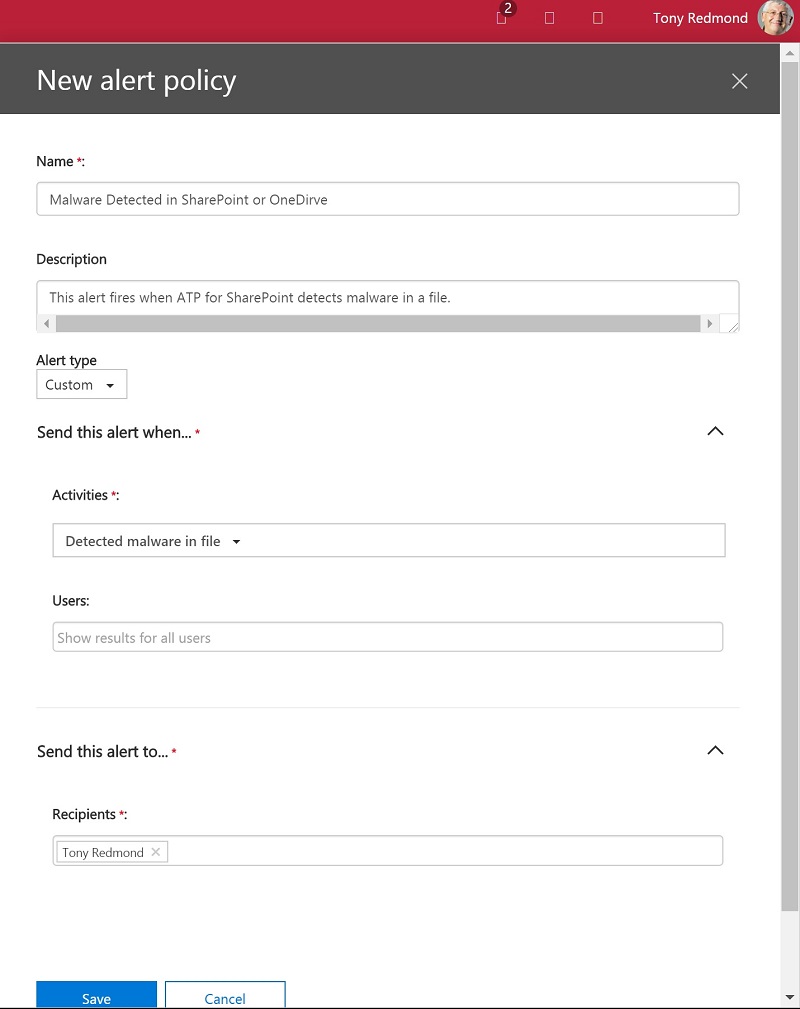
In addition, a new “detected malware in file” audit event is logged by ATP when it detects malware. Like other audit events, you can search the Office 365 audit log to find problems or create an activity alert or activity policy to email you automatically when ATP logs this audit event (Figure 1).
Turning on ATP for SharePoint
Once you have the necessary licenses, enabling ATP for SharePoint is easy. Go to the Security and Compliance Center, open Threat Protection, then Policy, select Safe attachments, and set the checkbox to turn on ATP (Figure 2).
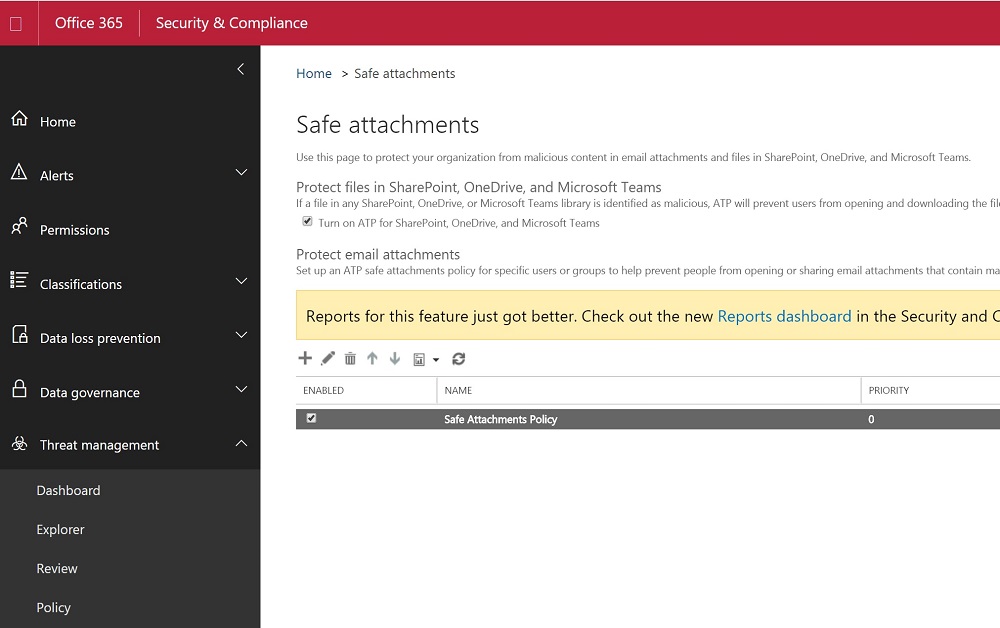
As noted in Microsoft’s instructions, the new policy must be published to all of the datacenters which hold your tenant data. That process can take up to 30 minutes as an Office 365 datacenter region spans multiple datacenter (EMEA, for instance, has four in Helsinki, Dublin, Amsterdam, and Vienna).
Don’t expect a flood of notifications to happen after you enable ATP for SharePoint. Remember that checking centers around file sharing, so you should only expect to see events when people try to share infected content.
ATP for Teams?
Teams is Microsoft’s current poster child application for Office 365, so it is no surprise when marketing tries to include Teams into every announcement. In this case, every team has a SharePoint team site and document library, so every team can store documents, and therefore every team can take advantage of ATP for SharePoint.
It is a tenuous but valid connection. People using teams to store files might not even know that they are using SharePoint, but they are. And because they store attachments and other files in SharePoint, they gain protection when ATP is active. If ATP blocks a suspect file, users cannot download or open that file with Teams.
Protection for a World of Threat
Commenting on ATP, Dana Simberkoff, Chief Risk, Privacy and Information Security Officer at AvePoint said: “It’s important for organizations to implement a layered approach to security. Improperly relying on ATP alone, or any other existing scanning technology, may create a false sense of safety in that most costly breaches come from simple failures, and not from attacker ingenuity.”
I agree. ATP is not a panacea that will suddenly eradicate malware from SharePoint.
The thing about security is that threat evolves all the time. You can’t stay still and expect to remain invulnerable when new threats come along. One of the nice things about using Office 365 is that you gain from the investments Microsoft makes in technologies like ATP. That is, if you can afford the licenses.
Follow Tony on Twitter @12Knocksinna.
Want to know more about how to manage Office 365? Find what you need to know in “Office 365 for IT Pros”, the most comprehensive eBook covering all aspects of Office 365. Available in PDF and EPUB formats (suitable for iBooks) or for Amazon Kindle.