Active Directory Authentication for Azure Files Enters Public Preview
Last month, Microsoft announced Active Directory authentication for Azure Files, which is now in preview. Azure Files lets you create SMB shares for Azure storage accounts. SMB shares can be easily accessed by Windows virtual machines (VM) and physical devices.
A brief history of Azure Files
Unlike SMB file shares you might create in on-premises Windows Server for end-users, Azure Files shares serve a different purpose. At least in the service’s original incarnation. Azure Files was designed for applications that rely on SMB file shares, so the apps could be moved to the cloud without the need to implement Windows Server in a VM. Shares created using Azure Files in its original release didn’t have permissions. An application could either connect or not connect.
Azure File Sync
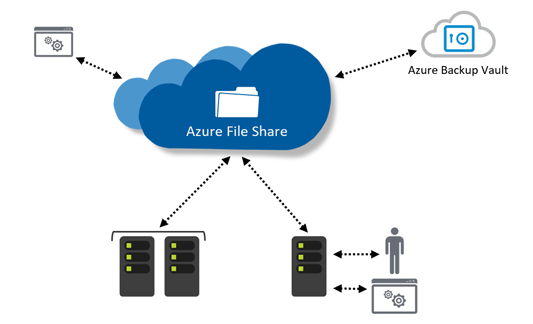
Microsoft has a separate service, which is based on Azure Files, for deploying cloud file shares to end users. It is called Azure File Sync. Azure File Sync lets you synchronize the contents of Windows Server file shares to the Azure cloud. The service changes the role Windows Server plays in an organization so that it acts as a fast-local cache for Azure File Sync. The master of the copy of all files is stored in the cloud. For more information on Azure File Sync, read Azure File Sync is now Generally Available on Petri.
Azure AD DS authentication over SMB
In 2018, Microsoft added the ability to assign permissions to shares created using Azure Files. The feature requires Azure Active Directory (AAD) and Azure Active Directory Domain Services (Azure AD DS). Azure AD authentication over SMB, as the feature is known, is supported in Windows VMs joined to an Azure AD DS domain. To be more precise, it is supported on Azure VMs running Windows 7 or Windows Server 2008 R2, or later versions of these OSes.
Azure AD can be licensed for free, although there are also paid subscription plans. But Azure AD DS is not free. In addition, the workflow for creating a share and assigning permissions involves several steps:
- Enable Azure AD DS authentication over SMB for a storage account to register the storage account with Azure AD DS.
- Assign access permissions for a share to an Azure AD user, group, or service principal.
- Configure NTFS permissions for directories and files.
- Mount an Azure Files share from a domain joined VM.
Active Directory authentication for Azure Files
Active Directory authentication for Azure Files, which is now in preview, builds on Azure AD DS authentication over SMB by letting you mount shares created using Azure Files with Windows Server Active Directory (AD) credentials.
Before using Active Directory authentication for Azure Files, Windows Server AD credentials must be synchronized to Azure Active Directory. Then directory and file level permissions can be managed with standard NTFS access control lists (ACLs) using File Explorer.
The preview introduces three main capabilities to Azure Files:
- Enable Active Directory (AD/AD DS) authentication for server message block (SMB) access.
- Enforce share level, and directory or file level permissions.
- Support file migration from on-premises file servers with ACL persistence over Azure File Sync.
When AD authentication for SMB is enabled, you can mount Azure Files shares from Active Directory domain-joined machines using AD credentials. The machines can be on-premises or hosted in the Azure cloud. AD authentication works on Azure Files shares you create yourself or on those managed by Azure Files Sync. Role-based access control (RBAC) control can be used for share-level permission management. NTFS ACLs can be configured using File Explorer or the command-line icacls tool.
AD authentication for Azure Files supports migration of on-premises Windows Server file shares over Azure Sync while maintaining ACLs. Microsoft says:
Existing files and directories tiered to Azure Files through Azure Files Syncs have ACLs persisted in the native format.
AD authentication for Azure Files will allow organizations to move file shares to the Azure cloud and decommission on-premises servers. Microsoft is also touting AD authentication for Azure Files as useful for storing Virtual Desktop Infrastructure (VDI) user profiles. Most customers run Windows Virtual Desktop (WVD) along with on-premises Active Directory. Therefore, Azure Files can be used for user profile storage without needing a separate domain service for managing access control to shares.
Windows Virtual Desktop (WVD) is Microsoft’s VDI-as-a-Service in the Azure cloud. For more information on WVD, see Getting Started with Windows Virtual Desktop: Understanding Windows Virtual Desktop on Petri.
Microsoft simplifies migrating Windows Server file shares to Azure
Some organizations are keener than others to move their user file shares to the cloud. Reducing the number of on-premises servers can lower costs. But managing storage blobs in Azure comes with its own challenges. Managing Azure cloud storage is more complicated than setting up Windows Server file shares, there is no antimalware protection at the file-share level, and disaster recover isn’t as mature compared to solutions available for Windows Server.
But for organizations that are interested in moving file shares to the cloud, AD authentication for Azure Files is going to make the migration process easier. I will be looking at how to migrate file shares from Windows Server to Azure File Sync using AD authentication for Azure Files in the next few months, so check back soon.



