Preventing Automatic Service Pack 1 Update to Windows 7 and Windows Server 2008 R2
Microsoft began to distribute Windows 7 and Windows Server 2008 R2 Service Pack 1 (SP1) as a high-priority update through Automatic Updates. However, as with most large corporate environments, IT organizations may want to delay the introduction of a new Service Pack until they have tested compatibility with internal applications and sites.
Microsoft created a tool called “Windows Service Pack Blocker Tool Kit” to stop it from updating your servers and workstations without your permission. Unlike the Blocker Toolkit for IE9, this tool does have an expiration date – the 22nd of February 2012. The tool and can be configured either by running the registry file on the client machines or through Group Policy in domain joined environments.
Download
Download details: www.microsoft.com/downloads/en/details.aspx?FamilyID=D7C9A07A-5267-4BD6-87D0-E2A72099EDB7
The tool can be used with:
- Windows 7 Service Pack 1
- Windows Server 2008 R2 Service Pack 1
Toolkit Components
The tool contains three components. All of them function primarily to set or clear a specific registry key that is used to detect and block download of Service Packs from Windows Update. You need to only use one of the components, the one that best serves your organization’s computer management infrastructure.
The components are:
- A Microsoft-signed executable
- A script
- An ADM template
Registry key
The executable creates a registry key on the computer on which it is runs that blocks or unblocks (depending on the command-line option used) the delivery of a Service Pack to that computer through Windows Update. The key used is HKLM\Software\Policies\Microsoft\Windows\WindowsUpdate.
Key value name: DoNotAllowSP
- When the key value name is not defined, distribution is not blocked.
- When the key value name is set to 0, distribution is not blocked.
- When the key value name is set to 1, distribution is blocked.
Blocker Script
The script does the same thing as the executable, but allows you to specify the remote machine name on which to block or unblock delivery of Service Packs.
When the ‘/B’ command line option is used, the key value name ‘DoNotAllowSP‘ is created and its value set to 1. This value blocks delivery of a Service Pack to the computer through Automatic Update or Windows Update.
When the ‘/U’ command line option is used, the previously created registry value that temporarily blocked the delivery of a Service Pack to the computer through Automatic Update or Windows Update is removed. If the value does not exist on the computer on which it is run, no action is taken.
Note: The executable and script have been tested only as a command-line tool and not in conjunction with other systems management tools or remote execution mechanisms.
Group Policy Administrative Template (.ADM file)
The ADM template allows administrators to import group policy settings to block or unblock delivery of Service Packs into their Group Policy environment. Administrators can then use Group Policy to centrally execute the action across systems in their environment.
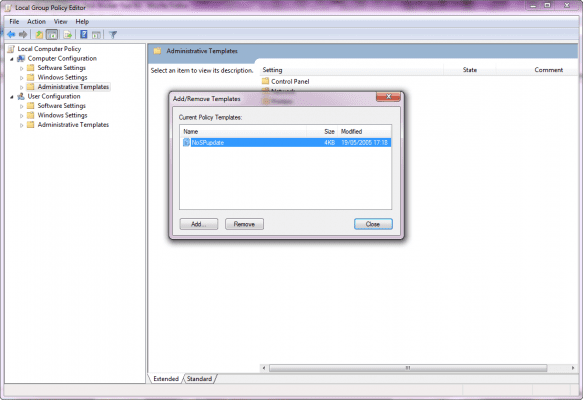
Add the .ADM file to the Group Policy by going to Computer Configuration > Administrative Templates. Right click and select Add/Remote Templates. Browse to the location of the .ADM file and click Ok.
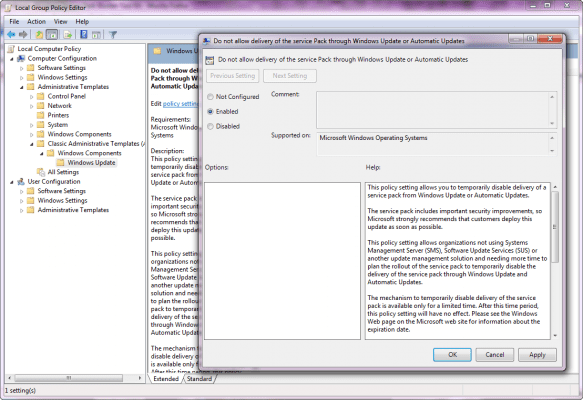
Users running Windows 7 and Windows Server 2008 R2 will see the policy setting under Computer Configuration > Administrative Templates > Classic Administrative Templates (ADM) > Windows Components > Windows Update.
Please note that this toolkit will not prevent the installation of the service pack from CD/DVD, or from the stand-alone download package. This simply prevents Windows 7 and Windows Server 2008 R2 Service Pack 1 (SP1) from being delivered over Windows Update.